Introduction
Definition Of Physical Data Security

Physical data security is a set of measures implemented to protect physical storage devices and media that contain sensitive or confidential information. These measures can include the use of locks, access controls, alarms, and video surveillance systems to prevent unauthorized access to sensitive data. Physical security also extends to the protection of servers, switches, routers, and other network infrastructure equipment that store or transmit data.
Importance of Physical Data Security
Physical data security is an essential aspect of protecting sensitive information. It involves the protection of physical devices such as laptops, hard drives, and USB drives that contain confidential data. The importance of physical data security cannot be overstated because a single breach can have significant consequences on a company’s reputation and financial stability.
Physical data security is crucial is that it serves as a backup plan in case of cyber-attacks or other forms of digital breaches. For instance, if hackers gain access to your online accounts and lock you out, having backed-up files on a separate device can help recover important information. Physical data security also protects against natural disasters such as floods or fires that could destroy electronic devices.
Additionally, complying with regulations like HIPAA and GDPR requires adherence to strict guidelines for securing physical documents containing personal information. An organization must ensure the safe storage, handling, and disposal of confidential documents to avoid legal action from regulatory bodies or affected parties.
Overview of the Article
The article highlights the importance of securing paper files, electronic devices, and even employees themselves. It then delves into specific threats such as theft, natural disasters, and human error. Each threat is discussed in detail with practical tips on how to mitigate risks. The article also emphasizes the importance of creating a culture of security within organizations through employee training and awareness programs.
Understanding Physical Data Security
Types of Physical Data Security
- Locks and Keys: Perhaps the most common physical data security method is to use locks and keys. This can be anything from a simple padlock on a filing cabinet to high-tech biometric access control systems that require fingerprints or retinal scans to grant entry. However, it’s important to remember that locks are only as secure as their keys; if someone manages to steal or duplicate a key, they can easily bypass the lock.
- Security Cameras: Installing security cameras is another way to physically protect your data. These devices can monitor who enters and exits certain areas of your business, record footage of any suspicious activity, and provide evidence in case of theft or other crimes. Additionally, just the presence of cameras can deter potential criminals from attempting to breach your security.
- Alarms and Sensors: Another type of physical data security measure is alarms and sensors. These can range from basic motion detectors that trigger an alarm when someone enters an unauthorized area, to more advanced systems that detect changes in temperature or air pressure – indicating the presence of someone trying to break into a room through walls or ceilings.
Physical Security Measures for Data Protection
Access Controls
Access controls are an essential part of physical data security. Access control systems restrict access to certain areas or information based on pre-defined rules and permissions. The goal is to ensure that only authorized personnel can access sensitive information, resources, or systems. This can be achieved through various methods such as biometric identification, smart cards, PIN codes, and key fobs.
Effective access controls require a well-planned strategy that addresses several aspects such as identifying the level of access required for each user group, defining clear policies and procedures for granting and revoking access rights, implementing appropriate technology solutions, training employees on how to use the system effectively, and regularly reviewing and updating the access control policy.
One of the benefits of implementing robust access controls is the ability to monitor who has accessed what data or resource at any given time. This is crucial in case of security incidents or breaches since it allows for quick containment and investigation. Access control systems can also help organizations comply with regulatory requirements by providing an audit trail of all activities related to sensitive data or resources.
Key Cards and Biometric Scanners
Key cards and biometric scanners are two of the most popular identification and access control technologies used in physical data security. Key cards or smart cards are plastic cards embedded with a small chip that stores data that can be read by a card reader. They provide a secure way to grant access to authorized personnel while keeping unauthorized individuals out of restricted areas. Key card systems can also track who enters and exits certain areas, providing an audit trail for security purposes.
On the other hand, biometric scanners use unique physical characteristics such as fingerprints, facial recognition, iris scans, or voice patterns to identify individuals. Biometrics offers a high level of security because they cannot be lost or stolen as key cards can. However, implementing biometric technology can be more expensive and require additional hardware and software investments.
