Introduction
Data breaches have become common in business and can devastate client privacy. When a company’s sensitive information is compromised, it not only puts the company at risk but also jeopardizes the trust that clients have in the business. This situation can lead to a loss of business and a tarnished reputation. In this article, we will explore the effect of data breaches on client privacy within businesses and discuss ways to prevent them from happening.
Understanding Data Breaches
A data breach is a sensitive information that an unauthorized individual or group can access, steal, or expose. This data breach can happen through various means, such as hacking, phishing, or physical theft of sensitive data devices. Data breaches can occur in any industry, including healthcare, finance, retail, and government agencies. The results of a data breach can be severe, including financial losses, legal penalties, and damage to a company’s reputation and client trust.
Types Of Data Breaches
There are several types of data breaches, including:
1. Phishing attacks: These fraudulent emails trick users into providing sensitive information, like login credentials or credit card numbers.
2. Malware attacks: Malware is malicious software designed to steal or damage data. It can infect computers through email attachments, downloads, or infected websites.
3. Physical theft occurs when a device containing sensitive data, such as a laptop or smartphone, is stolen.
4. Insider threats are breaches caused by employees or contractors who have access to sensitive data and intentionally or unintentionally leak it.
5. Social engineering: This attack is where hackers manipulate individuals into divulging sensitive information through psychological manipulation or deception.
6. Unsecured networks: These networks lack proper security measures, making them vulnerable to attacks from hackers.
7. Denial of service (DOS) attacks: These are attacks that overwhelm a system or network with traffic, causing it to smash and become unavailable to users.
8. Malware is malicious software designed to harm or exploit a computer system or network.
9. Phishing: This type of social engineering attack where hackers send fraudulent emails or messages to coax individuals into revealing sensitive information or clicking on malicious links.
10. Insider threats: These come from within an organization, such as employees who have access to sensitive data and intentionally or unintentionally leak it.
Causes Of Data Breaches
Data breaches can be caused by a variety of factors, including:
1. Weak passwords: If passwords are easy to guess or are reused across multiple accounts, it makes it easier for hackers to get access to sensitive information.
2. Unpatched software: If the software is not updated regularly, it can contain vulnerabilities that hackers can exploit.
3. Human error: Accidental data breaches can occur when employees make mistakes, such as sending sensitive information to the wrong person or leaving a device containing sensitive data.
4. Phishing attacks: Cybercriminals can trick individuals into giving away sensitive information through fake emails or websites.
5. Malware: Malicious software can be installed on a device without the user’s knowledge, allowing hackers to access sensitive information.
6. Insider threats: Employees or contractors with access to sensitive information can intentionally or unintentionally cause a data breach.
7. Lack of encryption: Hackers can easily intercept and read sensitive information without proper encryption.
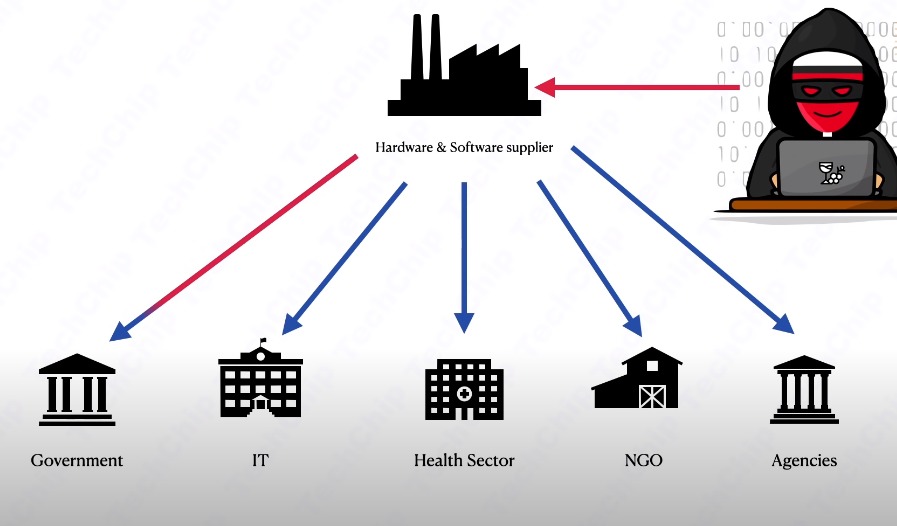
8. Third-party vulnerabilities:
Third-party vulnerabilities: Hackers can exploit vulnerabilities in third-party software or services used by a company to gain access to sensitive information. It is important to regularly update and patch all software and services to minimize the risk of these attacks.
