Internet Protocol Security (IPsec) is the protocol for encrypting user plane data. IPsec is employed widely to establish secure virtual private networks (VPNs), ensuring the transmitted user plane data’s confidentiality, integrity, and authenticity.
The protocol that is responsible for encrypting user plane data. User plane data plays a crucial role in network communication, and its encryption is essential for data security. We will also discuss the basics of data encryption, different encryption protocols, and the impact of encryption on user plane data.
Understanding User Plane Data
User plane data refers to the information exchanged between network devices during communication. It includes the transmitted content, such as emails, videos, or web pages. This data is essential for users to interact with various applications and services.
When talking about user plane data, we refer to the payload or the actual data packets sent and received over a network. It is separate from control plane data, which manages network operations. User plane data is critical as it carries the information users want to transmit and receive. It directly affects the user experience and the reliability of network communication.
Imagine you are browsing the internet, streaming your favorite TV show, or sending an important email. All these activities involve user plane data. It is the backbone of our digital world, facilitating the transmission of information across networks.
Let’s dive deeper into the role of user plane data in network communication. By understanding its importance, we can appreciate how it enables seamless communication between devices, allowing users to access and exchange information.
Definition and Importance of User Plane Data
User plane data encompasses the payload or the packets sent and received over a network. It is separate from control plane data, which manages network operations. User plane data is critical as it carries the information users want to transmit and receive. It directly affects the user experience and the reliability of network communication.
When we send an email, for example, the user plane data contains the actual content of the email, including the text, attachments, and any other media. Without user plane data, the email would not be transmitted or received. Similarly, when we watch a video, the user plane data carries the video file, allowing us to enjoy the visual content.
It is important to note that user plane data is not limited to personal communication. It also plays a crucial role in various industries and sectors. For instance, in the healthcare industry, user plane data enables the transmission of medical records, test results, and real-time patient monitoring. In the financial sector, user plane data facilitates secure online transactions and the exchange of sensitive financial information.
The Role of User Plane Data in Network Communication
User plane data enables seamless communication between devices, allowing users to access and exchange information. Whether browsing the web, sending emails, or streaming multimedia content, user plane data ensures these interactions are possible. It is the backbone of our digital world, facilitating the transmission of information across networks.
When we browse the internet, user plane data carries the web pages we visit, the images we see, and the videos we watch. It allows us to access vast information and connect with people worldwide. Without user-plane data, our online experiences would be limited, and the internet as we know it would not exist.
In addition to personal use, user plane data plays a crucial part in businesses and organizations. It enables employees to collaborate remotely, share files, and access company resources. User-plane data ensures businesses can operate efficiently and effectively in today’s interconnected world.
Moreover, user plane data is not limited to traditional devices such as computers and smartphones. With the rise of the Internet of Things (IoT), user plane data now includes communication between various smart devices, home appliances, wearables, and industrial sensors. This interconnectedness allows for automation, improved efficiency, and enhanced user experiences.
In conclusion, user plane data is the lifeblood of network communication. It carries the content we transmit and receive, enabling us to access information, connect with others, and utilize various applications and services. Its importance cannot be overstated, as it directly affects the user experience and the reliability of network communication. As technology evolves, user-plane data will play an increasingly significant role in shaping our digital world.
Overview of Data Encryption
Data encryption is a fundamental aspect of data security. It involves converting plain text data into an unreadable form, ciphertext, using encryption algorithms and keys. Encryption ensures that even if the data is intercepted, it remains secure and inaccessible to unauthorized parties.
Data encryption is not a new concept. It has been used for centuries to guard sensitive information from falling into the wrong hands. In ancient times, people would use various methods to encrypt their messages, such as substitution ciphers and transposition ciphers. Though rudimentary compared to modern encryption algorithms, these methods made the message unintelligible to anyone who did not possess the key to decrypt it.
Fast forward to the digital age, and data encryption has become even more critical. With the rise of the internet and the widespread use of electronic devices, the need to protect data from unauthorized access has never been greater. Encryption algorithms have evolved to keep up with technological advancements, providing stronger and more secure encryption methods.
