Introduction
Provenance is the term used to describe the origin and history of a piece of data. In data security, understanding provenance is crucial for ensuring the accuracy and reliability of the information. It allows organizations to trace the source of data and verify its authenticity, making it easier to identify any potential risks or vulnerabilities.
Importance Of Provenance in Data Security
Provenance plays a vital role in data security because it enables organizations to trace the history of their data and detect any unauthorized modifications or tampering attempts. By maintaining accurate records of who accessed what information and when organizations can quickly identify potential security breaches and take appropriate action to prevent further damage. Additionally, provenance helps companies comply with regulatory requirements by demonstrating that they have implemented adequate security measures to protect their data.
The Connection Between Provenance And Data Security
Provenance plays enables organizations to verify the authenticity and integrity of their data, ensuring that it has not been tampered with or altered in any way. This is particularly important for sensitive data such as financial records or personal information, where any unauthorized access could lead to serious consequences.
Data provenance also helps in identifying potential security breaches by tracking the movement of data across different systems and applications. By understanding how data has been accessed and modified over time, organizations can identify unusual patterns or activities that may indicate a security breach. This can help them take proactive measures to prevent further damage and secure their systems. Furthermore, provenance can be used to ensure compliance with regulatory requirements related to data privacy and security.
What is Provenance?
Explanation Of The Term
Provenance, in the context of data security, refers to the documentation and tracking of the origins and history of a piece of data or information. This can include information such as who created it when it was created, how it has been modified over time, and who has had access to it. By keeping track of provenance, organizations can better ensure the authenticity and validity of their data.
Examples Of Provenance
There are several examples of provenance that can help illustrate its significance. One common example is in the art world where provenance plays a vital role in determining the authenticity and value of artwork. Every piece of art comes with a history that tells us about its creation, ownership, exhibition, and sale records. This information provides a clear lineage for artwork from its original creator to its current owner. Without this history, an artwork’s value and authenticity will be difficult to determine.
Another example is in the field of science where researchers need to ensure that their findings are trustworthy and accurate. Provenance helps scientists track their research methods and results from start to finish, ensuring transparency throughout the process.
Moreover, companies also use provenance as part of their supply chain management system. They use it to verify product origins, authenticate suppliers’ claims about products such as organic food items or fair-trade goods – which enhances trust between consumers and producers.
Provenance In Data Security
Role Of Provenance In Data Security
Provenance can be particularly important in contexts where multiple parties are involved in handling sensitive data. For instance, in healthcare settings where patient records must be shared among different providers while maintaining confidentiality requirements. In such cases, provenance can help track who has accessed the records and for what purpose. Provenance can also play a significant role in detecting malicious activities such as hacking attempts or insider threats by providing a comprehensive record of all actions taken on the system.
Benefits Of Provenance In Data Security
One of the major benefits of provenance in data security is that it helps detect anomalies and potential threats. By analyzing provenance data, security analysts can identify patterns that could indicate a breach attempt or insider threat. Furthermore, if a breach occurs, provenance information can help trace back the attack to its source and minimize damage.
Another advantage of utilizing provenance in data security is that it supports compliance with regulatory requirements such as GDPR and HIPAA. These regulations require organizations to maintain accurate records of how personal information is collected, processed, stored and shared with third parties. Provenance provides transparency throughout this process by providing proof of compliance with these guidelines which further reduces legal risks associated with noncompliance penalties.
Provenance In The Data Life Cycle
Provenance During Data Collection
Provenance during data collection helps prevent fraudulent activities by tracking the source of the collected data. It enables businesses to trace back any inconsistencies in their datasets to identify issues such as errors, inaccuracies, or corruption during processing stages.
Provenance During Data Transmission
One of the key aspects of data security is ensuring that data provenance is maintained during transmission. Provenance refers to the history and origin of data, including its source, how it has been processed, and who has accessed it. Without proper provenance management, it becomes difficult to trace the origins and life cycle of data, which makes it vulnerable to security threats.
Maintaining proper provenance during data transmission requires several measures, including encryption and secure communication channels. Encryption involves transforming plaintext into ciphertext so that only authorized parties can access the original message. This helps prevent unauthorized access to sensitive information while in transit across networks or through storage devices. Secure communication channels such as virtual private networks (VPNs) and secure sockets layer (SSL) also help protect against interception by third parties.
