The best method for securely wiping data combines physical destruction and software-based overwriting techniques. Degaussing and Tools like DBAN (Darik’s Boot and Nuke) can be used.
Data security has become a critical concern in today’s increasingly digital world. With the ever-growing number of data breaches and privacy concerns, ensuring the secure deletion of sensitive information is paramount. We will explore the best methods for securely wiping data and the implications of inadequate data deletion.
Understanding the Importance of Securely Wiping Data
In today’s digital age, where data plays a crucial role in our personal and professional lives, it is imperative to comprehend the significance of secure data deletion fully. The risks associated with inadequate data deletion cannot be ignored, as they can potentially cause serious consequences.
When data is not securely wiped, it becomes vulnerable to falling into the wrong hands. This can lead to many issues, including identity theft, financial fraud, and unauthorized access to sensitive information. The consequences of such breaches can be devastating, both on an individual level and for organizations.
Risks of Inadequate Data Deletion
One of the major risks of inadequate data deletion is the potential for unauthorized access. Simply deleting data using regular methods, such as sending it to the recycle bin or the delete button, is not enough to ensure its complete eradication. Specialized software can often recover deleted data, leaving sensitive information vulnerable to exploitation.
Imagine an individual selling their old computer without securely wiping the data stored on the hard drive. With malicious intent, the new owner could easily retrieve deleted files and gain access to personal photos, financial records, or even confidential work documents. This highlights the importance of taking extra precautions when deleting data.
Another significant risk of inadequate data deletion is the possibility of data breaches. When storage media, such as hard drives or USB drives, are discarded or repurposed without proper wiping, unauthorized individuals can still retrieve the information they contain. This can compromise personal, financial, or corporate data, leading to severe consequences for individuals and organizations.
Legal and Ethical Implications of Data Mismanagement
The legal and ethical ramifications of failing to wipe data securely cannot be overstated. Organizations that mishandle sensitive information can face severe legal consequences, including hefty fines, lawsuits, and damage to their reputation.
In recent years, data protection regulations, such as the General Data Guard Regulation (GDPR) in the European Union, have been implemented to ensure that individuals’ data is handled responsibly. Disappointment to comply with these regulations can result in significant penalties. Therefore, it is a legal obligation and an ethical responsibility to delete data to protect individuals’ privacy securely.
Respecting individuals’ privacy and safeguarding their data is an ethical imperative. Whether it is personal information, financial records, or confidential business data, mishandling and inadequate deletion can lead to breaches of trust and erosion of confidence in organizations.
In conclusion, understanding the importance of securely wiping data goes beyond mere compliance with regulations. It is about protecting sensitive information, preventing unauthorized access, and upholding ethical standards. Individuals and organizations can mitigate the risks associated with data mismanagement and ensure the privacy and security of valuable information by taking the necessary steps to delete data securely.
Different Methods of Data Deletion
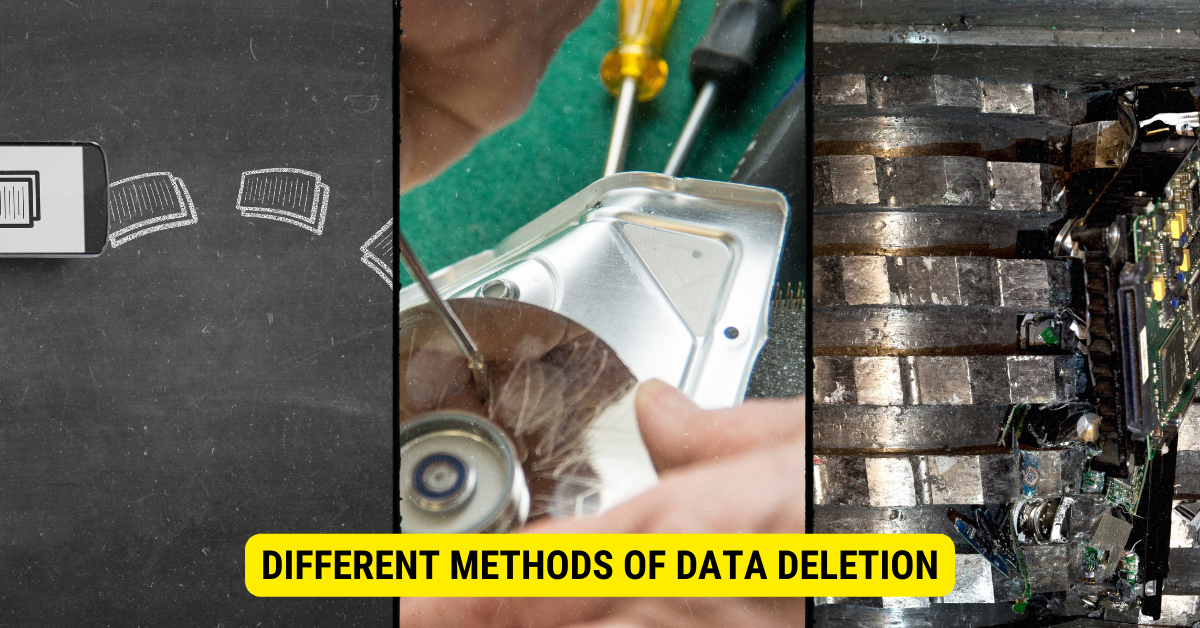
When it comes to securely wiping data, there are several methods available. Each method has advantages and limitations; understanding them is essential in determining the best approach for your needs.