Both key card and biometric systems have their own advantages and disadvantages when it comes to physical data security. The choice ultimately depends on the organization’s needs, budget, level of risk tolerance, and desired level of convenience for users.
Guards and Security Personnel
Guards and security personnel play a crucial role in physical data security. Their job is to monitor all access points, ensure the safety of people and property, and identify any suspicious activity that could compromise the integrity of sensitive information. Security guards are trained to detect potential threats by conducting regular patrols around buildings or premises, checking IDs, and scanning bags for prohibited items.
In addition to providing physical security, guards can also help prevent data breaches from occurring by ensuring that computer systems are secured when not in use. This includes locking up workstations, securing USB ports and other data transfer devices, and enforcing strict password policies. Guards may also be responsible for monitoring surveillance cameras or implementing biometric access control systems to reduce the risk of unauthorized access.
Having well-trained guards and security personnel as part of your physical data security strategy can help protect your business from theft or unauthorized access to sensitive information.
Video Surveillance
The use of cameras helps to deter criminal activity, monitor employee behavior, and provide evidence in the event of an incident. When implementing video surveillance, it is important to consider factors such as camera placement, image quality, and storage capabilities. Cameras should be strategically placed in areas where there is high foot traffic or valuable assets. Additionally, high-resolution cameras can provide more detailed images that are helpful in identifying individuals or objects.
One common concern with video surveillance is privacy infringement. It is important to communicate clearly with employees and visitors about the presence of cameras and how footage will be used. In addition, organizations must comply with relevant laws and regulations regarding video surveillance practices.
Alarms and Notifications
Alarms and notifications are designed to alert you when there is a breach in your security measures, giving you time to respond before any damage is done. There are a variety of different alarms and notifications available, from simple door chimes to sophisticated motion sensors that can detect even the slightest movements.
One common type of alarm used in physical data security is the intruder alarm. This system consists of sensors placed around the perimeter of a building or property that will trigger an audible alarm if they detect any unauthorized entry. In addition, many modern intruder alarms also come equipped with notification features that can send alerts directly to your mobile device or email inbox.
Another important type of notification in physical data security is the environmental alert. These systems monitor temperature, humidity levels, and other environmental factors that could potentially damage sensitive equipment or information stored on paper documents. Environmental alerts provide early warnings so that you can take steps to mitigate any potential damage and protect your valuable assets.
Physical Data Security Best Practices

Employee Training
Employee training allows employees to understand the importance of protecting sensitive information and how to do so effectively. This type of training should cover topics such as proper password management, secure document handling, and identifying potential security breaches.
One important element to include in employee training is the use of access control systems. This includes key cards, biometric scanning, or other mechanisms that ensure only authorized personnel can access certain areas. Employees should be trained on how these systems work and the importance of not sharing their credentials with others.
Regular refreshers on physical data security are necessary to ensure that employees continue to follow best practices over time. Consistent reinforcement will help prevent complacency and reinforce the importance of staying vigilant when it comes to protecting sensitive information.
Risk Assessment
Risk assessment refers to the process of identifying, analyzing, and evaluating potential risks that could cause harm or damage to an organization’s physical assets and information. The aim of risk assessment is to help organizations understand their vulnerabilities, assess the likelihood and impact of potential threats, and develop strategies to mitigate or manage those risks.
Effective risk assessment involves several steps. It requires a thorough understanding of the organization’s physical assets, including buildings, equipment, personnel, and data storage devices. It involves identifying potential threats such as theft or unauthorized access to sensitive information. It requires an evaluation of the likelihood and potential impact of each threat so that appropriate measures can be taken to prevent or minimize its effects.
By conducting regular risk assessments as part of their overall physical data security strategy organizations can ensure that they are prepared for any eventuality. With effective risk management practices in place, organizations can protect themselves against a wide range of threats from natural disasters like fire flooding earthquake etcetera., and criminal activity such as theft hacking vandalism etcetera., or even employee negligence which can lead to unintentional breaches in security protocols thereby ensuring continuity in business operations while safeguarding sensitive information from being leaked out by cybercriminals intent on causing harm through various means available at their disposal like social engineering tactics phishing scams malware attacks ransomware attempts etcetera.
