Data on AWS is not automatically encrypted by default. While AWS provides various encryption options to secure data both at rest and in transit, the responsibility to enable and configure encryption lies with the user.
AWS (Amazon Web Services) is a cloud computing platform that offers a wide variety of services, with data storage and processing. As businesses and organizations increasingly rely on cloud solutions to store and manage their data, ensuring the security of sensitive info has become paramount. One important aspect of data security is encryption. I will discover the topic of data encryption on AWS, understanding its basics, how AWS manages encryption, different types of encryption, and the benefits it brings, and we will also address some common misconceptions surrounding AWS encryption.
Understanding AWS Data Encryption
The Basics of AWS Encryption
Encryption is the process of encoding information to become unreadable to unauthorized individuals. AWS provides several encryption options to protect your data stored on its platform. It is important to understand the basics of AWS encryption to ensure the security of your data.
When it comes to AWS encryption, one of the core principles is that it provides encryption at rest and in transit. This means that your data is protected both when it is stored in AWS data centers and when it is being transmitted over the network.
Encryption at rest means your data is encrypted while stored in AWS data centers. This confirms that even if someone gains unauthorized access to the physical storage devices, they won’t be able to read your data without the encryption keys. AWS uses industry-standard encryption algorithms to protect your data at rest.
On the other hand, encryption in transit refers to data encryption while it is being transmitted over the network. This is important to prevent unauthorized individuals from intercepting and reading your data as it travels between AWS services or between your applications and AWS services. AWS uses secure protocols such as Transport Layer Security (TLS) to encrypt data in transit.
AWS Encryption Services and Tools
AWS offers various encryption services and tools that enable you to secure your data effectively. These services include AWS Key Management Service (KMS) and AWS CloudHSM.
AWS Key Management Service (KMS) is a completely managed service that allows you to create, manage, and control encryption keys used to encrypt your data. With AWS KMS, you have full control over the lifecycle of your encryption keys, including key rotation and key deletion. It integrates seamlessly with other AWS services, allowing you to encrypt and decrypt data easily.
AWS CloudHSM, on the other hand, enables you to manage your hardware security modules (HSMs) in the AWS cloud. This service provides a dedicated, FIPS 140-2 Level 3 validated cryptographic infrastructure to secure your data. With AWS CloudHSM, you have complete control over your encryption keys and their cryptographic operations.
Using AWS encryption services and tools, you can ensure the confidentiality and integrity of your data stored on the AWS platform. These services and tools are designed to be easy to use and integrate seamlessly with other AWS services, making it convenient to implement strong encryption measures for your data.
How AWS Manages Data Encryption?
AWS takes data encryption seriously and employs various services to confirm the security and protection of your data. Two key components of AWS’s data encryption strategy are the AWS Key Management Service (KMS) and AWS CloudHSM.
AWS Key Management Service
AWS KMS is a vital component of AWS’s data encryption strategy. It allows you to generate and manage encryption keys, protecting your data at rest and in transit. With AWS KMS, you have full control over your encryption keys and can audit their usage, rotation, and management.
One key advantage of using AWS KMS is its integration with other AWS services. It simplifies encrypting and decrypting data seamlessly within your AWS environment. This integration ensures that your data remains secure throughout its lifecycle, from storage to transmission.
Additionally, AWS KMS is highly scalable, allowing you to handle large volumes of data and meet the demands of your applications. Whether you are a small startup or a large enterprise, AWS KMS can scale to meet your encryption needs.
