Understanding Hard Drive Encryption

Hard drive encryption is a security measure that involves encoding data on a hard drive so that it cannot be accessed by unauthorized individuals. It is an effective way to protect sensitive information and prevent data breaches.
How Encryption Safeguards Data?
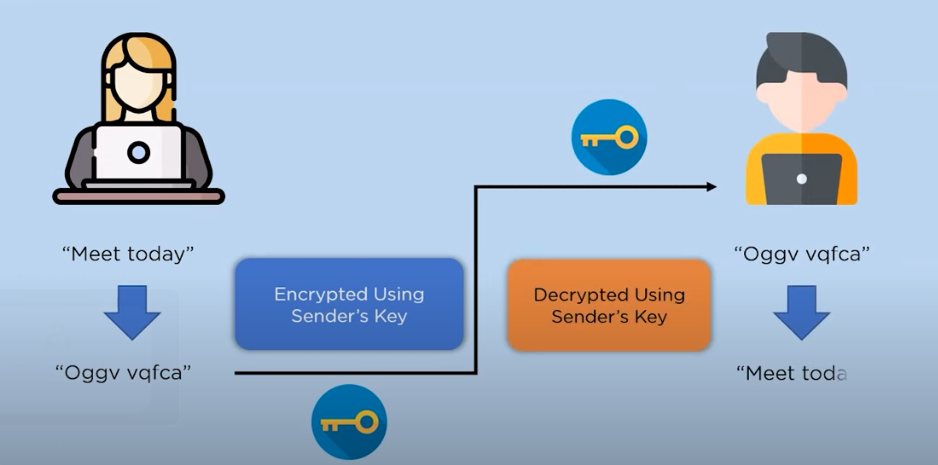
Encryption safeguards data by transforming it into a coded format that can only be accessed with the correct decryption key. This process makes the data unreadable and meaningless to unauthorized individuals, providing a strong level of protection against unauthorized access. When data is encrypted, it undergoes a complex mathematical algorithm that rearranges its structure. This algorithm uses a unique encryption key to convert the data into ciphertext, which appears as random characters or symbols. Without the correct decryption key, the ciphertext is virtually impossible to decipher.
Types of Hard Drive Encryption
There are several types of hard drive encryption methods available:
1. Full Disk Encryption (FDE): This type of encryption encrypts the entire hard drive, including the operating system, applications, and data. It provides a high level of security as all data on the drive is protected, even if it is moved or copied to another device.
2. File-based Encryption (FBE): With file-based encryption, only specific files or folders are encrypted rather than the entire hard drive.
Encrypt a Hard Drive After Data is Recorded
Yes, it is possible to encrypt a hard drive after data has been recorded. However, the process of encrypting a hard drive after data has been recorded typically involves creating a backup of the data, formatting the hard drive, and then encrypting the newly formatted drive. This process will result in the loss of all data previously stored on the drive, so it is important to ensure that you have a backup of your data before proceeding with the encryption process.
Preparation for Hard Drive Encryption
- Backing Up Data
- Assessing Hardware and Software Compatibility
- Understanding Encryption Algorithms
Step-by-Step Guide: Encrypting a Hard Drive After Data is Recorded
- A. Clearing Unnecessary Data
- B. Selecting an Encryption Tool
- C. Configuring Encryption Settings
- D. Initiating the Encryption Process
- E. Verifying the Encrypted Drive
Post-Encryption Considerations
- A. Managing Encrypted Hard Drive
- B. Accessing Encrypted Data
- C. Updating Encryption Protocols
Advantages of Post-recording Encryption
Advantages of Post-recording Encryption:
1. Data Security: Post-recording encryption ensures that your data remains secure even if it falls into the wrong hands. By encrypting the hard drive after data is recorded, you add an extra layer of protection to your sensitive information.
2. Flexibility: Encrypting the hard drive after data is recorded allows you to choose which data to encrypt. You can clear unnecessary data before initiating the encryption process, ensuring that only relevant and sensitive information is protected.
Limitations and Trade-offs
There are some limitations and trade-offs to consider when using post-recording encryption:
1. Performance Impact: Encrypting the hard drive after data is recorded can have a performance impact on your system. The encryption process requires additional computational resources, which can slow down data access and file transfers.