Regular Maintenance and Audits
It is important to conduct regular checks on all hardware, such as servers and backup systems, to ensure that they are functioning properly. These checks should include monitoring the temperature and humidity within the server room, checking for any signs of wear or damage on cables and connectors, and making sure that all software is up-to-date.
Audits should also be conducted regularly to ensure that physical access controls are working effectively. This includes checking that all doors and windows have appropriate locks or access controls in place, ensuring that cameras are positioned correctly, and reviewing logs of who has accessed the server room.
A comprehensive audit should also assess potential threats from both internal and external sources. This includes checking whether employees have been trained in data security protocols, identifying any vulnerabilities in the system, conducting background checks on employees with access to sensitive information, and testing the effectiveness of disaster recovery plans.
Challenges and Solutions for Physical Data Security
Common Physical Security Challenges
Controlling access to their premises. This includes managing who enters the building, at what times, and for what purposes. Without proper controls in place, unauthorized personnel can gain entry to sensitive areas and compromise data or other valuable assets.
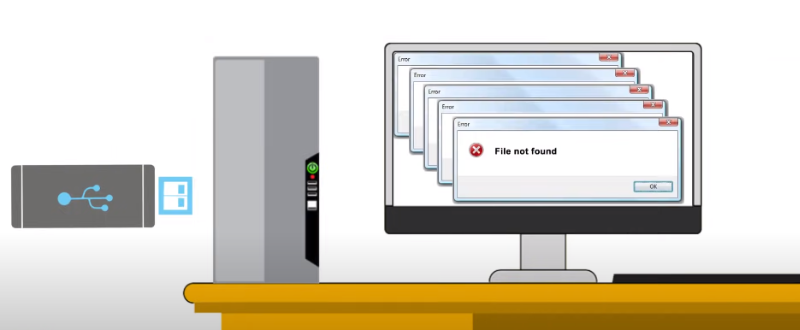
Protecting against theft or damage to equipment and devices that store important information. Whether it’s laptops, servers, or hard drives, these items are vulnerable to theft if they’re not properly secured. Physical security measures like cable locks, locked cabinets, or cages can help prevent theft but may also be inconvenient for employees who need frequent access.
Natural disasters such as floods or fires can also cause significant damage to a company’s physical infrastructure and result in data loss. Organizations must have plans in place to mitigate these risks by implementing disaster recovery procedures that include regular backups of critical data offsite and redundant systems that can take over in case of an emergency.
Human Error
Human error is a common cause of data breaches, and it can happen in many ways. Leaving sensitive documents unattended or not shredding them properly are some examples. Employees might forget to lock up confidential files, share passwords with unauthorized individuals, or fall victim to phishing scams that trick them into disclosing login credentials. As much as organizations try to minimize their risk of human error through training and security protocols, mistakes still happen.
Budget Constraints
Many companies do not have the money to invest in top-of-the-line security measures, which can leave them vulnerable to theft or other types of physical breaches. However, there are some cost-effective solutions that can still provide adequate protection.
Solutions to Physical Security Challenges
Install surveillance cameras that monitor activities around the premises. Cameras can deter criminals from attempting illegal activities or provide evidence in case of a breach. Access control systems are also useful in managing who enters and exits the building by requiring verification before granting entry. This helps prevent unauthorized access to restricted areas.
Implement proper employee training on physical security practices. Employees should be educated on how they can contribute to maintaining physical security within the workplace through best practices such as locking doors when leaving rooms unattended or not sharing access codes with unauthorized individuals. Regular audits of physical security measures can also help identify vulnerabilities and improve overall protection against breaches.
