Introduction
Definition of Data Security Incident
A data security incident refers to any event that leads to unauthorized access, loss, theft, or disclosure of sensitive information. This can include personal customer data such as names, addresses, social security numbers, credit card details, and even intellectual property like patents and trade secrets. Data breach incidents are becoming increasingly common in our digital age with a significant rise in cyberattacks.
Data breaches can be caused by various factors including human error or negligence such as misconfigured systems or weak passwords. Malicious attacks from external sources like hackers and insider threats from employees can also lead to data security incidents. The severity of the incident depends on the type of information compromised and how it was accessed.
Importance of Responding to a Data Security Incident
A data security incident can happen to any organization, no matter how big or small. It is essential to respond immediately and appropriately to minimize the damage and prevent future incidents. Responding quickly and effectively can help an organization regain control over its systems, and avoid regulatory fines, legal action, reputational damages, loss of customer trust, and financial losses.
Overview of the Article
In today’s digital age, data security incidents are becoming all too common. From phishing attacks to malware infections, cyber threats are a major concern for businesses worldwide. In this comprehensive guide, we will explore how to respond to a data security incident in order to minimize its impact on your organization.
Preparing For A Data Security Incident
Importance Of Having A Response Plan
A response plan outlines the steps that your organization will take in the event of an information security breach or any other type of cyberattack. With a well-designed response plan, you can minimize the impact and prevent further damage to your organization’s reputation.
A good response plan should include details on how to detect, contain, and mitigate the effects of an attack. It should also outline who is responsible for each stage of the process and provide contact information for key personnel who can assist with the response effort. By having a clear understanding of what needs to happen during an incident, your team can act quickly and effectively.
Components Of A Response Plan
The components of a response plan vary depending on various factors, such as the size of the organization, type of data involved, and nature of potential threats.
Incident Response Team

An incident response team (IRT) is a group of professionals responsible for managing and responding to data security incidents. Incident response teams are typically composed of various departments within an organization, including IT, legal, communications, and human resources.
The IRT’s first task is to identify and contain the incident before it spreads further into the system. This involves gathering information about the incident, analyzing its scope and impact on critical business functions or systems. Once containment has been achieved, the IRT can begin restoring normal operations while reducing any potential risks associated with data breaches.
Having an effective incident response team in place can significantly reduce downtime following a data security breach. The team should have a clear understanding of their roles and responsibilities during a crisis situation. Regular training sessions should be conducted to ensure that all members are up-to-date with current cybersecurity threats and best practices in responding to them promptly.
Communication Plan
A communication plan outlines the steps that should be taken to communicate with stakeholders in the event of an incident, including employees, customers, partners, regulators, and the media. The goal of a communication plan is to ensure that everyone affected by the incident receives clear and accurate information about what happened and what steps are being taken to address it.
The first step in developing a communication plan is to identify all potential stakeholders and determine their contact information. This includes internal contacts such as executives, IT staff, legal counsel, and human resources personnel as well as external stakeholders like customers, vendors, regulatory agencies or law enforcement officials. Once all relevant parties have been identified and contacted details about the incident must be shared with them immediately. This can include the nature of the breach or attack as well as any measures being taken to contain it.
Avoid downplaying or hiding facts from those who are affected by an incident. It’s essential for businesses to take responsibility for their mistakes transparently without blaming others.
Data Backup Plan
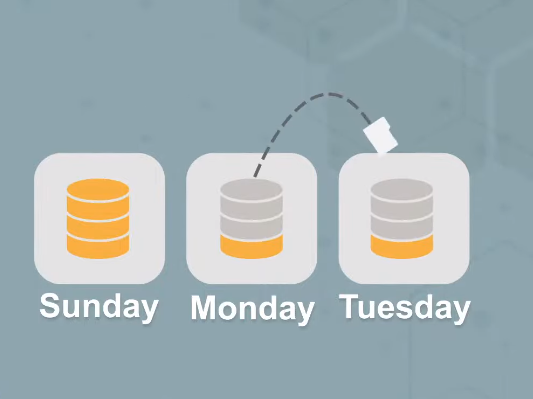
A data backup plan involves creating a routine process for backing up important data and storing it in secure locations, such as off-site servers or cloud storage solutions. The goal of a backup plan is to ensure that critical business information remains accessible even in the event of a security incident.
When developing a data backup plan, consider the type of data that needs to be backed up, how often backups should occur, and who will be responsible for managing the process. Organizations should also test their backup systems regularly to ensure they are functioning properly and can effectively restore lost data if needed.
Regularly Testing and Updating the Response Plan
Updating the response plan is equally important as technology and tactics change frequently. Organizations should reassess their threat landscape regularly and revise their plans accordingly. For instance, if an organization deploys new software or hardware solutions, it may need to update its procedures for managing them in case of a data breach. Similarly, if there are changes in regulatory requirements or industry best practices, the response plan must reflect those changes.