Effects Of Data Breaches On Client Privacy
Data breaches can have an important impact on client privacy. When personal information is exposed, clients may experience identity theft, financial loss, and other negative results. In addition, clients may lose trust in the organization that experienced the breach, which can lead to reputational damage and a loss of business. For example, suppose a healthcare organization experiences a data breach that exposes patient records. In that case, those patients may risk using their personal information for fraud, such as opening credit accounts or applying for loans.
Another example of the negative consequences of a data breach can be seen in the case of a retail company that experiences a breach of customer credit card information. This breach can lead to financial loss for both the customers and the company, as the customers may have to deal with unauthorized charges and face legal action or fines for failing to protect customer data. To prevent data breaches, organizations can take steps such as implementing strong cybersecurity measures, regularly updating software and systems, and providing employee training on data security best practices. It is also important for companies to conform to industry regulations and standards, such as the Payment Card Industry Data Security Standard (PCI DSS). In a data breach, the company should quickly mitigate the damage and notify affected customers. This act may involve offering credit monitoring services or reimbursing customers for unauthorized charges. The company should also conduct a thorough investigation to identify the cause of the breach and take steps to prevent similar incidents.
Impact Of Data Breaches On Client Privacy Within The Business
Data breaches can have a significant influence on client privacy within a business. When sensitive information such as names, addresses, phone numbers, email addresses, and financial data is compromised, it can lead to identity theft, fraud, and other types of cybercrime. Clients may lose trust in the business and may choose to take their business elsewhere. The business may also face legal and financial consequences, including fines, lawsuits, and damage to its reputation. It can also lead to a loss in revenue and increased security costs. Businesses should follow robust security measures to prevent such incidents as encryption, firewalls, and regular software updates. They should also provide cybersecurity training to employees and enforce strict policies regarding handling sensitive information.
Additionally, businesses should have a response plan in place in case of a data breach. This plan should include steps to contain the breach, notify affected clients, and work with law enforcement and cybersecurity experts to investigate and resolve the issue.
By prioritizing client privacy and implementing strong security measures, businesses can build trust with their clients and protect themselves from costly breaches. It’s important for businesses to regularly assess their security protocols and make updates as needed to stay ahead of emerging threats.
Businesses And Data Breaches

Unfortunately, businesses and data breaches are becoming increasingly common in today’s digital age. A data breach arises when sensitive or confidential information is accessed, stolen, or released without authorization. This breach can include personal information such as names, addresses, social security numbers, and credit card numbers. Data breaches can have grave consequences for businesses, including loss of customer trust, damage to reputation, financial losses, and legal repercussions. In addition, businesses may face regulatory fines and pen their customers’ data. Businesses can take several measures to prevent data breaches, including implementing strong passwords, using encryption to protect sensitive data, regularly updating software and security systems, and educating employees on proper security protocols. It’s also significant for businesses to have a response plan in place if a breach occurs, including notifying affected individuals and authorities and taking steps to mitigate the damage.
Several legal and financial implications exist for businesses that experience a data breach. Depending on the kind of breach and the compromised data type, businesses may be subject to fines and penalties under various data protection laws. In addition, affected individuals may sue the business for damages, which can be costly in terms of legal fees and settlements. The charge of a data breach can also be significant in terms of lost revenue and damage to the business’s reputation. Customers may lose trust in the business and take it to another place, resulting in a loss of revenue. The business may also incur costs associated with investigating the breach, notifying affected individuals, and implementing measures to prevent future breaches. Businesses need to take proactive steps to avert data breaches from happening in the first place. The steps can include implementing strong security measures, such as firewalls and encryption, regularly training employees on data protection best practices, and conducting regular security audits and vulnerability assessments.
Businesses should take immediate action in a data breach to contain and minimize its impact. The action may involve isolating affected systems, shutting down compromised accounts, and changing passwords and access credentials. Businesses should notify affected individuals as soon as possible and provide them with information on what data was compromised and what steps they can take to protect themselves. It is also important for businesses to work closely with law enforcement and regulatory authorities to investigate the breach and comply with any legal requirements for reporting and remediation. Finally, businesses should thoroughly review their security measures and make necessary improvements to prevent future breaches. In addition to these immediate steps, businesses should also consider implementing proactive measures to prevent data breaches from occurring in the first place. The steps can include regular security audits, employee training on best practices for data protection, and the use of advanced security technologies such as encryption and multi-factor authentication.
Data breaches can significantly impact a business’s reputation and customer trust. In addition to the financial costs of dealing with a breach, businesses may also experience a loss of customers and damage to their brand image. Businesses should be transparent and timely in communicating with customers about the incident to mitigate the reputational damage caused by a breach. This communication includes information on what data was compromised, how to address the issue, and how customers can protect themselves.
Businesses should also take proactive measures to thwart data breaches from occurring in the first place. The measures include implementing strong security measures, such as firewalls and encryption, regularly updating software and systems, and providing employee training on cybersecurity best practices. It is also important for businesses to have a plan for responding to a breach, including a designated team and clear protocols for communication and remediation. Businesses can help protect their customers’ data and maintain trust and loyalty by taking these steps.
