Introduction
Data communication refers to exchanging information between two or more devices through a transmission medium such as wires, cables, or wireless connections. This process allows individuals or organizations to share data and collaborate on projects but presents potential security risks. This guide will explore various strategies for configuring data communication to ensure maximum security.
Securing data communication is crucial for protecting sensitive information from unauthorized access, theft, or manipulation. Without proper security measures, data can be intercepted by hackers or other malicious actors, potentially leading to data breaches, identity theft, financial loss, or reputational damage. By implementing strong encryption, authentication, and access control mechanisms, organizations can safeguard their data communication channels and ensure their data’s confidentiality, integrity, and availability. Additionally, compliance with industry regulations and standards such as GDPR, HIPAA, and PCI DSS is essential for protecting sensitive data and avoiding legal and financial penalties. As a writing assistant, I can help you craft clear and concise messaging around the importance of data security and the steps your organization is taking to protect sensitive information..
Why Is Data Communication Security Important?
Data communication security is important because it protects sensitive material from unauthorized access, interception, and tampering. Without proper security measures, confidential information such as personal data, financial information, and intellectual property can be compromised, leading to serious consequences such as identity theft, financial loss, and harm to reputation. Therefore, it is crucial to implement strong security protocols and encryption methods to safeguard data during transmission.
What Needs To Be Configured To Secure Data Communication?
To secure data communication, several things need to be configured, including:
- Encryption: This converts data into a specific code that can only be decrypted with a key or password. Encryption confirms that even if data is intercepted, it cannot be delivered without the proper decryption key.
- Authentication: This is verifying a user’s or device’s identity before allowing access to data. Authentication can be achieved through passwords, biometric scans, or digital certificates.
- Access Control: Once authentication is complete, access control determines what level of access the user or device has to the data. This can include restrictions on viewing, editing, or sharing the data.
- Backup and Recovery: It is important to have a backup system in place to ensure that data can be improved in case of a system failure or loss. This can include regular backups to an external drive or cloud storage.
- Monitoring and Auditing: Regular monitoring and auditing of the system can help detect any potential security breaches or unauthorized access attempts. This can include reviewing logs and access records to identify any suspicious activity.
Threats To Data Communication Security
Data communication security is another important aspect of maintaining a secure system. There are several threats to data communication security that need to be addressed, including:
Malware
Malware, or malicious software, is a kind of software designed to harm computer systems. Malware can come in many forms, involving viruses, worms, Trojans, and ransomware. Malware is spread via email attachments, infected websites, or USB drives. To protect against malware, installing up-to-date anti-virus software on all devices and regularly scanning for potential threats is important.
Social Engineering

Social engineering is an approach used by cybercriminals to manipulate people into giving away crucial information or performing activities that can compromise security. This can include phishing scams, where a hacker sends an email from a valid source, asking the recipient to click on a link or provide personal information. It can also include pretexting, where a hacker pretends to be some others, such as a bank employee, to gain access to sensitive information. To guard against social engineering attacks, it can be recommended to be cautious of unsolicited emails or phone calls, never provide personal information unless you know the request’s legitimacy, and use strong and unique passwords for all online accounts. It is also significant to regularly update software and security systems to prevent vulnerabilities that hackers can exploit. By being aware of the tactics used in social engineering attacks and taking steps to defend yourself, you can decrease the risk of falling victim to these scams.
Insider Threats
Insider threats refer to the risks posed to an organization by its employees or contractors with access to sensitive information or systems. These individuals may intentionally or unintentionally cause harm to the organization by stealing or leaking confidential information, sabotaging systems, or engaging in fraudulent activities. Organizations can implement strict access controls to prevent insider threats and limit the information employees can access. They can also monitor employee behavior and detect suspicious activity indicating a potential threat.
Network-Based Attacks
Network-based attacks are any cyber attack that targets an organization’s network infrastructure or systems. These attacks can be launched from external sources, such as hackers or cybercriminals, or internal sources, such as disgruntled employees or contractors. Network-based attacks can take many forms, including:
1. Denial-of-service (DoS) attacks: These attacks flood a network or system with traffic, causing it to become overwhelmed and unavailable to users.
2. Man-in-the-middle attacks intercept communication between two parties, allowing the attacker to eavesdrop or modify the communication.
3. Malware attacks involve using malicious software, such as viruses or Trojans, to infect a network or system and steal or damage data.
4. Password attacks involve attempting to guess or steal passwords to gain unauthorized access to a network or system.
5. Phishing attacks involve sending fraudulent emails or messages to trick handlers into clicking on a link or providing sensitive information, such as login credentials or financial information.
6. Social engineering attacks involve manipulating individuals into divulging sensitive data or performing actions that compromise security, often through deception or coercion.
7. Denial of Service (DoS) attacks involve overwhelming a network or system with traffic or requests, causing it to become inaccessible to valid users.
