USB Disk Security is a type of software designed to protect USB flash drives and other removable storage devices from security threats. It scans USB drives for malware, offers real-time protection, and may include features like USB drive immunization, data encryption, and password protection. Its significance lies in safeguarding valuable data on USB drives, preventing malware distribution, and thwarting unauthorized access. Potential threats include data loss, malware distribution, and data theft.
Understanding USB Disk Security
USB Disk Security is a type of software or security solution designed to protect USB flash drives and other removable storage devices from various security threats. It is primarily used to safeguard the data on USB drives and prevent the spread of malware through these devices.
Key Functions And Features Of USB Disk Security:
- Malware Detection and Removal: USB Disk Security scans USB drives for any malware, such as viruses, trojans, worms, spyware, and adware. If it detects any malicious files, it isolates or removes them to prevent them from infecting the computer.
- Real-time Protection: Many USB disk security programs offer real-time protection, meaning they monitor USB drives as soon as they are connected to the computer. This proactive approach helps prevent malware from entering the system via the USB drive.
- USB Drive Immunization: Some USB security software can immunize or vaccinate your USB drives. This means it adds protective measures to the drive to prevent common types of malware from automatically executing when the drive is connected to a computer.
- Data Encryption: USB Disk Security may include encryption features, allowing you to encrypt the data stored on your USB drives. This ensures that even if the drive is lost or stolen, the data remains secure and inaccessible without the encryption key.
- Password Protection: Some solutions offer password protection for USB drives. This feature requires users to enter a password before they can access the contents of the drive, adding an extra layer of security.
- Whitelist and Blacklist: USB security software often includes the ability to create whitelists (trusted devices) and blacklists (blocked or suspicious devices). This lets users specify which USB drives are allowed to connect to their computer.
- Automatic Scanning: USB Disk Security can be set to automatically scan any connected USB drive when it’s inserted into the computer. This helps ensure that no malware goes undetected.
- Logs and Reporting: Many USB security solutions maintain logs of all USB drive-related activities, including scans and threat detections. This information can be valuable for monitoring and auditing purposes.
Understanding the Significance of USB Disk Security

The primary reason for emphasizing USB disk security is the need to protect valuable data. USB drives frequently contain sensitive information, including personal documents, financial records, and business-related files. Inadequate security measures can lead to data breaches through various means:
USB drives are susceptible to physical loss or theft. Misplacing a USB drive or having it stolen can result in the loss of critical data. This can have severe consequences for both individuals and organizations.
2. Malware Distribution
When connected to an infected computer, USB disk can easily become carriers of viruses, trojans, or other malicious software. Subsequently, when inserted into another computer, they can introduce these threats, compromising the security of the new host system.
3. Unauthorized Access
Lost or stolen USB drives can lead to unauthorized access to your data. Without proper security measures in place, anyone who finds the drive can potentially access, copy, or misuse your files. This can result in privacy breaches, identity theft, or corporate espionage.
Realizing the Threat Landscape:
1. Malicious Software
USB drives can inadvertently carry malware from one computer to another. When connected to a compromised system, they can introduce viruses and other malicious software, leading to data corruption and system compromise.
2. Data Theft
Imagine the consequences of losing a USB drive containing sensitive corporate data or personal information. If this data falls into the wrong hands, it can be exploited for identity theft, financial fraud, or competitive advantage in business.
3. Ransomware Attacks
Ransomware attacks frequently commence with an infected USB drive. Once malware infiltrates your system, it can encrypt your files and demand a ransom for decryption. Without a secure USB drive, you might unknowingly become a victim of such an attack.
4. AutoRun Exploits
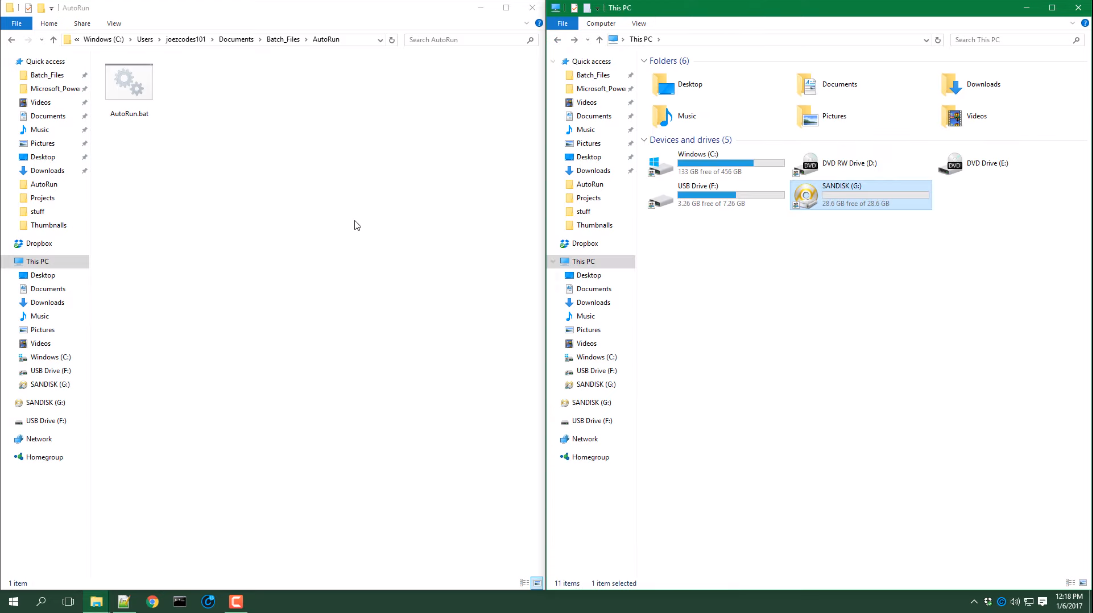
AutoRun exploits take advantage of the AutoRun feature in Windows. When you insert a USB disk, malware can automatically execute, infecting your computer without your knowledge.