Tech, Data, Privacy, And Time: It’s A Trade-Off, But Are We Giving Too Much?
The trade-off between technology, data, privacy, and time is an intricate issue that requires careful consideration. While technology has made our lives comfortable and more efficient, it has also created new risks and challenges, particularly regarding data privacy and security. Individuals and businesses need to be aware of the risks and take steps to protect themselves and their data. The steps may include using strong passwords, being careful about sharing personal information online and using security software to protect against cyber threats.
At the same time, it’s important not to let fear of these risks prevent us from taking advantage of technology’s benefits. By staying up-to-date and taking appropriate precautions, we can enjoy the convenience and opportunities technology provides while minimizing the potential downsides. Whether you’re writing about data privacy, cybersecurity, or other technology-related topics, I can provide the support you need to create compelling content. From researching the latest trends and statistics to providing suggestions for organizing your ideas, I can assist you every step of the way. With my help, you can communicate your message clearly and concisely, ensuring that your readers come away with a solid understanding of the topic at hand. So whether you’re writing a blog post, an article, or a report, let me help you deliver the results you need to succeed.
Prevention And Mitigation Of Data Breaches
Prevention and mitigation of data breaches are crucial to safeguarding sensitive information and maintaining the trust of customers and stakeholders. A data breach can affect financial losses, damage to reputation, and legal repercussions. Prevention measures include implementing strong passwords, regularly updating software and security systems, and training employees on cybersecurity best practices. Mitigation strategies involve having a response plan in place in case of a breach, such as identifying the source of the breach, comprising the damage, and notifying affected parties.
Companies can defend themselves and their customers from potential harm by prioritizing cybersecurity. It’s important to regularly assess and update security measures to stay ahead of evolving threats. In addition, companies should consider investing in cyber insurance to mitigate financial losses in the event of a breach. Businesses can maintain trust and safeguard operations by taking proactive steps to prevent and respond to cyberattacks.
Ways To Prevent Data Breaches
There are several ways that businesses can prevent data breaches. Here are a few:
1. Conduct regular security assessments: Regular security assessments can help identify vulnerabilities and potential risks in a company’s systems and processes.
2. Implement strong passwords and authentication measures: Strong passwords and multi-factor authentication can prevent unauthorized access to sensitive data.
3. Keep software up-to-date: Regularly updating software can help prevent security vulnerabilities from being exploited.
4. Train employees on cybersecurity best practices: Educating employees on recognizing and avoiding phishing scams, securely storing and sharing sensitive data, and other cybersecurity best practices can help prevent security breaches caused by human error.
5. Use encryption: Encrypting sensitive data can add an extra layer of protection, making it tougher for hackers to access or steal.
6. Limit access to sensitive data: Only grant sensitive data to employees who need it for their job responsibilities, and regularly review and update access permissions.
7. Have a response plan in place: In the event of a security breach, it’s imperative to have a response plan. This plan should include steps for containing the breach, notifying affected parties, and conducting a thorough investigation to determine the cause and prevent it from happening again. Regularly testing and updating the response plan can also help ensure it remains effective and up-to-date.
Steps Businesses Can Take To Protect Client Privacy
1. Implement a privacy policy: Develop and implement a clear privacy policy that outlines how client information is collected, used, and protected.2. Limit data collection: Collect only the information that is necessary for business operations and avoid collecting sensitive information unless it is required.
3. Secure data storage: Store client information in a secure location, on-site or in the cloud. Use encryption and other security measures to safeguard data from unauthorized access.
4. Train employees: Train employees on data privacy best practices and make sure they understand the importance of protecting client information.
5. Monitor data access: Monitor who has access to client information and limit access to only those who need it for their job responsibilities.
6. Respond to breaches: Develop a plan for responding to data breaches and notify clients if their information has been compromised.
By implementing these steps, businesses can help protect their client’s privacy and build trust with their customers.
The Future Of Data Breaches And Client Privacy
It is important to note that predicting the future is difficult and uncertain. However, some potential trends and developments may impact the future of data breaches and client privacy. One trend is the increasing use of artificial intelligence (AI) and machine learning in cybersecurity. These technologies can help detect and respond to breaches more quickly and accurately. However, they also raise concerns about privacy and the potential for AI to be used for malicious purposes.
Another trend is the growing importance of data privacy regulations, like the European Union’s General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA). These regulations give consumers more control over their personal information and require businesses to be more transparent about their data practices. More countries and states will likely adopt similar regulations in the future.
Businesses must stay vigilant and proactive in protecting their client’s privacy and data. By staying up-to-date on the latest cybersecurity trends and regulations, businesses can help prevent data breaches and maintain the trust of their customers.
