To use hashing securely for data matching, choose a strong cryptographic hash function, salt your hashes, avoid outdated hashing algorithms, and ensure no two different inputs produce the same hash output (avoiding collisions).
Data privacy and security are of utmost importance in today’s digital world. With the increasing amount of sensitive information being stored and transmitted online, it becomes crucial to ensure that data remains secure and protected from unauthorized access. One effective method widely used for data matching and security is hashing.
Understanding the Basics of Hashing
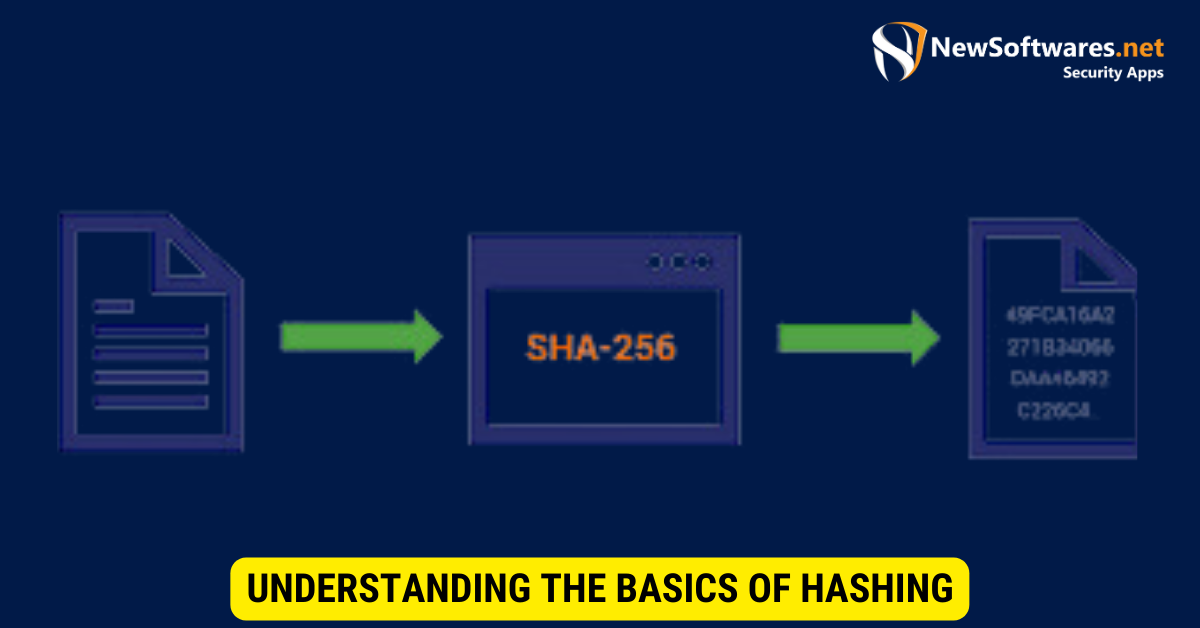
Before diving into the specifics of how to use hashing for data matching securely, it is important to understand it clearly. Hashing converts data, be it text or files, into a fixed-length string of characters. This string, known as the hash value, is generated using a mathematical algorithm.
The key characteristic of a hash function is that it is one-way. This means that once data is transformed into a hash value, it cannot be reversed back to its original form. Additionally, slightly altering the input data will result in a different hash value.
Hashing is an important concept in computer science and cryptography. It is widely used in various applications, such as password storage, data integrity verification, and matching. By understanding the basics of hashing, you can gain insights into how these applications work and how to use them effectively.
What is Hashing?
Hashing, in simple terms, is like a fingerprint for data. It is a unique representation of the input data that can be used for various purposes, such as matching or verifying data integrity. To better understand the concept, imagine a library where each book is assigned a unique identification number. Similarly, hashing assigns a unique identifier to each piece of data.
When data is hashed, it goes through a series of mathematical operations that transform it into a fixed-length string. This string is typically represented in hexadecimal format, consisting of numbers and letters. The consequential hash value is unique to the input data, meaning that even a small alteration in the input will produce a different hash value.
Hashing algorithms are planned to be fast and efficient, allowing for quick computation of hash values even for large amounts of data. Commonly used hashing algorithms include MD5, SHA-1, and SHA-256, each offering different security and hash length levels.
Importance of Hashing in Data Matching
Data matching is comparing two data sets to identify overlapping or duplicate records. By using hashing techniques, data matching becomes more efficient and accurate. Instead of comparing each data element individually, we can simply compare their hash values. This significantly reduces the computational complexity and improves the performance of data-matching algorithms.
In addition to improving efficiency, hashing enhances data security during the matching process. Instead of directly comparing sensitive data, such as passwords or personal information, we compare the hash values. This ensures that the original data remains protected and hidden from potential attackers.
Furthermore, hashing allows for the anonymization of data. By replacing sensitive information with hash values, organizations can share data for research or analysis purposes without compromising the privacy of individuals. This is particularly important in healthcare and finance, where privacy regulations and data protection are paramount.
It is worth noting that while hashing is a powerful tool for data matching, it is not without limitations. In rare cases, different inputs may produce the same hash value, leading to a collision. However, modern hashing algorithms are designed to minimize the probability of collisions, making them highly reliable for most applications.
In conclusion, hashing is a fundamental concept in computer science that plays a crucial role in data matching and security. We can efficiently compare and verify data without exposing sensitive information by converting data into unique hash values. Understanding the basics of hashing empowers individuals and organizations to leverage this powerful technique for various applications.
The Role of Security in Hashing
While hashing offers many advantages regarding data matching and performance, paying attention to the security aspects is crucial. Secure hashing is essential to prevent unauthorized access and maintain the confidentiality of sensitive information.
