In a PKI (Public Key Infrastructure) encryption method, the public key is used to encrypt the data.
Data security has become a paramount concern for individuals, businesses, and governments in today’s interconnected digital world. The need to safeguard sensitive information during transmission has led to the development of robust encryption methods. One such method is Public Key Infrastructure (PKI) encryption, which ensures secure communication and data exchange over unsecured networks. We will delve into the workings of PKI encryption and address the key question, “Which key encrypts the data in PKI?”
Understanding PKI Encryption
What is PKI?
PKI stands for Public Key Infrastructure, a set of policies, procedures, and technologies for managing cryptographic keys and digital certificates. It involves asymmetric encryption, where each user or entity possesses a unique pair of cryptographic keys – public and private keys.
How does PKI work?
PKI operates on the principle of two distinct keys – the public key, which is widely distributed and used for encryption, and the private key, which is kept confidential and used for decryption. The public key can be freely shared with others, while the private key is known only to the owner.
Which Key Encrypts the Data in PKI?
In PKI, the data is encrypted using the recipient’s public key. This means anyone can encrypt data intended for the recipient, but only the recipient with the corresponding private key can decrypt and access the original data.
The Role of the Public Key
In PKI encryption, the public key is used to encrypt the data. When someone wants to send encrypted data to a recipient, they use the recipient’s public key to encrypt the data before transmission. Once encrypted, the data becomes unreadable to unauthorized users, ensuring secure communication over untrusted networks.
Why the Private Key is Not Used for Encryption
The private key is kept confidential and is used for decryption, not encryption. Using the private key for encryption would defeat the purpose of PKI, as anyone with the public key could then decrypt the data, compromising its security.
Public Key and Private Key
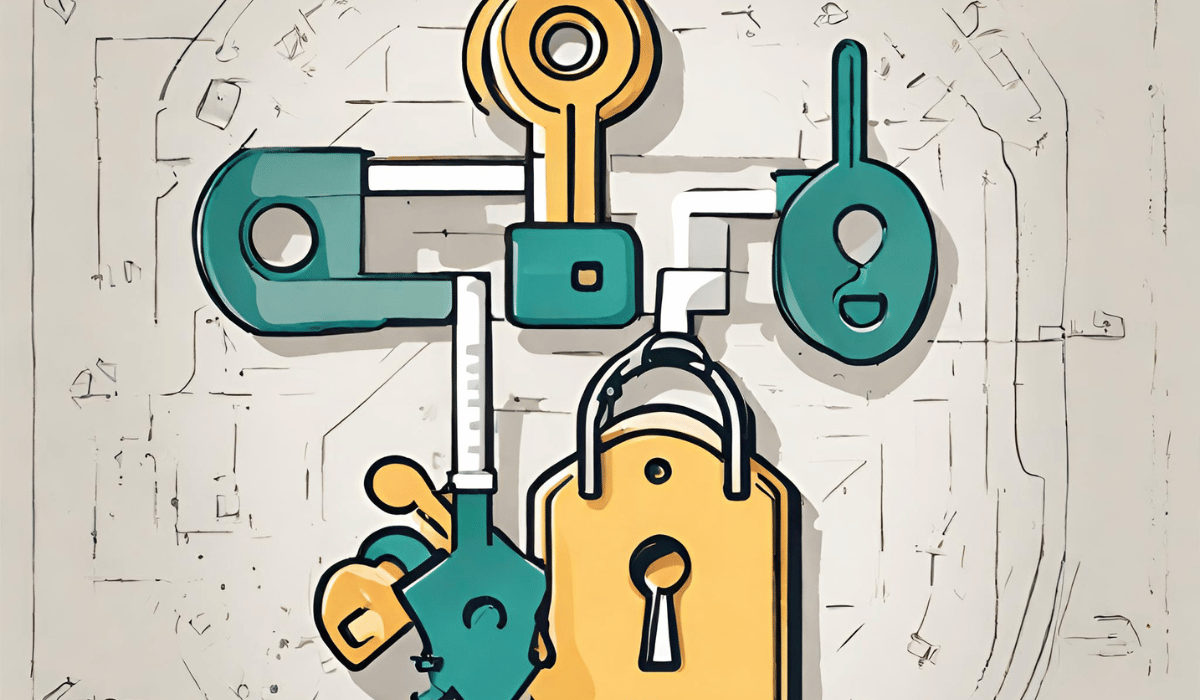
The public key and private key form a key pair that is mathematically related. Any data encrypted with the public key can only be decrypted using the corresponding private key and vice versa. This asymmetric encryption ensures data security and confidentiality.