Provenance During Data Processing
Maintaining provenance throughout the entire lifecycle of data processing involves capturing metadata such as timestamps, user identity, location, permissions, and other relevant information. This information allows users to understand how the data was created or modified and who accessed it at different stages. By implementing provenance tracking mechanisms in their systems or applications, organizations can improve their ability to manage risk associated with sensitive information.
Technologies For Provenance In Data Security
Blockchain
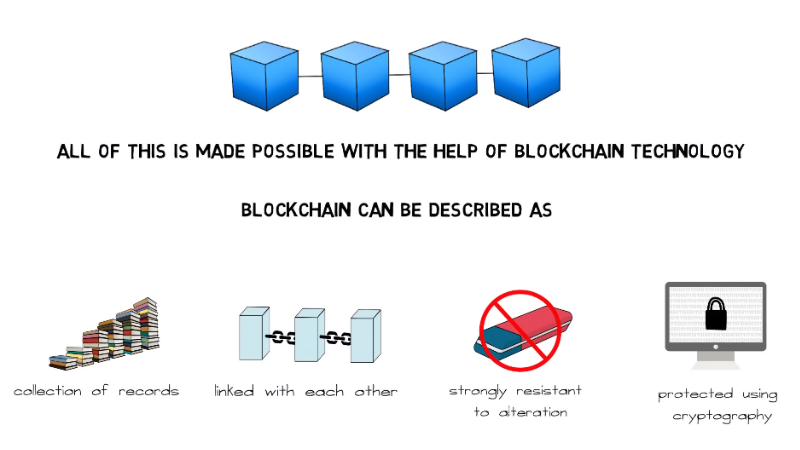
The blockchain network ensures that any data added to it is tamper-proof, transparent, and immutable. This feature makes it an ideal technology for managing provenance in data security. Provenance refers to the origin or ownership of an item, and with blockchain technology, every transaction can be traced back to its source.
The use of blockchain for provenance in data security is crucial because it helps prevent fraud or tampering with information. With the transparency provided by the blockchain network, it becomes easier for auditors and regulators to verify the authenticity of data without relying on third-party intermediaries. Additionally, since all participants have access to the same information on a shared ledger system, there is greater trust among the parties involved.
Data Logging
Data logging is an essential aspect of data security that involves the systematic recording of activities performed on a network, application, or system. The primary purpose of data logging is to provide a detailed account of user actions and system events in case an investigation into data breaches or suspicious activities becomes necessary. Data logs can help identify the source of malicious attacks, track changes made to files, and detect any unauthorized access attempts.
Data logging supports provenance tracking as it allows organizations to trace the origin and movement of their data. This information can be used to ensure compliance with regulations, manage risks effectively, and improve overall security posture. Provenance tracking helps determine who has accessed specific datasets at what time and enables auditing trails that can be used as evidence in legal proceedings.
Digital Signatures
Digital signatures provide a way to verify the authenticity of digital documents by ensuring that they have not been tampered with or altered in any way. A digital signature is essentially an electronic fingerprint that is unique to each document, and it can be used to verify the identity of the signer.
One of the main benefits of using digital signatures is that they provide a high level of security and protection against fraud. They are much harder to duplicate than traditional handwritten signatures, and they cannot be forged or altered without detection. This makes them particularly useful for sensitive documents such as contracts, legal agreements, and financial transactions.
Secure Hash Algorithms
Secure Hash Algorithms (SHA) are widely used in data security to ensure the integrity of data. A hash function is a mathematical algorithm that takes input data and produces a fixed-size output. SHA is designed to produce hashes that are unique, meaning it’s nearly impossible for two different sets of input data to produce the same hash value. This makes SHA an ideal choice for digital signatures, password hashing, and other applications where data integrity is critical.
One of the significant advantages of using SHA algorithms is their resistance to tampering and collision attacks. A tampering attack occurs when someone tries to modify any part of the original message or signature, while a collision attack involves creating two different messages with the same hash value intentionally. The probability of such attacks happening with SHA algorithms is low as they provide strong cryptographic protection over sensitive information.
Data Visualization
Data visualization is an effective tool for representing complex data sets in a clear and concise manner. It enables users to interpret data and identify trends, insights, and patterns that may not be immediately obvious. Visualization plays a significant role in improving decision-making processes by providing visual cues that help users understand the information more effectively.
Visualizing provenance in data security allows organizations to monitor access to sensitive information and trace any unauthorized access or modification attempts back to their source. By using visual representations such as networks, trees, graphs, charts, or tables, organizations can easily detect anomalies and suspicious activities within their systems. This makes it easier for them to take corrective action before any damage occurs.
