Data security is crucial in today’s digital landscape due to the constant threat of cyberattacks and data breaches. It involves various measures, including encryption to protect data from unauthorized access, access controls like RBAC and user authentication, regular data backups, and disaster recovery plans. Advanced measures such as data masking and network security are also essential. Compliance with data regulations like GDPR and HIPAA is imperative to avoid penalties. Data security is vital in sectors like healthcare, finance, e-commerce, and government, where sensitive information is handled.
Understanding the Importance of Data Security:
1. Protection Against Cyber Threats
The digital landscape is fraught with cyber threats, from hackers and malware to phishing attacks. Without proper data security measures, you are vulnerable to these threats, risking data breaches and financial losses.
2. Compliance with Regulations
Many industries and jurisdictions have stringent data protection regulations in place. Failing to comply with these regulations can result in severe penalties. Proper data security ensures you stay on the right side of the law.
3. Preserving Reputation
A data breach can irreparably damage your reputation. Customers and clients trust you with their data; a breach can erode that trust. Secure data handling is essential to maintain a positive image.
Different Means of Securing Data:

Encryption:
What is Data Encryption?
Data encryption is the foundation of modern data security. It involves converting your data into a code that is unreadable to anyone without the decryption key. This process transforms your data into ciphertext, making it nearly impossible for unauthorized individuals to access it. The opposite of ciphertext is plaintext, which is the original, unencrypted data.
Types of Encryption
There are two primary types of encryption: public key and symmetric key. Public-key encryption uses a pair of keys: a public key for encryption and a private key for decryption. Symmetric key encryption, on the other hand, uses a single key for both encryption and decryption. While both methods are effective, they differ in nature and use cases.
Strength of Encryption
In terms of strength, third-party encryption software often surpasses built-in encryption programs. Third-party software is continuously updated to counter emerging threats, providing a higher level of security.
Port Blocking:
Physical Threats to Data Security
Physical intrusions can also jeopardize your information. An unauthorized USB device inserted into your system while you’re away can lead to data theft.
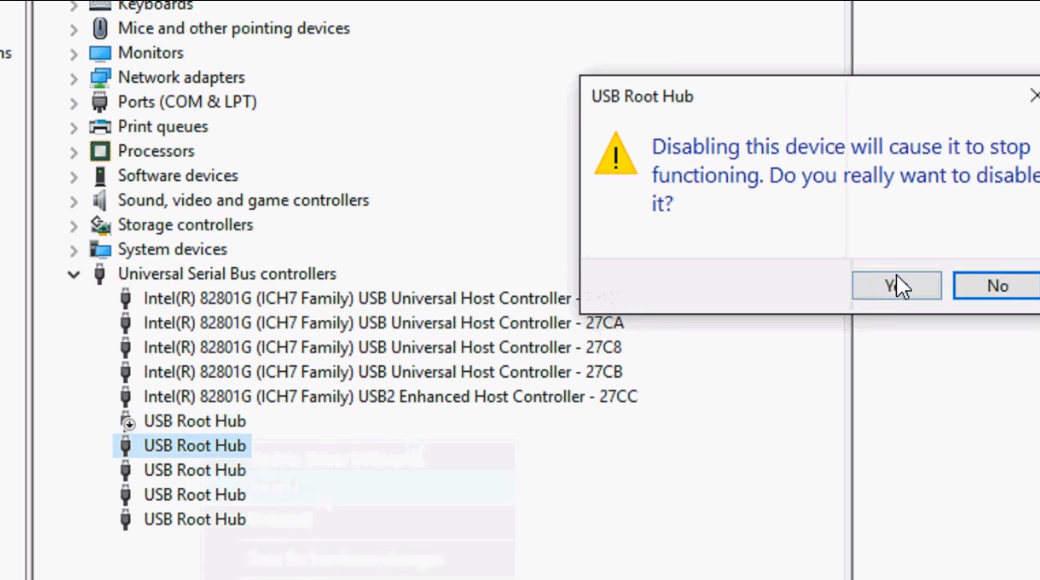
To counter this threat, USB port blocking is a valuable tool. It restricts access to any unauthorized USB drives that are not trusted. Whether you’re present or not, this feature ensures that your data remains safe from physical intruders.
USB Security:
The Relevance of USB Security
USB drives remain a reliable means of data storage. Many users still prefer them due to their reliability and distrust of cloud services, which rely on third parties to safeguard data.