AWS CloudHSM
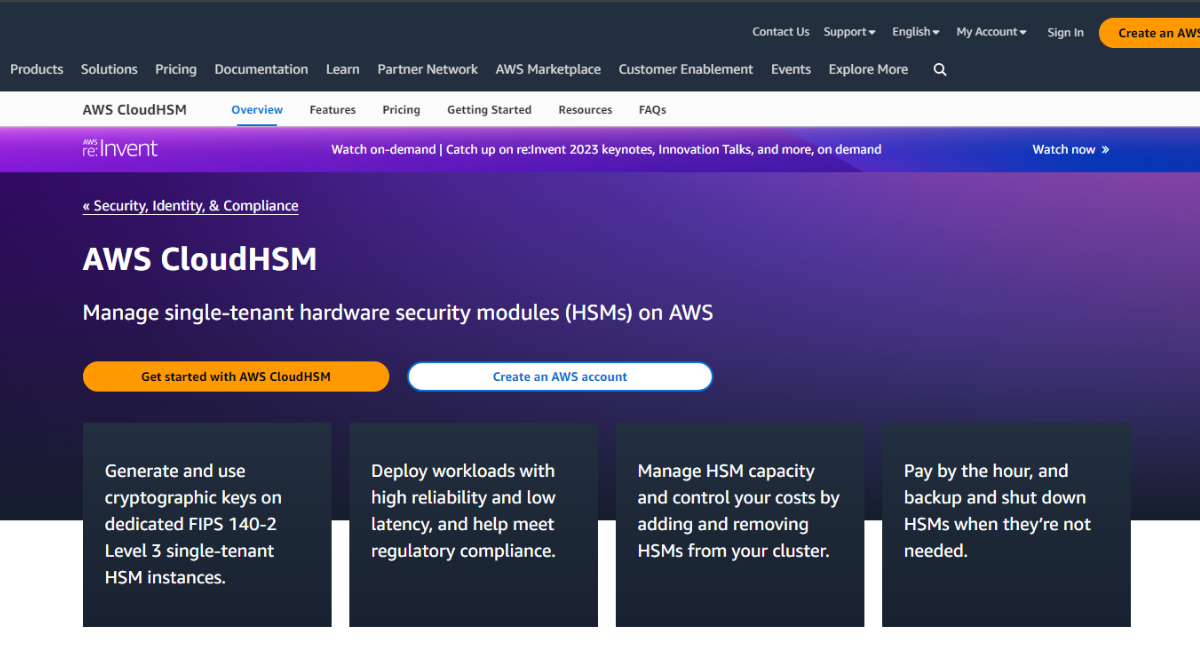
AWS CloudHSM allows you to manage your own Hardware Security Modules (HSMs) in the AWS cloud. These HSMs are hardware devices that securely generate and store encryption keys. By using AWS CloudHSM, you can ensure that your encryption keys are stored securely and not accessible to unauthorized parties.
AWS CloudHSM gives you complete control over your encryption keys and helps meet stringent compliance and regulatory requirements. It allows you to maintain ownership and control of your keys while leveraging the benefits of the AWS cloud.
Furthermore, AWS CloudHSM offers high throughput and low latency, making it suitable for high-performance encryption applications. Whether processing financial transactions or handling sensitive customer data, AWS CloudHSM can provide the performance and security you need.
In conclusion, AWS employs a comprehensive approach to data encryption with services like AWS KMS and AWS CloudHSM. These services ensure your data’s security and provide scalability, integration, and compliance capabilities. By leveraging these services, you can confidently protect your data in the AWS cloud.
Types of AWS Data Encryption
At-Rest Encryption
At-rest encryption refers to encrypting data when stored on disk or any other form of storage. AWS offers multiple options for at-rest encryption, depending on the specific service you use. For example, Amazon S3 (Simple Storage Service) provides server-side encryption, automatically encrypting your data upon storage.
Using AWS KMS, you can also manage your keys for at-rest encryption. This gives you complete control over the encryption process and allows you to meet any specific compliance or security requirements.
In-Transit Encryption
In-transit encryption is the process of encrypting data when transmitted over the network. AWS encrypts data in transit by default for many services, ensuring the confidentiality of your data during its transfer.
For example, Amazon S3 uses SSL/TLS (Secure Sockets Layer/Transport Layer Security) to encrypt data during transmission. In contrast, AWS Direct Connect uses IPSec VPN tunnels for secure data transfer between your on-premises environment and your AWS resources.
Benefits of AWS Data Encryption
When it comes to data security, AWS offers a range of benefits that go beyond the basic protection measures. By utilizing AWS data encryption, businesses can enhance their data security and ensure compliance with industry regulations.