Methods For Data Communication Security
Configuring Firewalls For Data Communication Security
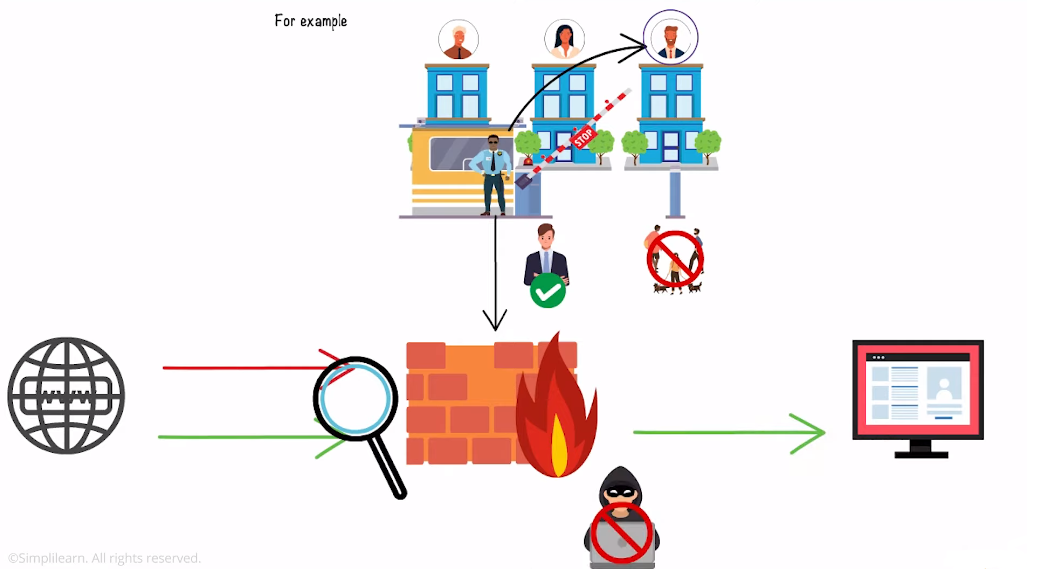
Configuring firewalls is an essential step in ensuring data communication security. Firewalls are a barrier between a trusted internal network and an untrusted peripheral network like the internet. They can be configured to permit or block traffic based on predefined rules. To configure a firewall for data communication security, organizations should follow these steps:
- Define the firewall’s purpose: Determine what the firewall is meant to protect and what traffic should be allowed or blocked.
- Determine the firewall’s placement: Decide where the firewall should be situated in the network topology to protect the desired assets effectively.
- Choose the appropriate firewall technology: Select one that meets the organization’s security requirements and is compatible with the existing network infrastructure.
- Configure firewall rules: Establish rules that determine what traffic is allowed and blocked based on the firewall’s purpose and placement.
- Monitor and update the firewall: Regularly monitor the firewall for any anomalies or suspicious activity and update the firewall rules to maintain optimal data communication security.
Configuring VPNs For Data Communication Security
Virtual Private Networks (VPNs) are another effective means of ensuring data communication security. VPNs create a secure, encrypted connection between two devices over the internet, allowing for private and secure communication. To configure a VPN, you must choose a VPN provider and install their software on the devices communicating with each other. Once the software is installed, you must configure the VPN settings, including the type of encryption used, the authentication method, and the VPN server location.
Encryption For Data Communication Security
Encryption converts plain text into a coded language that authorized parties can only decode. It is essential to data communication security as it ensures that sensitive information transmitted over the internet remains private and cannot be intercepted by unauthorized parties. Several encryption methods are used in data communication security, including symmetric encryption, asymmetric encryption, and hashing. Symmetric encryption involves using one key to encrypt and decrypt statistics, while asymmetric encryption uses two different keys for the same purpose. Hashing involves transforming data into a fixed-length string of characters, which cannot be reversed to obtain the original data. Hashing is often used to verify data integrity, as any changes to the original data will result in a different hash value. In addition to encryption methods, other security measures used in data communication include firewalls, intrusion detection, anticipation systems, and virtual private networks (VPNs). Firewalls block unauthorized access to a network, while intrusion detection and prevention systems monitor.
Authentication For Data Communication Security
Authentication is a crucial aspect of data communication security. It ensures that the parties involved in the communication are who they claim to be. There are several methods of authentication, including:
1. Passwords: This is the most common method of authentication. Users are required to enter a username and password to access a system.
2. Biometric authentication involves using physical characteristics like fingerprints, facial or voice recognition to authenticate users.
3. Two-factor authentication: This method requires users to give two forms of authentication, such as a password and a security token or biometric scan, to access a system.
4. Multi-factor authentication: This method requires users to offer multiple forms of authentication, such as a password, security token, and biometric scan, to access a system.
