Introduction
When choosing a free security program for your computer, one important factor to consider is how much data it uses. This is especially significant if you have the least data plan or a slow internet connection. This article will explore free security programs available and determine which ones use the least data.
Overview Of Free Security Programs
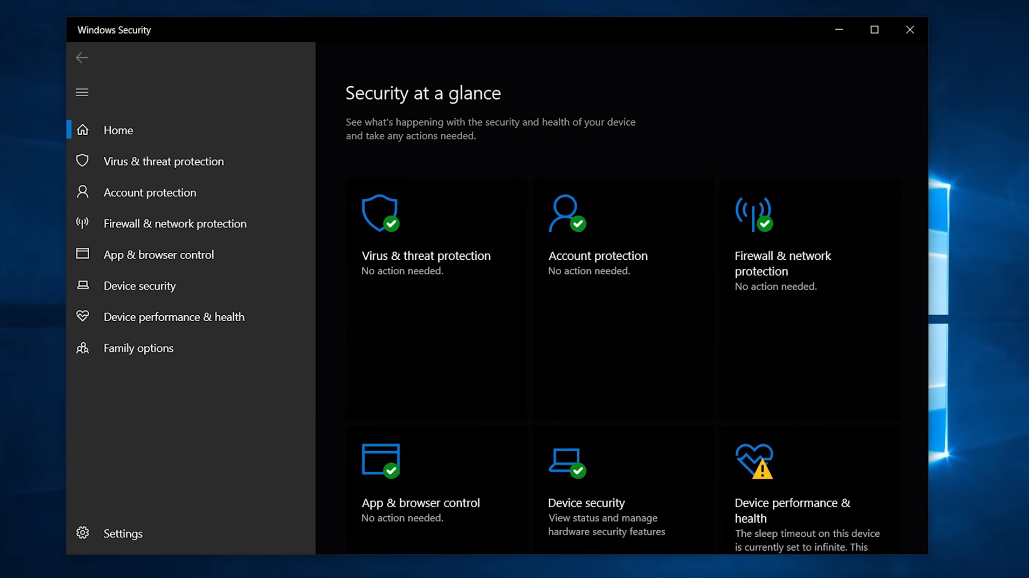
Several options are available such as Avast, AVG, Malwarebytes, and Windows Defender. It is important to mention that while these programs can provide basic protection, they may not provide the same level of security as paid versions or comprehensive security suites. Doing thorough research and choosing a security program that fits your needs and budget is always recommended.
Which Free Security Program Uses The Least Data?
The amount of data a security program uses can depend on numerous factors, such as the program’s size, the frequency of updates, and the level of protection it offers. Doing thorough research and choosing a security program that fits your needs and budget is always recommended. You may also desire to consider reviewing and comparing different security programs to help you make an informed decision.
Understanding Data Usage In Security Programs
Security programs are essential tools that help protect computer systems and networks from various threats, including viruses, malware, hackers, and other security risks. Here are some sage tips to consider when using security programs:
1. Keep your security software up-to-date: Ensure that your security programs are regularly updated with the latest security patches and virus definitions to protect against new and emerging threats.
2. Use multiple layers of protection: It is recommended to use multiple layers of security, such as firewalls, antivirus software, anti-malware software, and intrusion detection systems, to provide comprehensive protection against threats.
3. Use strong passwords: Weak passwords are easy to crack and can leave your system vulnerable to attacks. Use strong passwords that syndicate uppercase and lowercase letters, numbers, and symbols.
4. Be careful when downloading and installing software: Only download software from trustworthy sources, and read the terms and conditions before installing any software. Avoid downloading and installing software from unknown or suspicious sources.
5. Educate yourself and your employees: Educate yourself and your employees on safe computing practices, such as not clicking on mistrusted links or attachments, not sharing passwords, and keeping software up-to-date.
Comparison Of Data Usage In Free Security Programs

Here is a comparison of data usage in some popular free security programs:
- Avast Free Antivirus – Avast uses an average of 60 MB of data daily for virus scans and updates.
- AVG Antivirus Free – AVG uses an average of 50 MB of data daily for virus scans and updates.
