
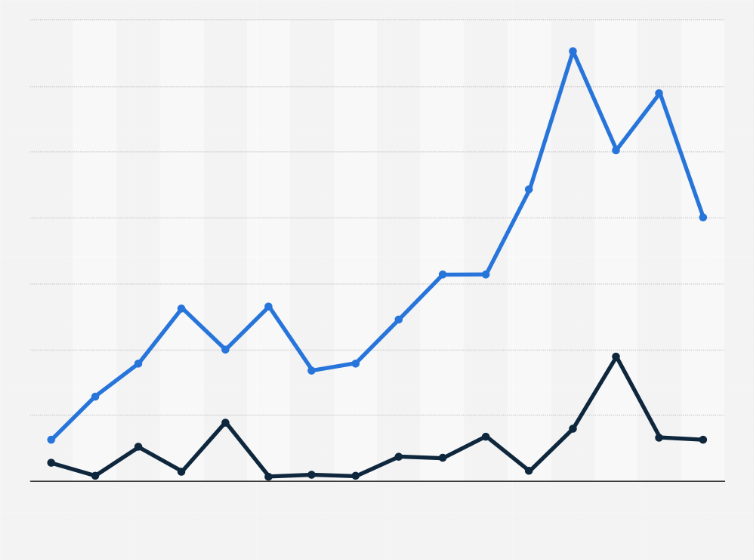
There are absolutely no surprises that 2013 was even worse than 2012 regarding the constantly growing issue of data breach. There is no such categorization such as small business, large firm, government, private or individual, every kind of business and individual can be a victim of a data breach that has been proven time and time again. In the year of 2012, almost 75 percent of the data breaches victimized individuals and small scale companies, which is such a huge number. The problem of data breach is known as a global problem because no border no walls can keep you protected against it other than your data security barriers and data security software such as Folder Lock.
In the recent past year, there have been more than 47,000 data security incidents, according to the Verizon’s reports, 621 data breach incidents have been confirmed. The incidents of data breach have been pooled by international destinations and more than 25 countries’ computer users have become its prey. The majority of the culprits is situated in the US as most of the data breach incidents have been headlined from that region, other than that, eastern Europe is also a base from where these hackers act. Bulgaria, Romania and Russian Federation are the pieces of land on which many of these crooks are located.
Experts have always warned the computer users that, it is necessary to have the knowledge of a data breach as soon as possible in order to lessen the severity of loss. But, a bitter truth is that more than 69 percent of the time the data that gets breached is pointed out by a third party. Another 9 percent of those incidents of breach are observed by the customers and just remaining 22 percent of the time company itself comes to know that their records have been compromised. There are some classifications of data thieves that are given below.
The classifications of data thieves are according to the motives, target setting and the tools they use. The first kind of data thieves is Activists. Their goal of stealing data is just to embarrass their targets and make them suffer with no intention of earning or making profit. They are opportunistic and use very basic methods to get the data.
The other kind of data thieves is actually the criminals that steal data to earn, to exploit your data for their good and make you suffer a loss. They do not have intended targets and attack people at large. They know very well which kind of data can benefit them, so they look to get their desired sort of data. They are devilish genius and use comparatively latest tools to break through databases.
The third of data thieves are not actually thieves, they are professional hackers hired by the government to work for them. They usually have pin pointed targets and steal just the kind of data the government wants them to steal. They are the ones that are equipped with the latest hacking tools and are extremely good in their job.
The Verizon’ report has clearly suggested that the situation regarding data breach is just getting worse day by day and computer users have to take good care of their data. Hackers are present in every part of the world and performing their mal activities quite boldly.
Describe A Data Breach
A data breach is an incident in which sensitive, confidential, or otherwise protected data is accessed, used, or disclosed without authorization. It can involve the loss or theft of personal information, financial information, intellectual property, or other sensitive data. Data breaches can have serious consequences, such as identity theft, financial loss, and reputational damage.
Most Common Cause Of A Data Breach
The most common cause of a data breach is a lack of proper security measures, such as weak passwords, lack of encryption, and inadequate access control. Other causes of data breaches include malicious attacks, such as phishing, malware, and ransomware, as well as accidental data leakage, such as employee negligence or an unsecured server.
Impact Of Data Breach
The impact of a data breach can be wide-reaching and long-lasting. It can cause financial losses, reputational damage, and legal consequences. Additionally, it can lead to identity theft, data loss, and a decrease in customer trust. In some cases, the breach can even result in the suspension of operations or closure of a business.
Data Breach A Threat Or Risk
Data breach is both a threat and a risk. A threat is a potential danger or harm that can be caused by a malicious attack or data breach. A risk is a potential loss or negative impact that can result from a threat.
Responsible For Data Breach
The responsibility for a data breach usually lies with the organization or individual that owns or controls the data. This includes the organization that stores or processes the data, as well as any third-party service providers that have access to the data. Organizations must ensure that they have adequate security measures in place to protect the data they store and process, as well as to prevent unauthorized access or use. Additionally, organizations should also have a plan in place to respond to a data breach in the event one occurs.