To keep your data secure on USB drives, consider adding a password. This simple step can significantly enhance the security of your portable storage devices. Until the complete transition to cloud storage, it’s wise to take measures to protect your data where it resides.
Access Controls
Role-Based Access Control (RBAC)
RBAC is a method of limiting access to data based on an individual’s role within an organization. It ensures that only authorized personnel can access specific information.
User Authentication
Implementing strong user authentication methods, such as two-factor authentication (2FA) or biometrics, adds an extra layer of security. It verifies the identity of users before granting access.
Backup and Recovery
Creating regular backups of your data ensures that you can recover it in case of data loss due to cyberattacks or hardware failures. Cloud-based backups are becoming increasingly popular for their convenience and security.
Disaster Recovery Plans
Having a well-defined disaster recovery plan in place is crucial. It outlines the steps to be taken in case of a data breach or catastrophic event, minimizing downtime and data loss.
Advanced-Data Security Measures:
Data Masking
What is Data Masking?
Data masking involves replacing sensitive data with fictitious but realistic data. This allows organizations to use and share data for testing and analysis without exposing sensitive information.
Use Cases
Data masking is particularly valuable in industries like healthcare and finance, where data privacy regulations are stringent. It helps maintain data utility while protecting privacy.
Network Security
Firewall Protection
Firewalls act as a barrier between a trusted internal network and untrusted external networks. They filter incoming and outgoing traffic to prevent unauthorized access and cyber threats.
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS)
IDS and IPS are proactive security measures that monitor network traffic for suspicious activities and take action to block or mitigate threats.
Data Classification and Labeling
Importance of Data Classification
Classifying data based on its sensitivity allows organizations to prioritize security efforts. Not all data is equally valuable or vulnerable so resources can be allocated accordingly.
Labeling Data
Once data is classified, labeling it with appropriate security levels helps control access and use. This ensures that data is handled according to its importance.
The Role of Data Security in Different Sectors:
1. Healthcare
In the healthcare sector, patient data privacy is paramount. Stringent regulations like HIPAA (Health Insurance Portability and Accountability Act) govern the handling of patient data, necessitating robust data security measures.
2. Finance
Financial institutions handle vast amounts of sensitive financial data. Data breaches can lead to massive financial losses and erode trust. Banks and financial organizations invest heavily in data security.
3. E-commerce
E-commerce businesses store customer payment information and personal details. Implementing secure payment gateways and protecting customer data is vital for maintaining customer trust.
4. Government
Government agencies deal with sensitive and classified information. National security relies on the protection of this data, making government institutions a prime target for cyberattacks.
The Future of Data Security:
AI can be used to detect and respond to security threats in real time. Machine learning algorithms can identify patterns indicative of potential breaches, enhancing proactive security measures.
Blockchain offers a decentralized and tamper-proof ledger system. It has the potential to revolutionize data security by ensuring the integrity of data and transactions.
3. Zero Trust Architecture
Zero Trust is an evolving security model that doesn’t trust anyone or anything by default. It requires continuous authentication and authorization, making it harder for malicious actors to gain access.
Conclusion:
Data security is a necessity in our interconnected digital world. It plays a pivotal role in protecting against a myriad of cyber threats, ensuring compliance with stringent regulations, and preserving the trust and reputation of individuals and organizations alike. From the fundamental practice of data encryption to advanced measures like data masking and network security, the means to safeguard data continue to evolve. In various sectors, such as healthcare, finance, e-commerce, and government, data security is paramount, given the sensitive information each of these fields handles.
Frequently Asked Questions:
How does USB port blocking enhance data security?
USB port blocking restricts access to unauthorized USB drives, preventing physical intrusions and data theft, even when you’re not present.
What is data masking, and where is it valuable?
Data masking replaces sensitive data with realistic but fictitious information, ensuring privacy while enabling the use and sharing of data, particularly in industries like healthcare and finance.
What are firewalls, IDS, and IPS in network security?
Firewalls act as barriers to prevent unauthorized access, while Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) monitor and proactively block suspicious network activities.
How does data security vary across sectors like healthcare, finance, e-commerce, and government?
Each sector has unique data security needs. Healthcare focuses on patient data privacy, finance safeguards financial information, e-commerce secures customer data, and the government protects classified information for national security.
What are the future trends in data security?
The future of data security includes the use of artificial intelligence for real-time threat detection, blockchain technology for tamper-proof data integrity, and the adoption of Zero Trust Architecture, which continually verifies access to enhance security.
