Encrypting your USB memory stick is crucial to provide robust protection against data loss and theft, a common risk due to these devices’ small size and portability. Encryption ensures that even if your USB memory is lost or stolen, sensitive information remains inaccessible without the correct password or decryption key. It safeguards confidential information from prying eyes, including personal documents, financial records, business contracts, and photos. Methods like BitLocker and VeraCrypt for Windows users and Folder Lock provide effective means to encrypt your USB memory and secure your valuable data, providing peace of mind in today’s digital age.
Why Encrypt Your USB Memory Stick?
1. Protection Against Data Loss and Theft:
- Due to their small size, USB memory sticks are prone to being misplaced or stolen. When unencrypted, any sensitive information stored on these devices is readily accessible to anyone who finds or steals them. Encryption is a shield, rendering the data inaccessible without the correct password or decryption key.
2. Safeguarding Confidential Information:
- In our digital age, we frequently carry confidential or sensitive information on USB drives. This could include personal documents, financial records, business contracts, or photos. Encrypting your USB memory ensures that the information remains confidential and protected from prying eyes, even if it’s lost or stolen.
3. Prevention of Unauthorized Access:
- Encryption is a powerful deterrent against unauthorized access. Even if someone gains physical access to your USB memory, they won’t be able to open or view the contents without the correct encryption key. This layer of security is invaluable in preventing data breaches.
4. Protection Against Malware and Viruses:
- USB drives can also be carriers of malware and viruses. When you encrypt your USB memory, you reduce the risk of malicious software infecting your data. The encrypted data remains inaccessible to the attacker even if malware is present.
Encrypt Folders On USB Memory:
Method 1: Encrypting with BitLocker (Windows)
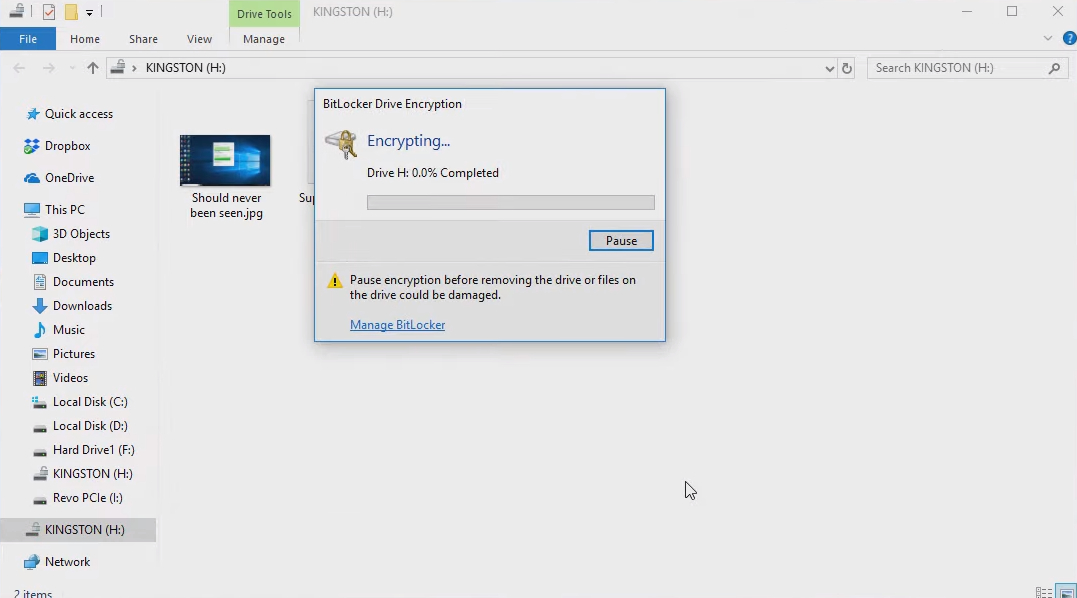
BitLocker is a built-in encryption tool in Windows, but it may not be available in all editions (e.g., Windows Home).
- Plug your USB memory device into your Windows computer.
- Search for “BitLocker” in the Windows search bar and select “Manage BitLocker” from the results.
- Find your USB memory device in the BitLocker window and click “Turn on BitLocker.”
- You’ll be asked how you want to unlock your drive. You can use a password, a smart card, or both. Select your preferred method and follow the on-screen instructions to set it up.