Emerging Technologies To Address Data Breaches
Several emerging technologies can help address data breaches and improve cybersecurity. One such technology is blockchain, which provides a decentralized and secure way of storing and sharing data. Blockchain can help prevent data tampering and ensure data integrity.
Another technology is artificial intelligence (AI), which can help detect and prevent cyber attacks in real time. AI can analyze large data and identify patterns indicating a potential breach or attack.
Additionally, biometric authentication, such as fingerprint or facial recognition, can provide an extra layer of security for accessing sensitive data.
Policy Changes To Address Data Breaches
Businesses should consider implementing policies prioritizing data security to address data breaches. The policies can include regular security audits, employee training on best practices for data protection, and strict access controls for sensitive information.
Additionally, businesses should have a clear plan for answering a data breach, including notifying affected parties and taking steps to mitigate any damage.
It’s also important for businesses to stay current on emerging threats and vulnerabilities and continually reassess and update their cybersecurity strategies as needed.
New Developments In Client Privacy Protection
In current years, there have been increasing concerns about protecting client privacy in various industries. Businesses need to implement robust privacy policies and practices that safeguard their clients’ personal information to address these concerns.
One key step is ensuring that clients are fully informed about how data is collected, used, and shared. This step includes providing clear and concise privacy notices explaining what information is being collected, who it is being shared with, and how it is protected.
Businesses should also implement strong data protection measures, such as encryption and access controls, to prevent unauthorized access to client data. Regular security audits and vulnerability assessments can assist in identifying and addressing potential weaknesses in these systems.
Finally, businesses should be transparent and responsive in their communication with clients about any privacy concerns or breaches that may occur. These acts include providing timely and accurate notifications and assisting and supporting affected clients.
Conclusion
In summary, protecting client privacy is crucial for businesses to maintain trust and loyalty. This privacy can be achieved by implementing strong help and procedures, using security and technology and data storage systems, and being transparent and responsive in client communication. Consistent security audits and vulnerability assessments can help identify and address potential weaknesses in privacy protection.
For businesses, it is important to prioritize and invest in privacy protection measures to safeguard client information. This privacy protection helps maintain trust and loyalty and ensures compliance with data protection laws and regulations. Additionally, businesses should communicate clearly and transparently with clients regarding their privacy policies and procedures. For clients, it is important to be aware of the privacy policies and practices of the businesses they interact with. They should also protect their personal information by using strong passwords and avoiding sharing sensitive material with untrusted sources. Businesses and clients can create a safer and more secure online environment by working together.
Frequently Asked Questions (FAQs)
What Is A Data Breach?
A data breach is where sensitive, confidential, or protected information is accessed, stolen, or exposed by an unauthorized person or entity. This data breach can happen for numerous reasons, like hacking, malware, phishing, or human error. Data breaches can cause identity theft, financial loss, reputational damage, and legal consequences.
What Are The Most Common Reasons For Data Breaches?
The leading common causes of data breaches are hacking, malware, phishing, human error, and insider threats. Hackers use several techniques to exploit vulnerabilities in computer systems and networks to get unauthorized access to sensitive data. Malware, such as viruses, Trojans, and ransomware, can infect computers and steal data. Phishing is a method used by cybercriminals to trick people into revealing login credentials or other sensitive information. Human error, such as weak passwords, lost or stolen devices, accidentally sending sensitive information to the wrong recipient, or failing to install software updates, can lead to data breaches. Insider threats can be particularly damaging when an employee or contractor intentionally or unintentionally accesses or shares sensitive information. Implementing strong security measures, like firewalls, encryption, and access controls, is important to protect against these threats. Regular employee training and cybersecurity education can also help prevent data breaches.
What Are The Effects Of A Data Breach On Clients?
The consequences of a data breach for clients can be severe and long-lasting. Clients may experience financial losses, identity theft, and reputation damage. They may also lose trust in the organization that failed to protect their data and choose to take their business elsewhere. Sometimes, clients may even take legal action against the organization responsible for the breach. Therefore, organizations must take data security seriously and implement measures to prevent breaches.
What Should Clients Do If Their Information Has Been Compromised In A Data Breach?
If clients’ information has been compromised in a data breach, they should take immediate action to protect themselves. This protection includes changing passwords associated with the compromised account, monitoring their credit reports for suspicious activity, and contacting their financial institutions to alert them of the breach. It is also recommended to place a fraud alert or freeze on their credit report to prevent unauthorized access. Clients should also report the breach to the relevant authorities and the organization responsible for the breach. It is important to respond quickly to minimize the potential damage caused by the breach. In addition, clients should review their online security practices and consider implementing stronger measures such as two-factor authentication and regularly updating their passwords. Being careful when clicking links or downloading attachments from unknown sources is also important.