Why is Secure Hashing Necessary?
Insecure hashing algorithms can be vulnerable to various attacks, such as collision or rainbow table attacks. These attacks exploit weaknesses in the hashing algorithm to find two different inputs that result in the same hash value. This poses an important security risk, allowing attackers to impersonate legitimate users or gain access to sensitive information.
On the other hand, secure hashing algorithms are designed to mitigate these risks and make it computationally infeasible to find collisions or reverse engineer the original data from the hash value. By using secure hashing algorithms, we can ensure the integrity and confidentiality of the data during the matching process.
Potential Risks of Insecure Hashing
Using insecure hashing algorithms or not following security best practices can have severe consequences. Attackers can exploit vulnerabilities in the hash function to bypass security measures, gain unauthorized access, or tamper with the data being matched. This can lead to data breaches, identity theft, and other security incidents.
It is important to regularly update the hashing algorithms and follow industry standards to stay protected from emerging security threats. Additionally, implementing measures such as salted hashing or using multiple iterations of the hashing process can further enhance the security of the matching process.
Different Types of Hashing Algorithms
Various types of hashing algorithms are available, each with strengths and weaknesses. Choosing the right algorithm depends on the specific requirements of the data-matching process and the level of security needed.
Overview of Common Hashing Algorithms
The most commonly used hashing algorithms include MD5, SHA-1, and SHA-256. MD5 (Message-Digest Algorithm) is widely used but is considered relatively weak regarding security. SHA-1 (Secure Hash Algorithm 1) is stronger than MD5 but is being phased out due to vulnerabilities. SHA-256 is a more secure option and is currently recommended for most applications.
Choosing the Right Hashing Algorithm for Your Needs
When selecting a hashing algorithm, it is important to consider security, performance, and compatibility factors. Secure hashing algorithms, like SHA-256, offer better protection against attacks but may require more computational resources. On the other hand, less secure algorithms may provide faster performance but come with increased security risks.
It is advisable to consult security experts or follow industry best practices when choosing a hashing algorithm for your data-matching process. Moreover, staying up to date with the newest advancements and security recommendations is crucial to ensure the long-term security of your system.
Steps to Implement Secure Hashing
Implementing secure hashing for data matching involves a series of steps to guarantee the integrity and confidentiality of the process. Following a systematic approach helps minimize security risks and ensures the effectiveness of the matching algorithm.
Preparing Your Data for Hashing
Before the hashing process, it is important to ensure that the data is cleaned, standardized, and normalized. This helps improve the matching process’s accuracy and reduces potential errors or false positives. Data preparation may involve removing spaces and special characters or converting uppercase characters to lowercase.
Implementing the Hashing Process
The process involves applying the selected hashing algorithm to each data element individually. This generates a unique hash value for each data element. The hash values can then be stored in a hash table or database for subsequent matching processes.
It is crucial to handle errors or exceptions effectively during the hashing process. Proper error handling ensures that the algorithm runs smoothly and provides accurate results. Logging errors or exceptions for future analysis or troubleshooting is also important.
Verifying the Hashing Results
Once the hashing process is completed, verifying the integrity and quality of the hash values is vital. This can be done by comparing the hash values with a known reference or by independently verifying the hash values using checksums or digital signatures.
Verifying the hashing results helps identify any potential errors or inconsistencies and ensures the accuracy of the matching process. It also delivers an additional layer of security by validating the integrity of the data being matched.
Maintaining Hashing Security Over Time

Hashing security is not a one-time effort but an ongoing process. Regular maintenance and updates are crucial to ensure the data matching process’s long-term security.
Regularly Updating Your Hashing Algorithms
As security threats evolve, staying updated with the latest advancements in hashing algorithms is important. Regularly updating the hashing algorithms used for data matching helps mitigate any newly discovered vulnerabilities or weaknesses.
Keeping up with industry recommendations and best practices guarantees that your system remains secure and protected from emerging security risks. Consider establishing a process to monitor security bulletins and implement necessary updates promptly.
Monitoring for Potential Security Breaches
In addition to updating the hashing algorithms, monitoring the data-matching process for any potential security breaches is important. Implementing monitoring mechanisms, such as intrusion detection systems or log analysis tools, helps in identifying any abnormal activities or suspicious patterns.
Regularly reviewing logs and conducting security audits can help detect and mitigate any security incidents. Timely action can prevent potential data breaches and protect the confidentiality of the matched data.
Key Takeaways
- Salting hashes adds randomness, making it harder for attackers to use precomputed tables.
- Cryptographic hash functions, like SHA-256, offer robust security.
- Regularly update and review your hashing strategies.
- Never store raw (unhashed) sensitive data.
- Hash functions are one-way operations; the original data cannot be retrieved.
FAQs
What is salting?
Salting involves adding a random value (the salt) to the data before hashing, increasing security against attacks.
Why can’t we reverse a hash value to its original data?
Hashing is a one-way function, meaning it can’t be reversed to its original form once data is hashed.
How do we verify data with a hash?
By hashing the new data with the same function and comparing it to the stored hash.
Is MD5 secure for hashing?
No, MD5 is considered outdated and vulnerable. Modern applications should use stronger hashing algorithms.
Can two different inputs produce the same hash?
Ideally, no. However, when this rare event happens, it’s called a collision. Secure hash functions minimize the risk of collisions.
Conclusion
In conclusion, hashing is a powerful technique for securely matching data while maintaining privacy and integrity. By understanding the basics of hashing, considering security implications, choosing the right algorithms, implementing secure hashing steps, and maintaining security over time, you can ensure your data-matching process’s effectiveness and long-term security.