- After setting up your unlock method, you’ll be asked to choose how you want to back up your recovery key. It’s crucial to save this recovery key in a secure place because you’ll need it to access your data if you forget your password or lose your smart card.
- BitLocker will then ask if you want to encrypt the whole drive or just the used space. Choose the one that suits your needs.
- Click “Start encrypting” to begin the encryption process. This may take some time, depending on the size of your USB drive.
- Once the encryption is complete, your USB memory device is protected with BitLocker. You’ll need to enter your password or use your smart card to unlock it whenever you plug it into a computer.
Method 2: Encrypting with VeraCrypt (Cross-platform)
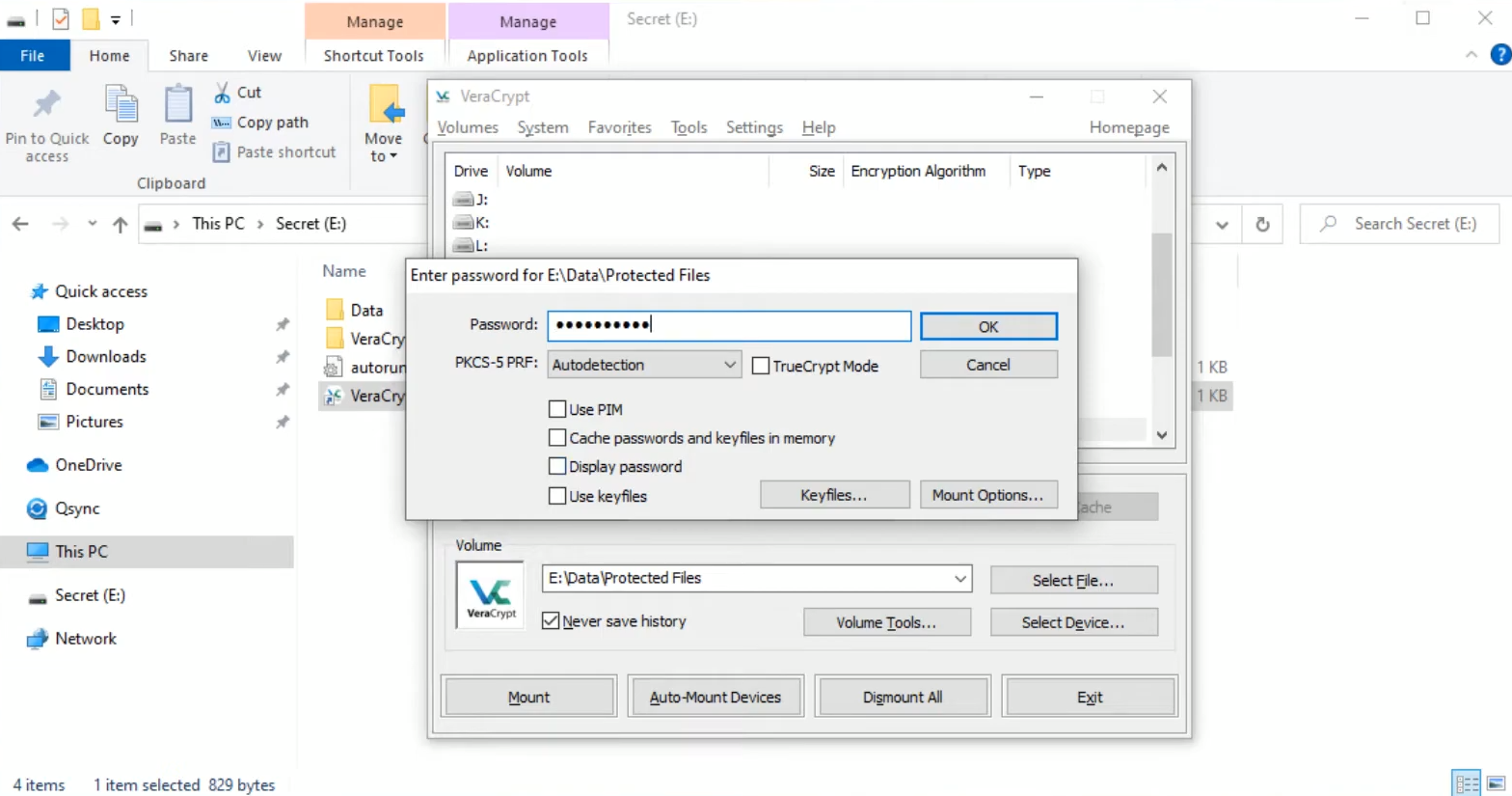
VeraCrypt is a free, open-source tool used on various operating systems, including Windows, macOS, and Linux. Here’s how to use it:
- Download and install VeraCrypt on your computer from the official website (https://www.veracrypt.fr).