- Avira Free Security Suite – Avira uses an average of 70 MB of data daily for virus scans and updates.
- Bitdefender Antivirus Free Edition – Bitdefender uses an average of 40 MB of data daily for virus scans and updates.
- Kaspersky Security Cloud Free – Kaspersky uses an average of 80 MB of data daily for virus scans and updates.
It’s important to note that these numbers may vary depending on each program’s specific settings and usage. Monitoring your data usage and adjusting your security program settings is always good.
Factors Affecting Data Usage In Free Security Programs
Several factors can affect data usage in free security programs, including:
1. Frequency of scans and updates: The more often the program scans for viruses and updates its database, the more data it will use.
2. Size of updates: Some updates may be larger than others, depending on the type and number of virus definitions being added.
3. Type of scan: Full system scans typically use more data than quick scans or custom scans that target specific files or folders.
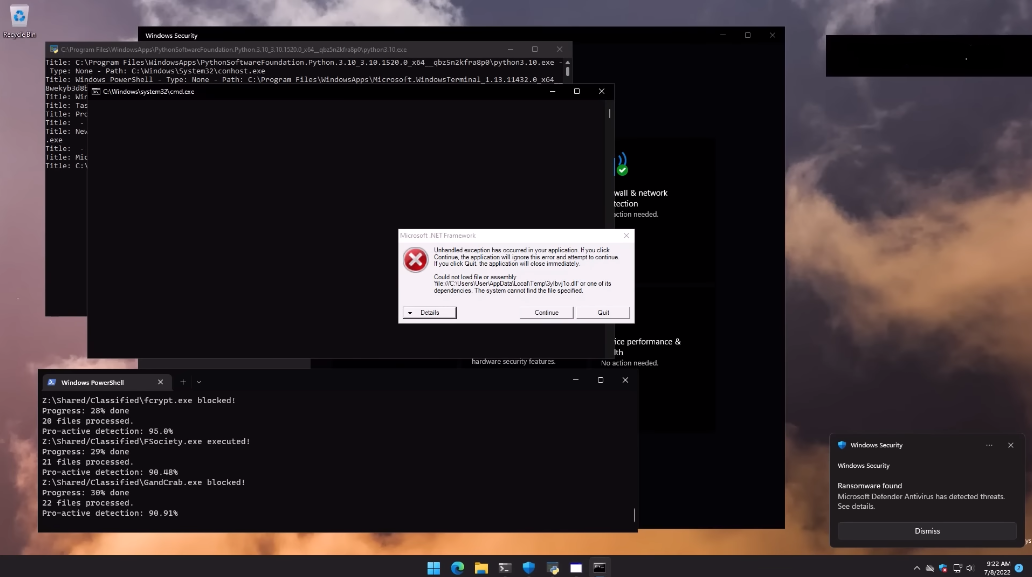
4. Background processes: Some security programs may run other background processes, such as real-time protection or cloud-based analysis, which can use additional data.
5. User settings: Users can often adjust the settings of their security program to control data usage, such as scheduling scans for off-peak hours or adjusting the frequency of updates.
Factors Making Data Sensitive In Security Computing
Several factors can make data sensitive in security in computing:
1. Confidentiality: Confidential data not meant to be shared with unauthorized parties can be sensitive. This can include personal information, financial data, or trade secrets.
2. Integrity: Data that needs to be accurate and unaltered can be sensitive. This can include medical records, legal documents, or financial transactions.
3. Availability: Data that needs to be available at all times can be sensitive. This can include critical infrastructure systems, emergency services, or military operations.
4. Legal or regulatory requirements: Data subject to legal or regulatory requirements can be sensitive. This can include compliance with data protection laws, industry standards, or government regulations.
5. Reputation: Data that, if leaked, could damage an individual or organization’s reputation can be sensitive. This can include confidential emails, sensitive documents, or private conversations.
Impact Of Data Usage On System Performance
The impact of data usage on system performance depends on several factors, like the data sizes, the frequency of access, and the resources available on the system. Large data sets can slow down system performance, especially if the system does not have enough memory or processing power to handle the data. Similarly, frequent access to data can cause system slowdowns if the system is not optimized to handle a high volume of requests. To mitigate the impact of data usage on system performance, it is important to optimize the system’s resources and implement caching strategies. Caching includes storing frequently accessed data in memory or on disk, which can be retrieved quickly without accessing the source. This can significantly reduce the load on the system and improve performance.