Detecting a Data Security Incident
Signs of a Data Security Incident
Signs of a Data Security Incident include unusual system activities, unexpected error messages or pop-ups, unauthorized access attempts or failed login attempts, and suspicious network traffic. Other warning signs may include missing files, unusual changes to file sizes or names, and unexplained modifications to system configurations.
In addition to these technical indicators, there are also behavioral clues that may indicate a security breach. For example, an employee suddenly refusing to take time off or abruptly resigning from their position could be hinting at something more sinister happening behind the scenes. Similarly, employees exhibiting secretive behavior around their workstations or being unusually defensive when questioned about their activities can also be warning signs of potential data breaches.
Importance of Early Detection
The sooner an issue can be identified, the faster it can be addressed and resolved before any significant damage or loss occurs. This highlights the importance of implementing proactive monitoring systems that can detect potential threats before they become a major problems.
In addition to preventing further harm, early detection also allows for a more effective response strategy. With timely identification of the issue, companies can quickly gather relevant information and assess the extent of the breach. This enables them to determine what actions need to be taken, such as notifying affected parties and implementing necessary safeguards against future incidents.
Monitoring and Alert Systems
Monitoring and alert systems provide real-time visibility into the security posture of an organization’s network, applications, and systems. These systems can detect anomalies and potential threats before they cause damage to the organization’s data assets.
When it comes to monitoring and alert systems, there are two primary types: intrusion detection systems (IDS) and security information event management (SIEM). IDS monitors network traffic for signs of unauthorized access or malicious activity while SIEM aggregates logs from various sources across the enterprise to identify patterns that may indicate a security breach.
Containing A Data Security Incident
Prioritizing and Assessing the Incident
Identify the type of data that has been compromised, such as personal information or financial records, and determine the extent of the breach. This helps prioritize which actions should be taken first, ensuring that the most sensitive and critical data is addressed immediately. The response team should also assess whether there are any legal or regulatory requirements that they need to comply with.
Once the priority areas have been identified, it’s important to gather as much information about the attack as possible. This includes collecting system logs, reviewing access controls for suspicious activity, and analyzing any malware found on systems affected by the breach. Identifying how attackers gained access to your network or system can help prevent future attacks by addressing vulnerabilities in your security posture.
Isolating the Affected Systems and Networks
Disconnect the compromised devices from the rest of the network to prevent further damage and contain the incident. Isolation can be done physically, by unplugging cables or shutting down machines, or remotely through network segmentation.
When isolating affected systems and networks, consider potential consequences such as loss of critical services, data corruption or deletion, and system availability. To minimize these effects, organizations should have a pre-established plan for isolating affected systems that takes into account various scenarios and potential impacts on business operations.
Escalating the Incident
One of the most important steps in responding to an incident is escalating it to the appropriate parties within your organization. This includes notifying management, IT staff, legal counsel, and any other relevant departments.
To escalate an incident, determine its severity level. This will help you decide which individuals or teams need to be notified immediately versus those who can wait for additional information before being informed. It’s also important to document every step of the escalation process, including who was notified and when.
Collaborating with External Parties
In many cases, companies may not have the necessary expertise or resources to handle complex security breaches on their own. As such, it is important to identify and collaborate with external partners such as cybersecurity firms, legal counsel, and law enforcement agencies.
When selecting an external partner, consider their level of experience in handling data security incidents similar to your own. You should also ensure that they can provide ongoing support throughout the entire response process. For instance, cybersecurity firms can help identify the source of the breach and contain it from further spreading while law enforcement officers can provide legal guidance on how to report the incident.
Managing the Impact of the Incident
Assess the impact of the incident on your business operations, customers, employees, and stakeholders. Identify any critical business processes that may have been disrupted or compromised as a result of the breach. This will help you prioritize your response efforts and allocate resources effectively.
Investigating A Data Security Incident
Goals of an Investigation
The goals of an investigation during a data security incident are multifaceted. The investigation aims to determine the extent of the breach, identifying what information was compromised and how it may have been accessed. This helps organizations understand the scale of the potential damage caused by such an incident. The investigation also seeks to identify who or what caused the breach, which can help prevent future incidents from occurring.
Another goal of an investigation is to assess whether any legal obligations or industry regulations have been violated. This includes determining whether there were any failures in compliance with data protection laws such as GDPR, CCPA, HIPAA, etc. In addition to legal ramifications, investigations also help maintain trust between companies and their customers by reassuring them that measures are being taken to protect their personal information.
Investigations seek to provide recommendations on how organizations can improve their existing security protocols and processes. By looking back at what went wrong during an incident response plan (IRP), organizations can learn from their mistakes and strengthen their defenses against future attacks.