Data deletion is critical to security, ensuring unauthorized individuals cannot access sensitive information. In this expanded version, we will explore the different data deletion methods in more detail, providing a comprehensive understanding of their effectiveness and suitability.
Simple Deletion and Its Limitations
The simplest method of data deletion involves deleting files or formatting storage media. This method is commonly used by individuals who want to free up storage space or eliminate unwanted data. However, it is important to note that simple deletion is not foolproof, as the data can often be easily recovered using specialized software.
When you delete a file or format a storage device, the operating system marks the space previously occupied by the data as accessible for new data to be written. Until new data is written over the old data, it remains intact and recoverable. If someone gains access to your storage device before new data overwrites the old data, they can retrieve the supposedly deleted information.
Therefore, simple deletion is not recommended for securely wiping sensitive information, such as personal documents, financial data, or confidential business files. If you need to ensure that your data cannot be recovered, it is advisable to use more advanced data deletion methods.
Formatting and Its Effectiveness
Formatting a storage device is a more advanced method of data deletion. It involves erasing all existing data and preparing the storage media for future use. When you format a storage device, the operating system not only marks the space previously occupied by the data as available but also performs a low-level format that overwrites the entire storage device with zeros or random data.
This method provides a higher level of data security compared to simple deletion. However, it is important to note that even formatting is not entirely secure. Advanced recovery techniques can often recover formatted data, especially if the formatting process is not performed correctly or the storage device is not overwritten with random data.
Therefore, while formatting can be effective in most cases, it is still not recommended for securely wiping sensitive information that needs to be permanently deleted. For such cases, a more robust method of data deletion is required.
Physical Destruction of Storage Media
For the most secure method of data deletion, physical destruction of storage media is recommended. This method ensures the data is destroyed, rendering it unreadable and irrecoverable.
Physical destruction involves physically damaging the storage media to such an extent that it becomes impossible to retrieve any data. Several physical destruction methods include shredding, pulverizing, or incinerating the media.
Shredding is a common method for destroying hard drives, solid-state drives, and other physical storage devices. It involves feeding the media through a high-powered shredder that reduces it to small pieces, making data recovery virtually impossible.
Pulverizing is another effective method that crushes the storage media into tiny particles. This method ensures that even the smallest media fragments are destroyed, leaving no chance of data recovery.
Incineration is commonly used to destroy optical discs, such as CDs and DVDs. By subjecting the discs to extreme heat, they are melted down, rendering the data layer unreadable.
It is important to note that physical destruction is irreversible, and once the storage media is destroyed, the data cannot be recovered. Therefore, ensure you have backed up any important data before proceeding with physical destruction.
While physical destruction is the most secure method of data deletion, it may not be practical or cost-effective for all situations. It is typically used for highly sensitive information, such as classified government or confidential corporate data.
In conclusion, simple deletion and formatting are insufficient for permanently deleting sensitive information when securely wiping data. For the highest level of data security, physical destruction of storage media is recommended. Understanding each method’s advantages and limitations allows you to choose the best approach for your specific needs.
Introduction to Secure Data Wiping
 Secure data wiping is a comprehensive method of data deletion that aims to ensure that sensitive information is permanently and irreversibly erased. Through various techniques, it guarantees that data cannot be recovered by any means, providing a higher level of data security.
Secure data wiping is a comprehensive method of data deletion that aims to ensure that sensitive information is permanently and irreversibly erased. Through various techniques, it guarantees that data cannot be recovered by any means, providing a higher level of data security.
When protecting sensitive information, secure data wiping is crucial in safeguarding data privacy and preventing unauthorized access. Whether it’s personal data, financial records, or confidential business information, securely wiping data ensures that it is beyond the reach of malicious individuals.
What is Secure Data Wiping?
Secure data wiping, or erasure refers to overwriting stored information with random or predefined patterns. This overwriting process makes it impossible for unauthorized parties to recover the original data, even using specialized recovery software.