Top Data Breaches
1. Equifax: In 2017, Equifax, one of the three major credit reporting agencies, announced a massive data breach that exposed the personal information of 143 million people.
2. Marriott: In 2018, Marriott revealed that hackers had accessed the Starwood guest reservation database and exposed the personal information of up to 500 million customers.
3. Yahoo: In 2013, Yahoo reported that a data breach had exposed the personal information of up to three billion user accounts.
Ways To Prevent Data Breach
Data breaches can be prevented by implementing strong security measures such as encryption, two-factor authentication, regular security audits, and incident response plans. Organizations should also ensure that their systems are up-to-date with the latest security patches, and that their employees are trained in cybersecurity best practices. Additionally, organizations should have a comprehensive data protection policy in place and regularly monitor for any suspicious activity.
Importance To Avoid Data Breaches
Data breaches are a serious security threat that can have serious consequences for organizations. They can lead to the loss of sensitive information, financial losses, reputational damage, and legal liabilities. Data breaches can also be used to launch malicious attacks, such as ransomware, or to gain access to confidential information. By avoiding data breaches, organizations can protect their data, their customers, and their reputation.
Steps To Improve Data Security
1. Implement strong access control measures.
3. Regularly update security systems and software.
4. Educate employees on data security best practices.
5. Monitor data access and usage.
6. Use two-factor authentication.
7. Regularly back up data.
8. Use firewalls and other security measures to protect networks.
9. Perform regular security audits.
10. Limit access to sensitive data to
Steps Of Data Breach
1. Detection: Identifying a data breach has occurred.
2. Containment: Limiting the spread of the breach.
3. Investigation: Determining the cause and extent of the breach.
4. Notification: Notifying affected individuals and/or organizations.
5. Remediation: Taking steps to prevent a similar breach from occurring in the future.
Top Stages Of Data Analysis
1. Data collection: Collecting and organizing the data.
2. Data cleaning: Removing any outliers or inconsistencies.
3. Data exploration: Exploring the data to gain insights.
4. Modeling: Building and testing models to predict outcomes.
5. Evaluation: Assessing the accuracy and reliability of the model.
6. Deployment: Making the model available for use in real-world applications.
7. Monitoring: Monitoring the model’s performance
Best Ways To Respond To A Data Breach
1. Notify affected individuals and organizations: It is important to notify individuals and organizations that have been affected by the data breach as soon as possible.
2. Investigate the breach: Conduct an investigation to determine the cause of the breach and identify any vulnerabilities that may have allowed the breach to occur.
3. Take corrective action: Implement measures to prevent similar breaches from occurring in the future.
4. Notify law enforcement: Depending on the severity of the breach
How Common Are Data Breaches?
Data breaches are becoming increasingly common. According to the Identity Theft Resource Center, there were 1,473 data breaches in the United States in 2020, a 44% increase from 2019. The most common type of data breach was hacking, which accounted for nearly half of all data breaches.
Country With Most Data Breaches
The United States has the most data breaches of any country in the world. According to the Identity Theft Resource Center, the United States accounted for more than half of all data breaches in 2020. Other countries with high numbers of data breaches include China, the United Kingdom, and India.
Examples Of Data Breaches
Examples of data breaches include:
• Hacking: Unauthorized access to a system or network, often with malicious intent.
• Insider threat: Unauthorized access by an employee or contractor.
• Social engineering: Manipulation of individuals to gain access to sensitive information.
• Malware: Malicious software used to steal or damage data.
• Data loss: Accidental or intentional loss of data due to human error or malicious intent.
Difference Between Security Breach And Data Breach
A security breach is the unauthorized access to a system or network, which can lead to a data breach. A data breach is the unauthorized access to, use, or disclosure of sensitive information. Security breaches can lead to data breaches if the attacker gains access to the sensitive information. Data breaches can also occur without a security breach if the sensitive information is not properly secured.
Top Steps In Managing A Breach
1. Identify the breach: Identify the source of the breach, the type of data affected, and the extent of the breach.
2. Contain the breach: Secure the affected system and limit the spread of the breach.
3. Investigate the breach: Investigate the cause of the breach and identify the responsible parties.
4. Remediate the breach: Implement measures to prevent future breaches and restore any affected data.
Where Are Data Breaches Reported?
Data breaches must be reported to the relevant authorities, such as the Information Commissioner’s Office (ICO) in the UK, the Federal Trade Commission (FTC) in the US, and other data protection authorities in other countries. Depending on the severity of the breach, companies may also be required to notify customers and the general public.
Most Common Causes Of Data Breaches
1. Human Error: Human error is one of the most common causes of data breaches. This includes employees accidentally exposing confidential data, failing to follow security protocols, or being tricked into giving away sensitive information.
2. Malware and Hacking: Malware and hacking are also common causes of data breaches. Malware is malicious software that can be used to steal data, and hackers can exploit vulnerabilities in a system to gain access to confidential information.
Powered by NewSoftwares.net