2. Time-consuming: Encrypting a large amount of data after it has been recorded can be a time-consuming process.
Best Practices for Hard Drive Encryption
- Regular Backups
- Strong Passwords and Key Management
- Keeping Software and Firmware Up to Date
Case Studies: Successful Encryption After Data Recording
Here are some best practices for hard drive encryption:
1. Regular Backups: It is important to regularly back up your data to ensure that you have a copy in case of any issues with the encrypted drive.
2. Strong Passwords and Key Management: Use strong, unique passwords and ensure proper key management practices to protect your encrypted drive from unauthorized access.
3. Keeping Software and Firmware Up to Date: Regularly update your encryption software and firmware to ensure that you have the latest security patches and features.
Frequently Asked Questions (FAQs)
Can I encrypt a hard drive without losing data?
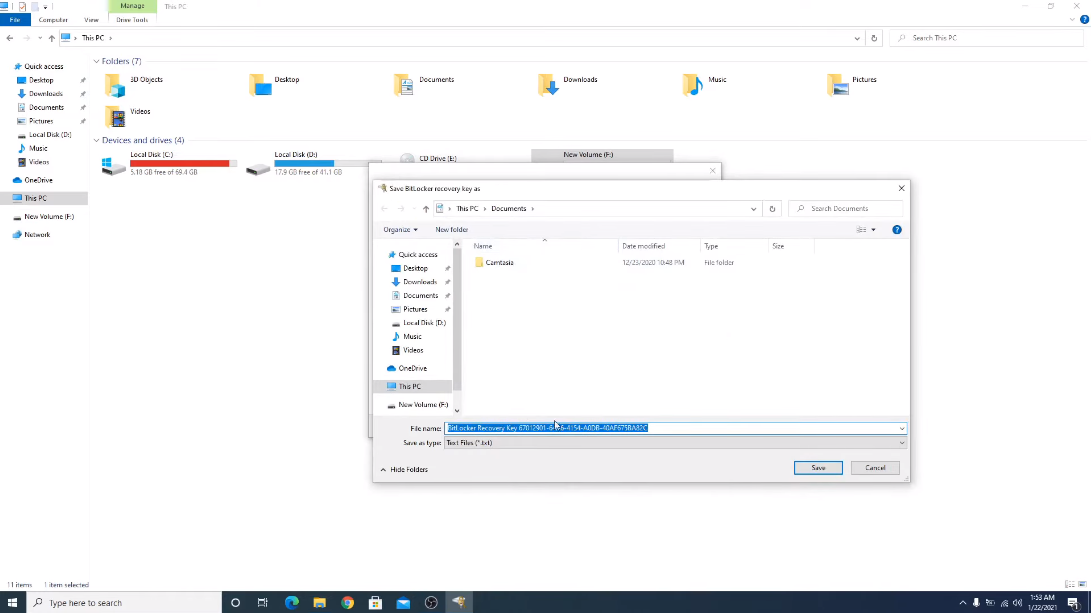
Yes, it is possible to encrypt a hard drive without losing data. Most encryption software allows you to encrypt the drive without formatting or erasing any existing data. However, it is always recommended to create a backup of your important data before initiating the encryption process, just in case any unforeseen issues occur.
What happens if I forget my encryption password?
If you forget your encryption password, it can be difficult to recover your data. Encryption is designed to be secure, so forgetting the password means you may not be able to access the encrypted data. In most cases, there is no way to recover the data without the password. It is important to keep your encryption password in a safe and secure place to avoid this situation.
Is it possible to decrypt an encrypted hard drive?
Yes, it is possible to decrypt an encrypted hard drive. However, decrypting an encrypted hard drive typically requires the encryption password or recovery key. Without these, decrypting the hard drive can be challenging or even impossible. It is important to keep your encryption password or recovery key in a safe and secure place to ensure that you can decrypt your hard drive if needed.
Can encryption slow down my computer’s performance?
Yes, encryption can potentially slow down a computer’s performance. When data is encrypted, it requires additional processing power and resources to perform the encryption and decryption processes. This can result in a slight decrease in performance, especially when dealing with large amounts of data or complex encryption algorithms. However, the impact on performance is typically minimal and may not be noticeable for most users. It is important to weigh the benefits of data security provided by encryption against any potential impact on performance.
Conclusion
In conclusion, implementing regular backups, strong passwords and key management, and keeping the software and firmware up to date are essential practices to ensure the security and integrity of your encrypted drive. These measures will help protect your data from unauthorized access and ensure that you have a backup in case of any issues.