5. Malicious Files
USB disks can contain files with malicious code. These files can infect your system when opened or executed.
Best Practices for USB Disk Security:
1. Use Reliable Antivirus Software
Invest in reputable antivirus software that offers real-time protection against malware. Ensure it includes USB disk scanning to detect and remove any threats automatically.
2. Enable USB Disk Encryption
Encryption is a powerful tool to protect your data. By encrypting your USB drive, you make it nearly impossible for unauthorized users to access the information stored on it. Windows and macOS both offer built-in encryption tools, so take advantage of them.
3. Disable AutoRun
Disable the AutoRun feature on your computer to prevent malware from executing automatically when you insert a USB disk. This can be done through your computer’s settings.
4. Keep Your USB Disks Secure
Physically protect your USB disks. Store them in a safe place when not in use, and avoid lending them to others unless necessary. This reduces the risk of data theft.
5. Regularly Update Your Software
Keep your operating system, antivirus software, and all applications up-to-date. Updates often include security patches that address vulnerabilities.
6. Be Cautious with Unknown Drives
Avoid plugging unknown USB drives into your computer. Cybercriminals often use “lost” or intentionally placed infected drives to compromise unsuspecting users. If you find a stray USB drive, it’s best to report it to the appropriate authorities.
Data Recovery and Backup:
Despite all precautions, accidents can happen. You may lose your USB disk or accidentally delete important data. In such cases, having a data recovery and backup plan is crucial:
Data Recovery Software
Invest in data recovery software that can help you retrieve lost or deleted files from your USB disk. These tools can be a lifesaver when data loss occurs.
Cloud Backup Services
Consider using cloud backup services to sync your USB disk’s contents to the cloud automatically. This ensures that even if you lose your USB disk, your data remains safe and accessible.
What software enhances USB Disk security?
1. Antivirus Software
Antivirus software, such as Avast, Norton, or Bitdefender, plays a crucial role in USB disk security. These programs continuously scan your USB drives and your computer for malware and viruses. They can detect and remove threats that may have been introduced through USB drives, preventing them from compromising your data and system.
2. USB Disk Encryption Tools
USB disk encryption tools like VeraCrypt or BitLocker (Windows) allow you to encrypt the entire USB drive or specific folders and files. Encryption converts your data into an unreadable format without the encryption key. Even if your USB drive is lost or stolen, the data remains inaccessible to unauthorized users.
3. USB Access Control Software
USB access control software, such as USB Disk Manager or USB Secure, enables you to control who can access your USB drives. You can set permissions to restrict access based on specific criteria, including password protection, device whitelisting, or time-based access. This helps prevent unauthorized access to your USB drives.
4. USB Monitoring and Auditing Tools
USB monitoring and auditing tools like USBLogView or Endpoint Protector allow you to monitor the activity on your USB drives. These tools can log when and how USB drives are used, helping you identify suspicious activities and potential security breaches.
5. Password Managers
Password managers like LastPass or Dashlane can help you generate and store strong, unique passwords for your USB drives. Using strong passwords adds an additional layer of security, especially when your USB drive supports password protection.
6. Device Control Software
Device control software, often provided by endpoint security solutions like Symantec or McAfee, allows you to manage and control USB device usage within your organization. You can enforce policies that specify which USB drives can be used and monitor their activity to prevent data breaches.
Some USB drives come with built-in security features, including fingerprint scanners or PIN protection. These drives provide an additional layer of hardware-based security to prevent unauthorized access.
Conclusion:
USB disk security is a critical aspect of safeguarding our valuable data and protecting our systems from the ever-present threats posed by malware and data breaches. USB drives can become carriers of malicious software or expose sensitive information to unauthorized access if not adequately secured. By understanding the significance of USB disk security, recognizing the potential threats, and adopting best practices such as using reliable antivirus software, enabling USB disk encryption, and exercising caution with unknown drives, individuals and organizations can greatly enhance their data protection efforts. Incorporating security software, monitoring tools, and secure USB drives into your strategy can further fortify your defenses against the evolving landscape of cybersecurity threats.
FAQs:
What is USB drive encryption, and why should I use it?
USB drive encryption is the process of encoding the data on your USB drive so that it can only be accessed with the correct decryption key or password. You should use it to ensure that even if your USB drive is lost or stolen, the data remains confidential and secure.
Can I password-protect my USB drive?
Yes, many USB drives support password protection. You can set a strong, unique password to prevent unauthorized access to the drive’s contents. It’s a recommended security measure for sensitive data.
How often should I back up the data on my USB drive?
Depending on how frequently your data changes, you should consider backing up your USB drive at least once a week or more often for critical data. Storing backups in a remote, secure location is also advisable.
What should I do if I suspect my USB drive has been compromised?
If you suspect your USB drive has been compromised, immediately disconnect it from your computer and run a thorough malware scan. If sensitive data was on the drive, change any related passwords and notify the appropriate authorities or IT department if it’s a corporate device.
Can USB disk security measures impact the usability of the drive?
While some security measures, such as encryption and password protection, may add an extra step to access your USB drive, the impact on usability is generally minimal. The added security far outweighs any minor inconvenience.