Enhanced Data Security
One of the main aids of using AWS data encryption is its enhanced data security. Encrypting your data at rest and in transit adds an extra layer of protection against illegal entree. This becomes crucial when handling sensitive or confidential information, such as personal data or trade secrets.
With AWS encryption, your data is safeguarded from potential threats. Even if somebody gains access to your storage or intercepts your network traffic, they won’t be able to decipher the information without the encryption keys. This ensures your data remains secure and protected, giving you peace of mind.
Compliance with Regulations
Compliance with regulations is another significant benefit of AWS data encryption. Several industries, such as finance, healthcare, and government, have specific data security and privacy necessities. Failure to comply with these rules can effect in severe consequences, including legal penalties and damage to reputation.
By utilizing AWS encryption services, businesses can meet these compliance requirements effectively. AWS provides robust encryption mechanisms that align with industry standards, ensuring that your data is protected according to the specific regulations governing your industry. Additionally, AWS allows users to maintain control over their encryption keys, giving you the flexibility to manage your data security in a way that meets your organization’s unique needs.
Ensuring compliance with regulations helps you avoid legal issues and builds trust with your customers. By demonstrating your commitment to data security and privacy, you can attract and retain customers who value their information’s confidentiality.
In conclusion, AWS data encryption offers enhanced data security and compliance with industry regulations. By encrypting your data and maintaining control over your encryption keys, you can protect sensitive information and meet the specific requirements of your industry. Embracing AWS data encryption is a proactive step towards safeguarding your data and building trust with your stakeholders.
Common Misconceptions about AWS Encryption
Debunking AWS Encryption Myths
There are several misconceptions surrounding AWS encryption that need to be addressed. One common myth is that AWS automatically encrypts all your data by default. While AWS provides many encryption options, you must enable and configure encryption for your data. AWS offers the necessary tools and services to facilitate encryption, but the implementation is in the hands of the user.
Understanding the Limitations of AWS Encryption
Another misconception is that AWS encryption makes your data completely impervious to attacks. While encryption is crucial in protecting your data, it is just one piece of the security puzzle. To safeguard your data, it is important to consider other security measures, such as access controls, network security, and intrusion detection systems.
Key Takeaways
- AWS offers various encryption options to protect data at rest and in transit.
- AWS Key Management Service (KMS) and AWS CloudHSM are vital services to manage and control encryption keys.
- While AWS equips users with tools for encryption, it’s the user’s responsibility to enable and appropriately configure them.
- Encryption alone isn’t sufficient; a layered security approach, combining encryption with other measures, is necessary.
- Users should remain informed and aware of potential misconceptions regarding AWS encryption to ensure effective data security.
FAQs
Does AWS encrypt data by default?
While AWS offers encryption tools and services, users must enable and configure them as required.
What sets apart encryption at rest from encryption in transit in AWS?
Encryption at rest ensures data is encrypted while stored in AWS data centers. Encryption in transit protects data during its transfer over the network.
How does AWS Key Management Service (KMS) enhance data security?
AWS KMS allows users to create, manage, and control encryption keys, ensuring data confidentiality and allowing full control over the encryption process.
Is AWS CloudHSM different from AWS KMS?
AWS CloudHSM allows users to manage their Hardware Security Modules (HSMs) in the cloud, providing dedicated cryptographic infrastructure for data security.
Can AWS encryption guarantee complete data security against all threats?
While encryption enhances data security, it’s just one aspect. Users should employ a comprehensive security approach, including access controls and network security, to fully safeguard data.
Conclusion
In conclusion, ensuring the security of your data on AWS is essential, and encryption forms a critical part of a robust security strategy. You can effectively protect your data and comply with relevant regulations by understanding the basics of AWS encryption, how it is managed, the different types available, and the benefits it brings. It is important to address any misconceptions and realize that encryption alone cannot secure your data. By employing a layered approach to security, combining encryption with other security measures, you can mitigate risks and safeguard your data effectively on AWS.