Challenges Of Implementing Provenance In Data Security
One significant challenge is the complexity involved in capturing and storing provenance information. Depending on the type and volume of data being processed, it can quickly become overwhelming to keep track of every change made to each data element. Additionally, ensuring that the captured information is accurate and reliable requires careful design and implementation of monitoring mechanisms.
There is the issue of scalability. As the volume of data increases, traditional methods may not be sufficient for tracking provenance. This requires specialized tools and techniques that are capable of handling large amounts of data without compromising performance.
There is the challenge of interoperability between different systems and networks. Provenance information needs to be shared across different systems seamlessly for it to be effective in enhancing security. Achieving this level of interoperability requires standardization efforts that are often complex and time-consuming.
Provenance Standards and Best Practices
Existing Standards And Best Practices For Provenance In Data Security
The W3C PROV (Provenance Data Model) standard provides a framework for recording and sharing provenance information. It helps track the origin, ownership, and changes made to the data over time.
Another important practice in provenance is implementing access controls. Access controls limit who can view or modify certain data. This ensures that sensitive information is not accessed by unauthorized personnel, reducing the risk of breaches.
Encryption is also a widely used practice in provenance. Encrypting data makes it more difficult for hackers to read or access it without authorization, ensuring the confidentiality of sensitive information.
Recommendations For Improving Standards And Best Practices
To improve standards and best practices in this area, organizations must first establish a clear understanding of the importance of provenance. This includes developing guidelines for tracking and documenting the origin, ownership, and movement of data throughout its lifecycle.
In addition to establishing clear guidelines for provenance tracking, organizations should also consider implementing automated tools and technologies to assist with this process. For example, blockchain technology can be used to create an immutable record of data transactions that cannot be altered or deleted without detection. Similarly, machine learning algorithms can be used to identify anomalies or inconsistencies in data provenance that may signal potential security threats.
Organizations must prioritize ongoing education and training on best practices for maintaining data provenance. This includes regular training sessions for all employees involved in handling sensitive data as well as ongoing communication about any updates or changes to policies related to provenance tracking.
Provenance In Machine Learning And AI
Importance Of Provenance In Machine Learning And AI
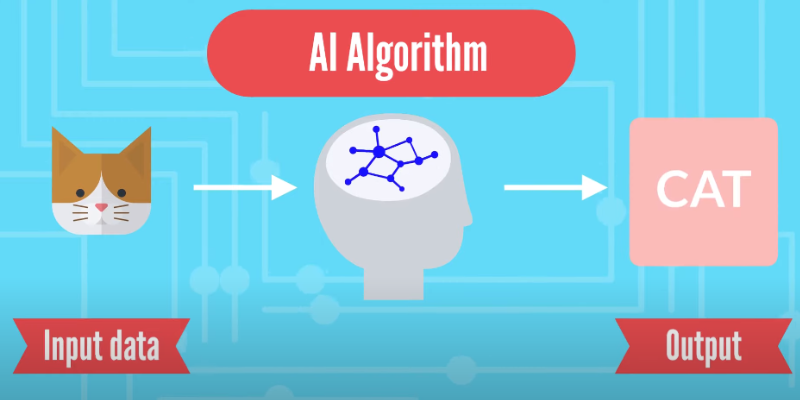
Provenance in machine learning and AI refers to the traceability of data sources and how data was processed. It is crucial because it helps to ensure data quality, transparency, and accountability in decision-making processes. Provenance allows for the tracking of changes made to data over time, enabling users to identify errors or biases in a dataset. Moreover, it helps in the creation of auditable records that are essential for compliance with regulatory requirements.
In addition to ensuring data quality and transparency, provenance can also aid in mitigating security risks associated with machine learning and AI algorithms. Cybersecurity threats have become increasingly sophisticated as attackers continuously look for ways to infiltrate systems. With provenance tracking, organizations can detect anomalous behavior early on before any significant damage is done.
Overall, provenance plays a critical role in building trust between stakeholders who use machine learning and AI technologies. It promotes the ethical usage of these systems by providing visibility into their inner workings while also protecting against security threats that could potentially cause harm..
Challenges Of Implementing Provenance In Machine Learning And AI
Implementing provenance in machine learning and AI systems poses many challenges. One significant challenge is the difficulty of tracking data lineage, as these systems process large volumes of data from various sources simultaneously. Consequently, tracing the origin of inputs and outputs can be challenging, particularly when dealing with complex models.