- Insert your USB memory device into your computer.
- Open VeraCrypt, and in the VeraCrypt main window, click “Create Volume.”
- In the VeraCrypt Volume Creation Wizard, select “Create an encrypted file container.
- Choose “Standard VeraCrypt volume” and click “Next.”
- Browse to the location where you want to create the encrypted container file, select a name and click “Save.”
- Choose an encryption and hashing algorithm. For most users, the default options are sufficient. Click “Next.”
- Enter and verify a password for your encrypted container. Make it strong and memorable.
- Select the size of your encrypted container. This should be large enough to store the files and folders you want to encrypt.
- Choose whether to format the container as a FAT or NTFS file system. NTFS is recommended for larger files and folders.
- Move your mouse randomly within the VeraCrypt window to generate random data, which enhances encryption security.
- Click “Format” to create the encrypted container.
- Once the container is created, go back to the main VeraCrypt window and select a drive letter that will be associated with your encrypted container.
- Click the “Select File” button and browse to the container file you created earlier.
- Click “Mount,” and you’ll be prompted to enter your password.
- Once mounted, the encrypted container will appear as a new drive in your file explorer. You can copy your sensitive files and folders to this drive.
- To dismount the container, open VeraCrypt, select the drive letter, and click “Dismount.”
- Title: Secure Your Data: How to Encrypt Folders on a USB Memory Stick
Encrypting with Folder Lock?
Folder Lock is a user-friendly, lightweight program that you can easily download and install on your computer. Alternatively, you can utilize a portable installation-free version.
Step 1: Setup USB Key
- Download and install the Folder Lock on your computer.
- Launch the program and select “Setup USB Key.”
- Clicking this option will create a hidden and encrypted section on your USB memory.
Step 2: Password and Domain Creation
- The password and domain creation process may take up to 15 minutes. Once completed, a .exe file will be stored on your memory stick, granting you access to the encrypted portion. You can access this area from any computer without installing the program.
Step 3: Encrypt Your USB Drive
- Install and run the Folder Lock on your computer.
- The program’s main window will appear.
- Select “Encrypt USB drive” from this window.
- Insert your USB memory stick into the computer. The program will likely automatically detect your USB memory. However, if it doesn’t, click “Change” and manually select the USB memory you wish to encrypt or another hard disk space.
- Once you’ve chosen the USB memory, enter a password in the “Set password for diskette access” box and confirm it by entering the same password in the “Confirm Password” box.
- Click “Create disk.”
- In minutes, an encrypted space will be established on your USB memory.
- When the process is complete, a notification window will appear. Click “OK.”
Accessing Your Encrypted Files
Please note that as you’re using the free version of Folder Lock, you won’t be able to modify the files within the encrypted area, but you can view them.
- Insert your USB memory into a computer.
- Two .exe files will be present on the USB memory. The executable file allows access to the encrypted area, which is available only with the paid version of the program. However, this limitation shouldn’t be a significant concern for most users, as you can still view your files.
- You won’t be able to add files to the secure zone when using another computer. Only on your computer can you add new files to this encrypted domain.
- To add files to the safe area on your computer, open the program’s main window, click “Browse,” select the desired files from the window that opens, and copy them into the secure area.
Conclusion:
Encrypting your USB memory stick is essential in safeguarding your sensitive data from potential threats such as loss, theft, unauthorized access, and malware. While incredibly convenient, USB drives can become security risks when left unprotected. This comprehensive guide highlights that methods like BitLocker and VeraCrypt offer robust encryption options for various operating systems, ensuring your data remains shielded from prying eyes.
Additionally, Folder Lock provides an accessible and user-friendly solution for securing your USB memory. Creating an encrypted, password-protected area empowers you to protect your files effectively, even when accessing them from different computers.