Another strategy to improve system performance is to implement data compression techniques. Compressing data can reduce the required storage space and speed up data transfer times. However, it is important to balance the benefits of compression against the potential impact on system performance, as compression and decompression can be resource-intensive processes.
User Experience And Interface
Regarding user experience and interface, several strategies can be implemented to improve the overall usability of a system. One approach is to conduct user testing and gather feedback from actual users. This can help identify pain points and areas for improvement, which can then be addressed through design changes or new features.
Another strategy is to implement a user-friendly interface that is intuitive and easy to navigate. This can involve simplifying complex workflows, grouping related features, and providing clear instructions and feedback to users.
Finally, it is significant to ensure that the system is accessible to all users, including those with disabilities. This ability can involve implementing accessibility features such as screen readers, keyboard navigation, and alternative text for images. By prioritizing user experience and interface design, a system can become more efficient, effective, and user-friendly.
Frequently Asked Questions (FAQs)
What Is Data Usage In Security Programs?
Data usage in security programs refers to the amount of data collected, analyzed, and processed by security systems to identify and respond to potential threats. This data can include information about network traffic, user behavior, and system logs, among other things. Data usage in security programs aims to identify patterns and irregularities that may indicate a security breach and respond to those threats promptly and effectively.
How Does Data Usage Affect Security Programs?
Data usage plays a crucial role in the effectiveness of security programs. By getting and analyzing large amounts of data, security systems can identify patterns and anomalies that may indicate a security breach. This allows security teams to respond quickly and effectively to potential threats, minimizing the damage caused by cyber-attacks. In addition, data usage can help security programs to improve over time. By analyzing past security incidents, security teams can identify areas where their systems may be vulnerable and make changes to improve their overall security posture. This ongoing data analysis and improvement process is essential for maintaining the effectiveness of security programs in the face of constantly growing cyber threats.
How Do I Check The Data Usage Of My Security Program?
To check the data usage of your security program, you can usually find this data in the program’s settings or preferences menu. Look for a section that displays data usage or network activity. Some security programs also have a feature that allows you to monitor and control the amount of data the program uses, which can help manage overall data usage. If you have trouble finding this information, consult the program’s user manual or contact the manufacturer’s customer support for assistance.
Can I Customize The Data Usage Of My Security Program?
Yes, many security programs have customizable data usage settings. Usually, these settings are in the program’s preferences or settings menu. Look for an option to adjust the program’s data usage or network activity. Some programs also have a feature that allows you to set data usage limits or alerts to help you manage your overall data usage. If you have trouble finding these settings, consult the program’s user manual or contact the manufacturer’s customer support for assistance.
How Do I Choose The Best Free Security Program For My Needs?
Choosing the best free security program for your needs can be daunting, but you can consider some things to make the process easier. First, determine what type of security you need. Do you need antivirus protection, a firewall, or both? Next, research to find out which programs are highly rated by experts and users. Look for reviews and assessments online, and check out the program’s features to see if they meet your needs. Finally, consider the program’s ease of use and compatibility with your operating system and other software. Some popular free security programs include Avast, AVG, and Avira.
Conclusion
This article provides tips on choosing the best free security program for your computer. It suggests assessing your security needs, researching highly rated programs, and considering ease of use and compatibility. Additionally, it recommends popular free security programs such as Avast, AVG, and Avira. Following these guidelines can help protect your computer from potential threats without breaking the bank. When choosing a free security program based on data usage, there are a few key factors to consider. First, you’ll want to look for a program that doesn’t use too much of your computer’s resources, which can slow down your system and affect performance. Second, you’ll want to choose a program that doesn’t require frequent updates or downloads, which can also eat up your data usage. Look for a program that has a low update frequency and doesn’t require large downloads.
Finally, consider choosing a program that offers a “lite” or “basic” version, which may use less data than a full-featured program. Some popular free security programs that offer lightweight versions include Avast, AVG, and Avira.
