To bypass Android phone security using methods like Google account recovery, third-party software, and safe mode without losing data.
In today’s digital age, the security of our smartphones plays a crucial role in protecting our sensitive information. However, there may be instances where you find yourself struggling to access your device. Fear not, as I will lead you through bypassing your Android phone’s security lock without losing any precious data.
Understanding Android Phone Security Locks

Before we delve into the methods of bypassing Android phone security locks, it is essential to understand the importance of these security measures and the different types available.
Android devices have become an integral part of our lives, containing a wealth of personal information, from contacts and messages to photos and sensitive documents. With the growing reliance on smartphones, protecting this valuable data from unauthorized access is crucial.
The Importance of Android Security Locks
Android security locks, such as PIN codes, patterns, passwords, and biometric authentication, safeguard your personal information from unauthorized access. They act as the first line of defense, ensuring that only you can access your device.
Imagine the consequences of someone gaining unauthorized access to your smartphone. They could read your private messages, access your social media accounts, and even steal your identity. By setting up a security lock, you are taking proactive steps to protect your personal information and maintain your privacy.
Moreover, Android security locks also provide a sense of peace of mind. If your device gets lost or stolen, the security lock is a barrier, preventing anyone from accessing your data. This feature protects your personal information and helps deter theft, as the device becomes useless to unauthorized individuals.
Different Types of Android Security Locks
Android offers several types of security locks to suit individual preferences. PIN codes require a numeric code to unlock; patterns involve drawing a specific pattern on the screen; character-based passwords and biometric authentication methods, like fingerprint and facial recognition, offer a convenient yet secure way to access your device.
PIN codes are popular due to their simplicity and ease of use. They typically consist of four to six digits, allowing for quick unlocking while providing reasonable security. On the other hand, patterns offer a more visually engaging way to unlock your device. Connecting a series of dots in a specific order creates a unique pattern that only you know.
Passwords, being character-based, offer a higher level of complexity and security. They can include a combination of letters, numbers, and special characters, making them harder to guess or crack. Biometric authentication systems, such as fingerprint and facial recognition, have gained popularity recently due to their convenience. You can unlock your device effortlessly with a simple touch of your finger or a quick scan of your face.
It is worth noting that while biometric authentication methods offer convenience, they may not be foolproof. Sometimes, fingerprints or facial features can be replicated, leading to potential security vulnerabilities. Therefore, combining biometric authentication with other security measures, such as a PIN code or password, is advisable for added protection.
By understanding the importance of Android security locks and the different types available, you can decide which technique suits your needs best. Recall that the goal is to balance convenience and security, ensuring that your personal information remains safe and secure.
Precautions Before Bypassing Security Locks
Although bypassing security locks can be a solution to regain access to your Android phone, it comes with certain risks. It is crucial to take precautions beforehand to ensure a smooth process.
When faced with a locked Android phone, it can be frustrating and inconvenient. Whether you have forgotten your password, pattern, or PIN, bypassing security locks can provide a way to regain control of your device. However, it is important to approach this process cautiously and be aware of the potential risks involved.
Backing Up Your Data
Before attempting any bypass methods, it is wise to back up your data. This ensures you don’t lose any important files or settings during the process. Use cloud storage services or backup apps to save your data securely.
Backing up your data is not only important for the bypassing process but also for general data security. Regularly backing up your files, contacts, and other important information is always a good practice to prevent any loss or damage.
Risks Involved in Bypassing Security Locks
It is important to be aware that bypassing security locks can void your warranty and may have legal suggestions depending on your location. Manufacturers often discourage users from bypassing security locks as it can compromise the integrity of the device’s security measures.
When you bypass security locks, you are circumventing the built-in protection mechanisms put in place by the device manufacturer. This can expose your device to potential vulnerabilities and security risks. It is crucial to understand the potential significance before proceeding.
If not done correctly, you risk permanently locking yourself out of your device or losing your data. Bypassing security locks requires technical knowledge and expertise. One wrong step can lead to irreversible consequences. Therefore, following reliable and trusted guides or seeking professional assistance when attempting to bypass security locks is highly recommended.
Furthermore, it is essential to note that bypassing security locks should only be done on devices that you own or have legal permission to access. Unauthorized bypassing of security locks is considered unethical and may violate privacy laws.
Proceed with caution and at your own risk. Make sure to weigh the potential benefits against the dangers involved before bypassing security locks on your Android phone. It is always advisable to explore alternative methods or seek professional help if unsure about the process.