5. Certificate-based authentication involves using digital certificates to authenticate users and devices.
6. Single sign-on: This allows users to access multiple systems with a single login credential, reducing the need for multiple passwords.
Implementing Data Communication Security In The Cloud
To implement data communication security in the cloud, you can take the following steps:
- Use encryption: Encrypt all data transmitted between the cloud and your organization’s network. This ensures it cannot be read even if the data is intercepted.
- Use secure protocols: Use secure protocols such as HTTPS, SSL, and TLS to ensure that data is transmitted securely.
- Implement access controls: Implement access controls to ensure that only sanctioned users can access the cloud environment.
- Monitor network activity: Monitor network activity to detect any unauthorized access or suspicious activity.
- Use firewalls: Implement firewalls to monitor and control incoming and outgoing traffic. This helps to prevent unauthorized access to the cloud environment.
- Conduct regular security audits: Regularly conduct security audits to identify vulnerabilities and take necessary actions to mitigate them.
- Train employees on data security: Train them on best practices to ensure they know the risks and take necessary precautions.
Conclusion
Data communication security is paramount in today’s digital age. It ensures that sensitive data is protected from unauthorized access, theft, and misuse. Organizations can safeguard their data and prevent costly breaches by following best practices such as strong encryption, implementing multi-factor authentication, and regularly monitoring access. As a writing assistant, I recommend that organizations prioritize data communication security as part of their cybersecurity strategy to protect their business and customers from potential harm.
Securing data communication is crucial for any organization that wants to protect sensitive information from unauthorized access. I strongly encourage readers to take action and implement the security measures discussed in this article, including strong encryption, multi-factor authentication, and regular access monitoring. Doing so can safeguard your business and customers from potential harm and prevent costly data breaches. Remember, data security is not an option and is necessary in today’s digital age.
Frequently Asked Questions (FAQs)
What Are The Essential Components Of Data Communication Security?
The essential components of data communication security include:
1. Confidentiality: This refers to data protection from unauthorized access. Encryption is commonly used to ensure confidentiality.
2. Integrity: This refers to data protection from unauthorized modification. Digital signatures and message authentication codes are commonly used to ensure integrity.
3. Availability: This refers to data protection from unauthorized denial of access. Redundancy and backup systems are commonly used to ensure availability.
4. Authentication: Verifying a user’s or system’s identity. Passwords, biometrics, and digital certificates are commonly used to ensure authentication.
5. Non-repudiation refers to the ability to prove that a message was sent and received by the intended parties. Digital signatures and timestamps are commonly used to ensure non-repudiation.
What Is A Firewall, And How Does It Enhance Data Communication Security?
A firewall is a network security system that monitors and controls received and outgoing network traffic based on predetermined security rules. It is a blockade between a reliable internal network and an untrusted exterior network, like the Internet. Firewalls enhance data communication security by filtering out unwanted traffic and preventing unauthorized access to a network. They can also block malicious software and prevent it from spreading through the network. Additionally, firewalls can be configured to permit only specific types of traffic, such as email or web browsing, while blocking other types of traffic, such as file sharing or remote access. By controlling network access, firewalls help ensure data communication’s confidentiality, integrity, and availability.
What Is A VPN, And How Does It Enhance Data Communication Security?
A VPN, or Virtual Private Network, is a technology that allows users to access a private network over the internet securely. It creates a protected and encrypted connection between the user’s device and the private network, which can be located anywhere in the world. When users connect to a VPN, their internet traffic is routed via an encrypted tunnel, protecting their data from interception or eavesdropping. This is particularly dynamic when using public Wi-Fi networks, which are often unsecured and vulnerable to cyber-attacks. VPNs are used by personnel and businesses alike for a variety of purposes. Some people use VPNs to access geo-restricted content, such as streaming services or websites only available in certain countries. Others use VPNs to protect their privacy and anonymity online, as the encrypted connection hides their IP address and location from prying eyes.
Businesses often use VPNs to allow remote workers to securely approach company resources, such as files and applications, from anywhere in the world. VPNs can also connect multiple offices or branches of a company, creating a secure and private network that spans multiple locations.
What Is Encryption, And How Does It Enhance Data Communication Security?
Encryption is converting plain text or data into a coded note that can only be read by authorized parties with the key to decipher the code. Encryption enhances data communication security by making it difficult for unauthorized parties to intercept, read, or modify the transmitted data. Encryption works by using a mathematical algorithm to scramble the data in a way that can only be reversed with a specific key. The key is a unique code used to decrypt the data and make it more readable. This means that even if an illegal party intercepts the encrypted data, they cannot read it without the key.
Encryption is a powerful tool for protecting sensitive data from unauthorized parties, such as financial, personal, and confidential business information. It is commonly used in online transactions, email communication, and data storage to keep the data secure and private.