The Basics of Data Encryption

Data encryption applies complex mathematical algorithms to transform the original data into ciphertext. Encryption algorithms utilize cryptographic keys to encrypt and decrypt the data. These keys are the cornerstone of data security, ensuring only authorized parties can access the encrypted information.
Encryption methods primarily fall into two categories: symmetric and asymmetric. A single key is employed for encoding and decoding in symmetric or private-key encryption. This necessitates both communicating parties to possess the identical key. Conversely, asymmetric encryption involves two keys: a public one for encoding and a private one for decoding, enabling safe communication even if the parties haven’t previously interacted.
Contemporary encryption techniques, like the Advanced Encryption Standard (AES) or the RSA method, are crafted to offer robust security and ward off breaches. They integrate intricate mathematical procedures that demand significant computational power, which renders decoding by unauthorized individuals exceptionally challenging without the appropriate key.
Why Encryption is Essential for Data Security
In our highly connected digital age, ensuring data security is critical. Encryption is key to defending vital data from unauthorized views and potential breaches, preserving personal records, securing monetary dealings, and shielding proprietary corporate communications. Data becomes exposed and susceptible to being hijacked, altered, or stolen without encryption.
Consider an instance where you’re transmitting your credit card details online for shopping. If encryption weren’t in place, this data would travel openly, presenting a golden opportunity for cybercriminals to capture and misuse your financial details. However, encryption converts your credit card data into an encoded format before its online journey, making it an extremely challenging task for malicious entities to interpret without the specific decryption key.
Moreover, encryption plays a significant role in maintaining individual privacy. In a time where data collection is omnipresent, encryption ensures personal data remains accessible only to permitted parties, thwarting any unauthorized snooping or privacy breaches.
Additionally, encryption isn’t just beneficial for enterprises managing confidential client information—it’s essential. It allows businesses to align with data protection guidelines and adhere to industrial benchmarks. Neglecting to establish stringent encryption standards can lead to dire outcomes, potentially including substantial fines and tarnishing the firm’s image.
In conclusion, data encryption is a vital component of data security. It protects sensitive information from unauthorized access and ensures the privacy and integrity of data. As technology advances, encryption algorithms will continue to evolve, providing stronger and more secure methods of protecting data.
Common Protocols for Data Encryption
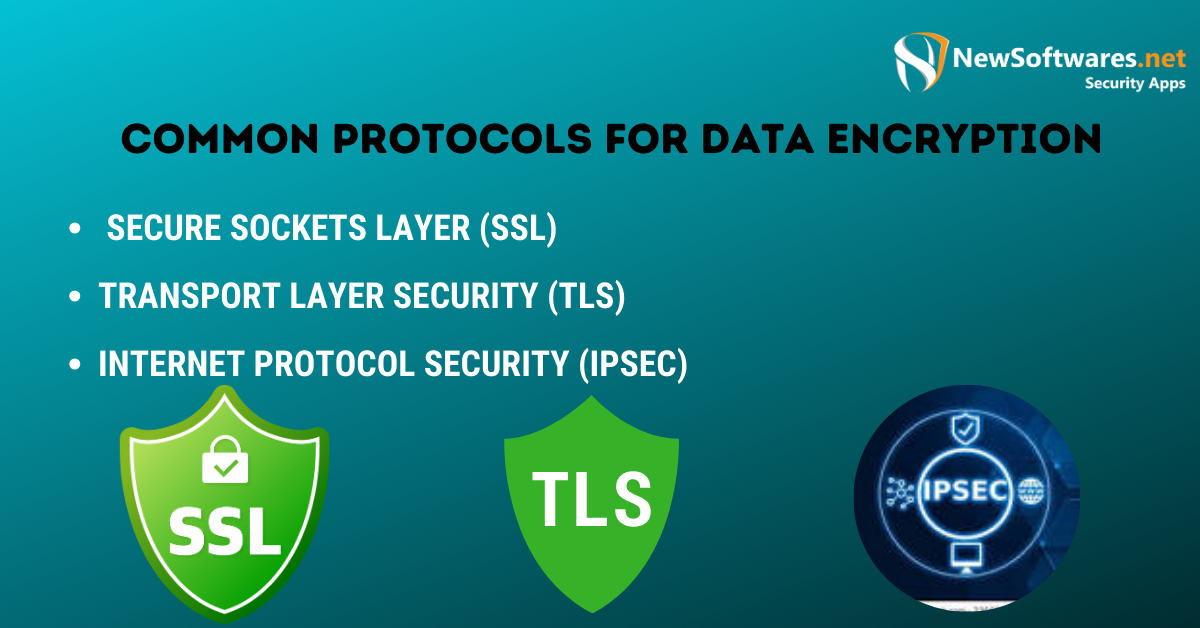
Various encryption protocols are used to secure user plane data. These protocols define the rules and procedures for encrypting and decrypting information. Let’s explore some of the commonly used encryption protocols.