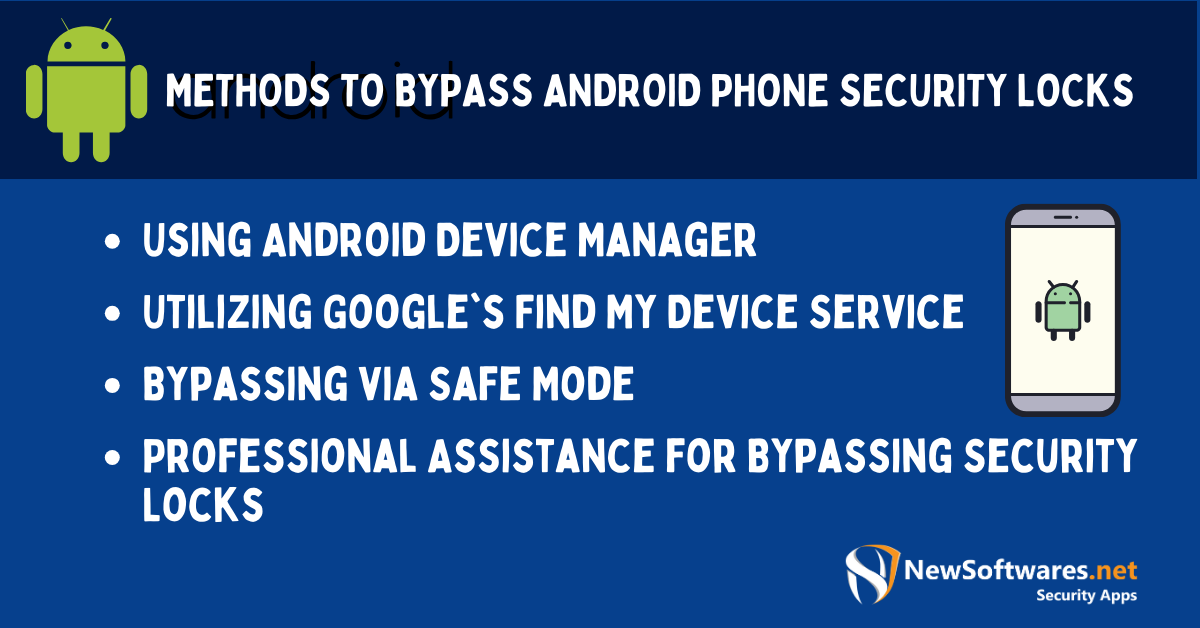
Methods to Bypass Android Phone Security Locks
Now that you recognize the importance of security locks and have taken the necessary precautions let’s explore different methods to bypass your Android phone’s security lock.
Using Android Device Manager
An effective way to bypass security locks is by utilizing Android Device Manager. This feature allows you to remotely lock, track, and erase data on your device. Accessing the manager on another device can reset your phone’s security lock and regain access.
Android Device Manager is an influential tool that helps you bypass security locks and provides peace of mind in case your phone gets lost or stolen. With this feature, you can track your device’s site, ensuring you have a higher chance of recovering it.
In addition to remotely locking your device, Android Device Manager allows you to erase all the data on your phone. This can be useful to protect your personal information from falling into the wrong hands.
Utilizing Google’s Find My Device Service
Like Android Device Manager, Google’s Find My Device service offers a convenient method to bypass security locks. You can locate your device, remotely lock it, and set a new security lock without losing data. This method requires your device to be connected to the internet.
Google’s Find My Device service is seamlessly integrated with your Google account, making it easily accessible from any device with internet access. This means that even if you don’t have another Android device, you can still use a computer or a friend’s phone to bypass your security lock.
In addition to bypassing security locks, Find My Device allows you to play a sound on your phone, even if it’s in silent mode. This can be incredibly helpful if you’ve misplaced your phone and need to locate it within your home or office.
Bypassing via Safe Mode
If the above methods do not work for your specific device, try booting your Android phone in safe mode. Safe mode temporarily turns off third-party apps, allowing you to remove or turn off any problematic app causing issues with your security lock. Once the problematic app is addressed, you can bypass your security lock.
Safe mode is a built-in feature in Android that allows you to troubleshoot issues by running your device with only the essential system apps. By entering safe mode, you can isolate the problem and determine if a third-party app is causing the security lock bypass issue.
In safe mode, you can uninstall or turn off any recently installed apps conflicting with your security lock. This can be particularly useful if you’ve recently downloaded an app you suspect is causing the lock bypass problem.
Once you’ve identified and resolved the issue, you can exit safe mode and regain the full functionality of your Android phone, including the security lock feature.
Professional Assistance for Bypassing Security Locks
In some cases, bypassing security locks may require professional assistance. It is important to understand when it is appropriate to seek help and how to choose a reliable tech service.
When to Seek Professional Help
If you cannot bypass your security lock using the methods as mentioned earlier or lack the technical knowledge to do so, it is advisable to seek assistance from a professional. They have the expertise to ensure a secure bypass without risking your data.
Choosing a Reliable Tech Service
When selecting a tech service for bypassing your security lock, do thorough research to find a reputable and trustworthy provider. Read reviews, seek recommendations, and inquire about their experience and success rate. This will help protect your privacy and safeguard a smooth bypass process.
Maintaining Your Android Phone Post-Bypass
After successfully bypassing your security lock, it is important to take additional steps to maintain the security of your Android phone.
Setting Up a New Security Lock
To ensure continued protection, set up a new security lock immediately after bypassing. Choose a strong and unique lock method to enhance the security of your device and prevent unauthorized access.
Regularly Updating Your Phone’s Security Settings
Stay vigilant by regularly updating your phone’s security settings. Android frequently releases security patches and updates to address vulnerabilities. Keeping your device up to date ensures you are protected against emerging threats.
Key Takeaways
- The “Forgot Pattern” feature can allow access using your Google account details.
- Some third-party tools can assist in unlocking without data loss.
- Booting in Safe Mode can temporarily turn off third-party lock screen apps.
- Always ensure to back up your data regularly.
- Avoid using these methods maliciously or on phones you don’t own.
FAQs
Q: Is it legal to bypass Android security?
A: Bypassing Android security on a device you don’t own or without permission is illegal.
Q: Can all Android phones be unlocked this way?
A: Different models and versions might have varying degrees of vulnerability.
Q: Is data compromised during this process?
A: If done correctly, the data remains intact.
Q: What if I can’t access my Google account for recovery?
A: You can try other methods or contact customer support for help.
Q: How can I prevent someone from bypassing my phone’s security?
A: Regularly update your software, use robust security features, and avoid third-party lock screen apps.
Conclusion
Following the methods and precautions mentioned above, you can bypass your Android phone’s security lock without losing any data. Remember to take necessary precautions, seek professional assistance if required, and prioritize the security of your device to safeguard your personal information.