Collecting and Analyzing Evidence
It is essential to collect all relevant data and document any suspicious activity. This includes reviewing system logs, network traffic, and user activity logs. Once the information has been gathered, it can be analyzed to identify patterns or indicators of compromise.
The analysis phase involves examining the collected evidence in detail to determine how the attack occurred and what data was impacted. This process may include forensics investigations on individual computers or devices that were involved in the incident. The goal is to determine whether any sensitive data was accessed or stolen during the breach.
Conducting Interviews
Before starting an interview, prepare questions in advance and have a clear understanding of what information you need to gather. Begin by explaining why you are conducting the interview and assure confidentiality. Active listening skills are crucial, allowing interviewees to speak candidly while maintaining focus on key issues.
After each interview, document your findings carefully for future reference. Be sure not to draw conclusions too quickly or make assumptions based on limited information. Instead, stay open-minded and use your findings as a basis for further investigation into any potential risks or vulnerabilities that may exist within your organization’s infrastructure.
Determining The Root Cause
To determine the root cause of a data security incident, assessment tools such as forensic investigation, vulnerability scanning, and risk assessments are often utilized. These tools help in identifying vulnerabilities in existing systems and processes that could be exploited by attackers. The results obtained from these assessments can then be analyzed to develop accurate conclusions about what went wrong during the incident.
Identifying the Extent of the Compromise
To identify the extent of the compromise, organizations can use various tools and techniques such as log analysis, network traffic monitoring, and forensic investigation. These methods provide insights into how attackers gained access to sensitive data, what actions they took while inside a system, and whether any other systems were compromised.
Evaluating The Response To A Data Security Incident
Reviewing the Effectiveness of the Response Plan
Review the effectiveness of the response plan after each incident. This review should focus on identifying areas that worked well and those that need improvement.
An effective review should involve all parties involved in executing the response plan, including IT staff, legal counsel, and any third-party vendors or consultants. It’s important to document findings and recommendations from this review process to inform future updates to the response plan.
Identifying Areas for Improvement
Once you have identified the areas of weakness, you can begin to implement appropriate measures that will help mitigate future risks. For instance, you may need to install additional software patches, upgrade hardware components or invest in employee training programs geared toward security awareness and safe internet practices.
FAQs
What Are The Legal And Regulatory Obligations For Responding To A Data Security Incident?
In the aftermath of a data security incident, companies must comply with strict legal and regulatory obligations to address the situation. The first step is to notify affected individuals, which may be required by state and federal laws such as HIPAA or GDPR. Companies must also report the breach to relevant government agencies, such as the FTC or SEC. Failure to comply with these notification requirements can result in hefty fines and reputational damage.
Companies may also have contractual obligations with customers or vendors that require them to report any data breaches. These contracts should be reviewed carefully before responding to a security incident. Additionally, businesses that handle credit card information are subject to PCI-DSS (Payment Card Industry Data Security Standard) regulations, which require compliance reporting within specific time frames after a data breach has occurred.
What Are The Components Of A Response Plan?
A response plan should include several key components, including specific roles and responsibilities for members of the incident response team, communication protocols for notifying stakeholders, steps for containing the breach and mitigating damage, procedures for conducting an investigation into the breach, and a plan for returning systems and operations to normal.
How Often Should A Response Plan Be Tested And Updated?
It is recommended that response plans be tested at least once a year or whenever there are significant changes to the organization’s operations. Additionally, response plans should be updated regularly to incorporate any new threats, vulnerabilities, or risks identified during testing.
What Is The Goal Of An Investigation?
The goal of an investigation is to determine the scope and impact of a data security incident. It involves gathering and analyzing evidence to identify the cause, extent, and potential consequences of the incident. This process helps organizations understand what happened, how it happened, who was affected, and what needs to be done to prevent similar incidents in the future.
What Are Some Post-Incident Activities That Should Be Conducted?
After a data security incident, there are several post-incident activities that should be conducted to help minimize the damage caused by the event. One of the first steps is to conduct a thorough investigation into what happened and how it happened. This will involve examining all available evidence, including log files, system backups, and other relevant data sources.
Another key post-incident activity is to determine what data may have been compromised during the incident. This will likely involve identifying any confidential or sensitive information that was accessed or stolen during the attack. Once this has been done, appropriate measures can be taken to protect affected individuals and prevent further damage from occurring.
Review and update your organization’s existing security policies and procedures in light of the incident. This might include implementing new technical controls or training employees on best practices for preventing future incidents.
Conclusion
Responding to a data security incident requires prompt action and careful planning. It is important to have a well-documented incident response plan in place before an incident occurs. This will help your organization respond quickly and efficiently should you experience a data breach.
Additionally, communication is key during the incident response process. You should ensure that all stakeholders are informed of the situation promptly and accurately. This includes employees, customers, and partners who may be affected by the breach.