Introduction to Data Encryption Protocols
Popular encryption protocols include Secure Sockets Layer (SSL), Transport Layer Security (TLS), and Internet Protocol Security (IPsec). These protocols provide a secure channel for data transmission, ensuring that the user plane data remains protected.
Comparing Different Encryption Protocols
Each encryption protocol has its strengths and weaknesses, and their suitability depends on the specific use case. Factors such as performance, compatibility, and level of security influence the selection of an encryption protocol. It is crucial to study these factors to ensure effective encryption of user plane data.
Protocol for Encrypting User Plane Data
One is responsible for encrypting user plane data among the various encryption protocols.
Identifying the Specific Protocol
The protocol responsible for encrypting user plane data is the Internet Protocol Security (IPsec). IPsec is widely used to establish secure virtual private networks (VPNs) and ensure the confidentiality, integrity, and authenticity of transmitted user plane data.
How This Protocol Works for User Plane Data
IPsec encrypts user plane data by encapsulating it within IP packets using the Encapsulating Security Payload (ESP) protocol. The encrypted data is transmitted over the network, safeguarding it from unauthorized access. The receiving device decrypts the data using the appropriate decryption keys, ensuring the original user plane data remains intact and secure.
The Impact of Encryption on User Plane Data
Encrypting user plane data has numerous benefits for both individuals and organizations. However, it can also present challenges that need to be addressed.
Benefits of Encrypting User Plane Data
Encrypting user plane data provides an additional layer of security, protecting sensitive information from eavesdropping and unauthorized access. It ensures the privacy and confidentiality of user communication. Encryption also helps maintain user plane data’s integrity by preventing tampering or alteration during transmission.
Potential Challenges and Solutions
Implementing encryption for user plane data may introduce performance overhead and compatibility issues. However, these challenges can be mitigated using efficient encryption algorithms, optimizing network infrastructure, and ensuring compatibility between devices and encryption protocols. The benefits of encryption far outweigh the challenges, making it a necessary measure for securing user-plane data.
Key Takeaways
- User plane data encompasses the content transmitted between devices on a network.
- Encryption is fundamental to safeguard user plane data, ensuring its confidentiality, integrity, and protection from unauthorized access.
- IPsec is the specific protocol responsible for encrypting user plane data.
- Alongside the benefits, encryption can present challenges like performance overhead and compatibility concerns, but these can be managed properly.
- Protecting user plane data is vital in today’s digital age, with encryption playing a central role in security.
FAQs
What is user plane data?
User plane data refers to the content transmitted during network communication, such as emails, videos, or web pages.
How does IPsec ensure user plane data encryption?
IPsec encrypts user plane data by encapsulating it within IP packets using the Encapsulating Security Payload (ESP) protocol, ensuring it’s protected from unauthorized access during transmission.
What distinguishes user plane data from control plane data?
User plane data carries the actual content or payload during communication, while control plane data manages network operations.
Why is data encryption vital for user plane data?
Encryption protects sensitive user plane data from unauthorized interception and potential breaches, ensuring privacy and data integrity.
Are there any challenges associated with encrypting user plane data?
While encryption provides security, it might introduce performance overhead and compatibility issues. However, these can be mitigated with efficient algorithms and optimized network infrastructure.
Conclusion
In conclusion, the Internet Protocol Security (IPsec) protocol encrypts user plane data, ensuring its confidentiality, integrity, and authenticity. Data encryption is essential for data security, safeguarding user communications from unauthorized access and potential data breaches. By implementing appropriate encryption protocols, organizations and individuals can protect sensitive information and maintain the privacy of user plane data.
