The importance of security in REST API
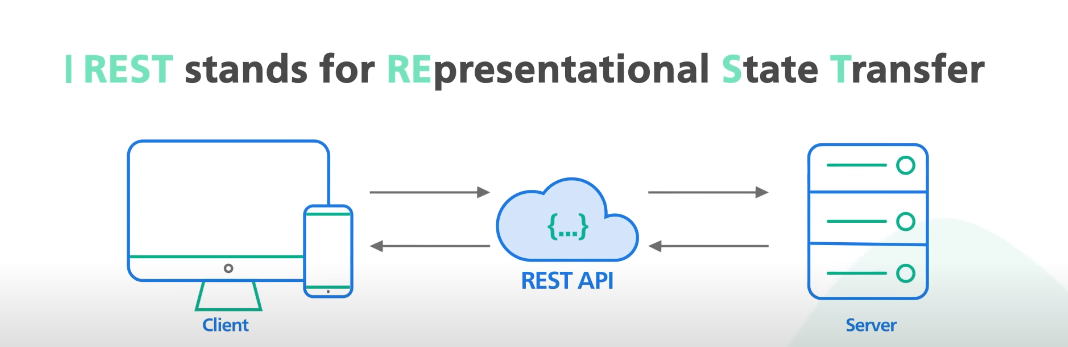
Security is a critical aspect of any REST API implementation. REST APIs are typically used to exchange data between different systems or applications, making them a prime target for attackers. Without proper security measures in place, sensitive data can be exposed, leading to data breaches, unauthorized access, and other security issues. There are several ways to ensure the security of a REST API. One of the most common methods is to use HTTPS (HTTP Secure) protocol, which encrypts data in transit between the client and server.
Best Practices for Secure Data Transfer in REST API
Here are some best practices for ensuring secure data transfer in REST API:
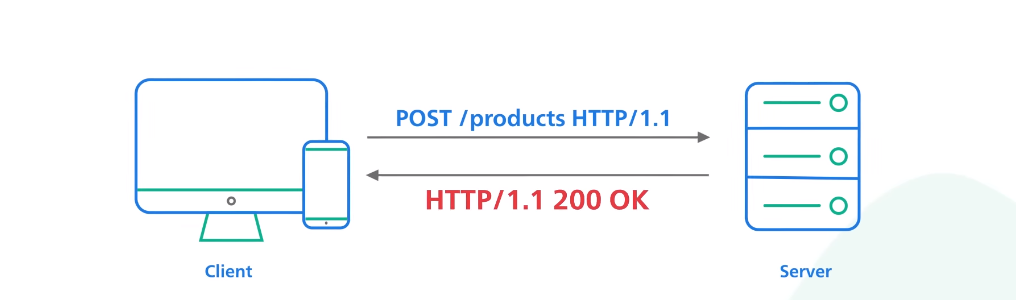
1. Use HTTPS: As mentioned before, HTTPS is the most common method for securing data transfer in REST API. It encrypts data in transit between the client and server, making it difficult for attackers to intercept and read the data.
2. Implement authentication and authorization: Implementing authentication and authorization mechanisms can help prevent unauthorized access to sensitive data. This can be achieved by using tokens, API keys, or other methods.
Implementing Encryption in REST API
Encrypting data in REST API can provide an additional layer of security to protect sensitive information. There are several ways to implement encryption in REST API, including using SSL/TLS encryption, encrypting data at rest, and using message-level encryption.SSL/TLS encryption can be implemented by using HTTPS to encrypt data in transit between the client and server. This ensures that data is protected from interception and tampering by attackers.
Key Management in REST API
Key management is an important aspect of securing REST API. It involves the management of cryptographic keys used for encryption and decryption of data. There are several key management techniques that can be used in REST API, including key rotation, key revocation, and key storage. Key rotation involves regularly changing cryptographic keys to prevent attackers from gaining access to sensitive information. This technique can be automated to ensure that keys are rotated at regular intervals.
Importance of Key Management In Encryption
Key management is crucial in encryption because it ensures the security and confidentiality of sensitive information. Without proper key management, encrypted data can be vulnerable to attacks, such as brute force attacks, where attackers try to guess the encryption key to gain access to the data. Key rotation, key revocation, and key storage are all essential techniques in key management that help prevent these types of attacks. By regularly rotating keys, any compromised keys become obsolete, making it more difficult for attackers to gain access to sensitive information.
Advantages of Encrypted Data Transfer
There are several advantages of encrypted data transfer, including:
1. Security: Encrypted data transfer ensures that the data being transmitted is secure and protected from unauthorized access.
2. Privacy: Encrypted data transfer helps to protect the privacy of the data being transmitted, ensuring that it is only accessible to authorized individuals.