Advantages of PKI Encryption
Data Security and Confidentiality
One of the primary advantages of PKI encryption is its ability to provide strong data security and confidentiality. By using asymmetric encryption, sensitive information remains protected from unauthorized access.
Digital Signatures
PKI also enables the creation of digital signatures, which verify the authenticity and integrity of digital documents or messages. Digital signatures are crucial for ensuring the origin of data and detecting any tampering or modifications.
Authentication and Non-Repudiation
PKI facilitates user authentication, ensuring individuals can be verified and granted access to specific resources or systems. Additionally, non-repudiation ensures that parties cannot deny their involvement in a digital transaction.
Implementing PKI Encryption
Generating Key Pairs
The process of implementing PKI starts with generating key pairs – the public key and the private key. These keys are unique to each user or entity and form the basis for secure communication.
Certificate Authorities (CAs)
Certificate Authorities play a vital role in issuing digital certificates that bind the public key to a specific entity to establish trust and authenticity. CAs are responsible for validating identities and managing the certificate lifecycle.
Certificate Lifecycle Management
Managing digital certificates is crucial in PKI. This involves certificate issuance, revocation, and renewal to ensure a smooth and secure PKI environment.
Common Uses of PKI Encryption
Secure Communication
PKI is widely used to secure communication channels, including email encryption, secure messaging, and virtual private networks (VPNs).
Secure Online Transactions
E-commerce platforms and online banking rely on PKI encryption to protect sensitive financial data during online transactions.
Digital Certificates for Websites
Websites use PKI to obtain SSL/TLS certificates, ensuring secure and encrypted connections between users and the website.
Challenges and Considerations
Key Management
Managing many cryptographic keys can be challenging, and proper key management practices are essential to maintain security.
Revocation and Expiry of Certificates
Certificate revocation and expiry mechanisms are critical to invalidate compromised or outdated certificates promptly.
Alternatives to PKI Encryption
Symmetric Encryption
Unlike asymmetric encryption, Symmetric encryption uses a single key for encryption and decryption. It is commonly used for bulk data encryption due to its efficiency.
Hybrid Encryption
Hybrid encryption combines symmetric and asymmetric encryption to optimize security and performance in various scenarios.
Short Summary:
In PKI encryption, the public key is used to encrypt the data. Public Key Infrastructure (PKI) is a robust encryption method for securing data during transmission over unsecured networks. It employs asymmetric encryption with unique key pairs, ensuring that data can only be decrypted by the intended recipient possessing the corresponding private key. PKI provides strong data security and authentication, making it valuable for safeguarding sensitive information and validating the authenticity of digital documents. It plays a crucial role in securing communication channels and online transactions and maintaining trust on the internet.
FAQs
Is PKI encryption suitable for securing sensitive data during transmission?
PKI encryption is highly suitable for securing sensitive data during transmission, as it ensures data confidentiality and protection against unauthorized access.
Can anyone encrypt data using a recipient’s public key?
Yes, anyone can encrypt data using the recipient’s public key, but only the recipient with the corresponding private key can decrypt and access the original data.
What role do Certificate Authorities (CAs) play in PKI?
Certificate Authorities (CAs) issue digital certificates that bind the public key to a specific entity, establishing trust and authenticity within the PKI system.
How does PKI facilitate user authentication?
PKI enables user authentication by validating identity through digital certificates and cryptographic keys.
Conclusion
In PKI encryption, the public key is used to encrypt the data. The Public Key Infrastructure (PKI) encryption method is fundamental to modern data security. The public key is crucial in encrypting data, ensuring secure communication and data exchange between users and systems. By leveraging asymmetric encryption and digital certificates, PKI empowers organizations to protect sensitive information, authenticate users, and maintain data integrity. Understanding the significance of the public key in PKI is essential for establishing a robust and secure digital environment.