Another challenge is ensuring that provenance information remains secure throughout the entire ML/AI workflow. Provenance information often contains sensitive information about data sources and users’ identities, making it a prime target for malicious attacks. To mitigate this risk, organizations need to implement robust security measures that protect provenance information from unauthorized access or modifications.
There is a lack of standardization in how different ML/AI platforms handle provenance information. This inconsistency makes it challenging to move data between different platforms or even within the same platform, leading to increased complexity and delays in data processing workflows.
Conclusion
It is evident that provenance plays a crucial role in ensuring data security. By tracking the origin and history of data, organizations can effectively monitor access to sensitive information and detect any unauthorized activity. Provenance also enables organizations to ensure compliance with regulations such as GDPR by providing transparency on how personal data is collected, processed, and stored.
Furthermore, provenance can aid in the detection of cyber threats and prevent them from escalating into major security breaches. With real-time monitoring of data lineage, organizations can identify abnormal patterns or suspicious behavior early on and take appropriate measures to mitigate risks.
FAQs
What is the difference between provenance and metadata?
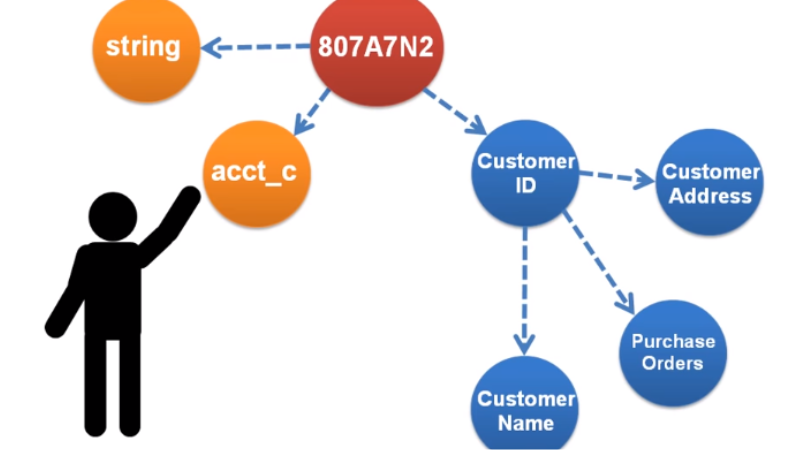
Provenance refers to the history or lineage of a particular data asset, including its origin, ownership, and any changes made to it over time. It provides a detailed record of how the data was created, manipulated, accessed, and shared. Provenance information helps in maintaining transparency and traceability of data which is essential for ensuring data security.
On the other hand, metadata refers to descriptive information about a particular data asset such as its format, location, size, authorship etc. Metadata doesn’t provide any information about the history or lineage of a data asset but rather focuses on describing what it is about. Metadata plays an important role in organizing and managing large volumes of data by enabling easy searchability and accessibility.
Provenance enables tracking back to the source of an issue if something goes wrong with a particular dataset while metadata assists users in identifying useful datasets based on their descriptions without necessarily knowing their origins or histories.
How Can Provenance Be Used To Prevent Data Breaches?
By tracking the origin and history of a piece of data, organizations can identify potential weaknesses in their system and mitigate risks before they become significant threats. Provenance technology provides a complete audit trail of all activities associated with a given dataset, allowing organizations to monitor each step in the data lifecycle.
Moreover, provenance enables the establishment of trust between different entities involved in information exchange. It ensures that data is only accessed by authorized parties who have been granted permission by the owner or curator. With this level of control, companies can ensure compliance with privacy regulations such as GDPR and CCPA, which mandate strict controls over how personal information is collected, stored, and shared.
Is It Possible To Implement Provenance In Legacy Systems?
Legacy systems are often outdated and may not have the necessary infrastructure to support provenance tracking. However, it is still possible to implement provenance in these systems with careful planning and execution.
Can Provenance Be Used To Track Individual User Behavior?
By analyzing provenance information, it may be possible to track how individual users interact with specific pieces of data or systems.
However, there are also significant privacy concerns associated with using provenance for this purpose. Tracking user behavior through provenance could potentially reveal sensitive information about individuals, such as their online activity or personal preferences. As a result, any use of provenance for tracking user behavior would need to balance the benefits with the potential risks and ensure that appropriate safeguards are in place to protect user privacy.