3. Compliance: Many industries and organizations are required to comply with regulations and standards that mandate the use of encryption for data transfer. Using encryption helps to ensure compliance with these requirements.
Limitations of Encrypted Data Transfer
There are some limitations to encrypted data transfer that should be considered:
1. Performance: Encryption can add overhead to data transfer, which may impact performance, especially for large data sets.
2. Compatibility: Encryption methods may not be compatible with all systems or devices, which can limit the ability to transfer data securely between different platforms.
3. Key management: Encryption requires the use of keys to encrypt and decrypt data. Managing these keys can be challenging, especially for large organizations with many users and devices.
Common Encryption Attacks and Countermeasures
Encryption is a crucial tool for protecting sensitive data, but it is not foolproof. There are several common attacks that hackers use to try to break encryption:
1. Brute force attacks: This involves trying every possible key until the correct one is found. To counter this, encryption algorithms can use longer keys or limit the number of attempts.
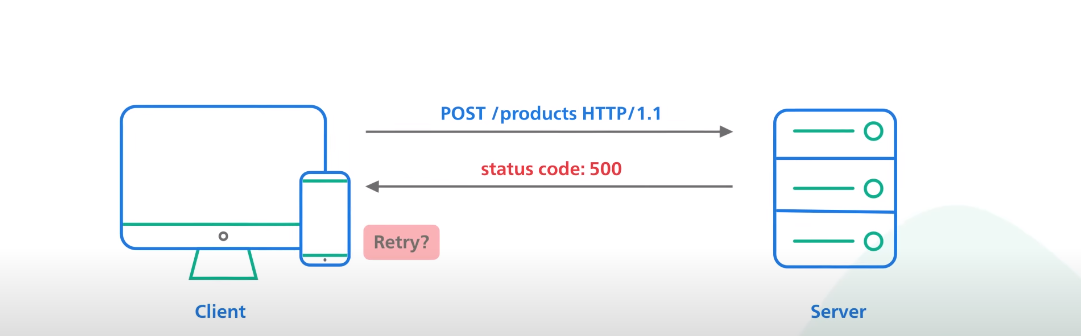
2. Man-in-the-middle attacks: This occurs when a hacker intercepts communications between two parties and can read or modify the data. To prevent this, encryption protocols can use authentication and digital signatures.
3. Side-channel attacks: This involves exploiting weaknesses in the hardware or software used to perform encryption. To prevent this, encryption algorithms can be designed to be resistant to such attacks.
Overall, while encryption is not perfect, it is still an essential tool for protecting data. By understanding the potential limitations and attacks, organizations can take steps to mitigate these risks and ensure their data remains secure.
Conclusion
In conclusion, encryption is a crucial tool for safeguarding sensitive data. While there are potential limitations and vulnerabilities to encryption, organizations can mitigate these risks by implementing strong encryption algorithms, using robust key management practices, and staying up-to-date with the latest security protocols. By doing so, they can ensure that their data remains protected from unauthorized access and theft. As a writing assistant, I can help you create clear and concise content to communicate the importance of encryption and its role in securing data.
Frequently Asked Questions
What is the best encryption method for REST API?
There is no one-size-fits-all answer to this question as the best encryption method for a REST API will depend on various factors such as the type of data being transmitted, the level of security required, and the compliance regulations that need to be followed. However, some commonly used encryption methods for REST APIs include AES (Advanced Encryption Standard), RSA (Rivest-Shamir-Adleman), and HMAC (Hash-based Message Authentication Code).
How do I generate encryption keys?
There are different ways to generate encryption keys depending on the encryption method being used. For example, if you are using AES encryption, you can generate a key using a random number generator or a key derivation function. If you are using RSA encryption, you can generate a key pair consisting of a public key and a private key using a key generation algorithm. It is important to ensure that the encryption keys are kept secure and not shared with unauthorized parties.
Can encrypted data be intercepted?
Encrypted data can be intercepted, but it cannot be read or understood without the decryption key. The purpose of encryption is to make the data unreadable to anyone who does not have the key to decrypt it. However, the interception of encrypted data can still be a security risk, as it could potentially be decrypted if the key falls into the wrong hands. It is important to use strong encryption methods and to keep the encryption keys secure to minimize the risk of interception and decryption.
What are the limitations of encrypted data transfer in REST API?
There are several limitations of encrypted data transfer in REST API:
1. Performance: Encryption and decryption of data can add processing overhead, which can slow down the transfer of data. This can be especially problematic in high-traffic environments.
2. Compatibility: Encryption methods used by the client and server must be compatible. If they are not, the data transfer may fail.
3. Key management: Encryption keys must be managed securely to prevent unauthorized access. This can be challenging, especially in distributed systems.