Imagine you want to dispose of an old computer or sell your smartphone. Simply removing files or formatting the device is not enough to guarantee the complete removal of sensitive data. Sophisticated data recovery techniques can easily retrieve deleted files if they have not been securely wiped.
Secure data wiping goes beyond simple deletion or formatting. It involves overwriting the existing data with random or fixed patterns, ensuring that the original information is overwritten and permanently eradicated. This leaves no traces behind, making it virtually impossible for anyone to reconstruct the data.
How Does Secure Data Wiping Work?
Secure data wiping utilizes advanced algorithms and patterns to overwrite data on storage media multiple times. Repeatedly overwriting the data with random or fixed patterns permanently eradicates the original information, leaving no traces behind. This ensures the data cannot be reconstructed, making it ideal for securely wiping sensitive information.
One common method used in secure data wiping is the Gutmann method, named after its creator Peter Gutmann. This method involves overwriting the data with 35 patterns, each designed to scramble the original information thoroughly. The Gutmann method is known for its thoroughness and effectiveness in securely wiping data.
Another widely used method is the DoD 5220.22-M standard, known by the U.S. Department of Defense. This method involves overwriting the data with three patterns, ensuring the original information is completely overwritten and irrecoverable.
Secure data wiping can be applied to many storage media, counting hard drives, solid-state drives (SSDs), USB drives, and even mobile devices. Each storage medium requires specific techniques and algorithms to ensure complete data erasure.
It is important to note that secure data wiping is not limited to physical storage media. Cloud-based storage systems also employ data-wiping techniques to ensure the secure deletion of data from their servers. This is particularly crucial for organizations relying on cloud storage for sensitive data.
In conclusion, secure data wiping is vital in today’s digital age. It delivers a reliable and effective method for permanently erasing sensitive information, protecting individuals and organizations from potential data breaches. By utilizing advanced algorithms and patterns, secure data wiping ensures that data is beyond recovery, offering peace of mind and enhanced data security.
Comparing Secure Data Wiping Methods
Various methods can be used to achieve secure data wiping. Each technique comes with its unique advantages and considerations.
Software-Based Data Wiping
Software-based data wiping relies on specialized software applications to overwrite data on storage media. These applications offer different algorithms and patterns to ensure secure deletion. They are often easy to use and provide thorough documentation on data erasure.
Hardware-Based Data Wiping
Hardware-based data wiping involves specialized hardware devices that physically overwrite data on storage media. These devices provide an added layer of assurance as they are specifically designed for secure data wiping and comply with industry standards.
Cryptographic Erase
Cryptographic erase involves encrypting the entire storage media before deleting the encryption key. This method ensures that the data becomes unreadable without the encryption key, rendering it effectively useless to any unauthorized party.
Best Practices for Securely Wiping Data
Knowing when to use each method and following best practices is crucial in achieving secure data wiping.
When to Use Each Method
In general, simple deletion and formatting should be avoided for securely wiping sensitive information. Hardware-based data wiping and cryptographic erase are suitable for most scenarios. However, for the highest level of security, physical destruction of storage media is recommended when dealing with extremely sensitive data.
Ensuring Complete Data Erasure
Regardless of the method used, it is important to verify the effectiveness of the data-wiping process. This can be done by performing verification checks, such as using specialized software to ensure data cannot be recovered.
Key Takeaways
- Simply deleting files does not remove the actual data.
- Overwriting data multiple times increases the security of the wipe.
- Physical destruction, like shredding or degaussing, ensures data is irrecoverable.
- Software tools like DBAN can be used for secure data wiping.
- Always verify after wiping to ensure no data remnants.
FAQs:
Q: Does simply deleting a file remove its data?
A: No, deleting only removes the reference to the file, but the data remains overwritten.
Q: How many times should data be overwritten for security?
A: Industry standards often recommend overwriting data multiple times, usually 3 to 7 times, depending on the sensitivity of the information.
Q: What is degaussing?
A: Degaussing is a method that uses magnets to disrupt the magnetic domains on a storage medium, rendering the data unreadable.
Q: Are there software tools for secure data wiping?
A: Tools like DBAN (Darik’s Boot and Nuke) can be used.
Q: Is physical destruction of a hard drive necessary?
A: While not always necessary, physical destruction ensures the data is irrecoverable and is often recommended for highly sensitive information.
Conclusion
In conclusion, securely wiping data is essential in today’s data-driven world. Understanding the risks of inadequate data deletion, exploring different methods, and following best practices are all crucial steps toward ensuring the highest level of data security. By implementing the appropriate secure data wiping methods and taking proper precautions, individuals and organizations can guard sensitive information from falling into the wrong hands and mitigate the legal and ethical implications of data mismanagement.