Automation and Technology
The rise of automation and technology has brought about numerous benefits across various industries. In terms of physical data security, it has allowed for the development of advanced security systems that can detect, prevent and respond to threats in real time. These systems are capable of monitoring a facility’s entrances and exits, and detecting unauthorized access attempts or suspicious behavior.
Moreover, automation and technology have enabled the implementation of strict access controls that limit who can access sensitive information. With biometric authentication technologies such as fingerprint or facial recognition scanners, only authorized personnel can gain access to restricted areas or devices containing sensitive data. This helps to ensure that confidential information is kept secure at all times.
Collaborative Efforts
Collaborative efforts are not just about securing your personal information or data, but also about ensuring that the environment and the people around you are safe. Collaborating with others can help identify risks that may have been overlooked and provide solutions to complex problems.
To foster collaborative efforts establish a team or committee focused on physical data security. This group can consist of employees from different departments such as IT, HR, and Facilities Management who will work together to address any concerns and implement best practices for physical data security.
Conclusion
Physical data security is a critical aspect of protecting your information in the physical world. The increasing number of cyber attacks and data breaches means that securing your physical environment has become more important than ever before. By implementing simple measures such as installing locks on doors and windows, using CCTV cameras, and limiting access to sensitive areas, you can significantly reduce the risk of unauthorized access.
It is also important to ensure that all employees are aware of the importance of physical data security and are trained on how to identify potential risks. Regular drills should be conducted to test their knowledge and readiness in case of an emergency or breach. Moreover, regular maintenance checks should be carried out on all security systems and equipment to ensure they are functioning optimally.
FAQs
Why is Physical Data Security important?

Physical data security is vital because it safeguards sensitive information from theft, damage, or destruction. This type of security prevents unauthorized access to important physical data such as documents, hardware, and storage devices. Physical data breaches can occur easily if these items are left unattended, misplaced, or stolen.
Moreover, physical data security is crucial for regulatory compliance. Many regulations require businesses to take adequate measures to ensure the protection of their customers’ information. Failing to comply with these regulations can lead to legal implications and reputational damage for companies.
In addition, physical data security ensures business continuity in case of disasters such as fires, floods, and natural disasters. Having a proper backup plan and storing important documents securely can help organizations quickly recover from such incidents without losing critical information or disrupting business operations.
What are some common physical security challenges?
One of the most common physical security challenges faced by organizations is unauthorized access. Whether it be through tailgating or social engineering tactics, individuals can gain access to sensitive information simply by being physically present in an area they shouldn’t be. This highlights the importance of proper access control measures like keycard systems and identity verification protocols.
Another challenge is theft, which can occur in many forms such as theft of laptops, paper files, or even entire servers. To combat this risk, companies should consider implementing physical locks on doors and cabinets where sensitive data is stored. Additionally, installing surveillance cameras and keeping an updated inventory of all assets can help to deter potential thieves.
Natural disasters also pose a significant physical security challenge for organizations. Fires, floods, and earthquakes are just some examples that can cause significant damage to critical infrastructure and result in data loss or downtime. Proper disaster preparedness planning including creating backups off-site and identifying alternative locations for employees to work from can help mitigate the impact of these events on business operations.
What are some emerging trends in physical data security?
One of the emerging trends in physical data security is the use of biometrics for access control. Biometric authentication technologies, such as facial recognition and fingerprint scanning, are becoming more prevalent in securing physical spaces. This technology eliminates the need for traditional access methods like keys or keycards which can be easily lost or stolen.
Another trend is the use of blockchain technology to secure physical data. Blockchain provides a decentralized and tamper-proof way to store data that cannot be altered without consensus from all parties involved. This makes it an ideal solution for industries such as healthcare and finance where sensitive information must be kept secure.
There is also a growing trend toward using artificial intelligence (AI) and machine learning (ML) to enhance physical security measures. AI-enabled cameras can detect anomalies in real-time and alert security personnel before any damage occurs. ML algorithms can analyze vast amounts of data to identify patterns that may indicate potential threats, allowing organizations to take proactive measures before any incident occurs.
