No, encryption is not only for geeks. It’s a crucial part of our digital world, used by everyone to protect data, privacy, and security in everyday scenarios like online banking, messaging apps, and e-commerce. It also plays a vital role in businesses, governments, and safeguarding personal information. Encryption is a tool for anyone who values their privacy and security in the digital age.
Understanding Encryption:
Encryption is a systematic process of encoding information, making your data appear scrambled and unreadable to unauthorized users. This scrambled data, often called ciphertext, can only be transformed back into its original form by someone with the encryption key, which is like a digital password.
How Does Encryption Work?
To understand encryption better, let’s take a look at how it works:
- Data Transformation: When you encrypt data, it goes through a complex transformation process, turning it into an unreadable jumble of characters.
- The Encryption Key: You need a specific key to decode the encrypted data. Without this key, the data remains locked and indecipherable.
- Security Levels: Encryption comes in various levels of complexity and security. Some are easy to crack, while others are nearly impossible to break without the right key.
The Importance of Encryption:

Securing Your Online World
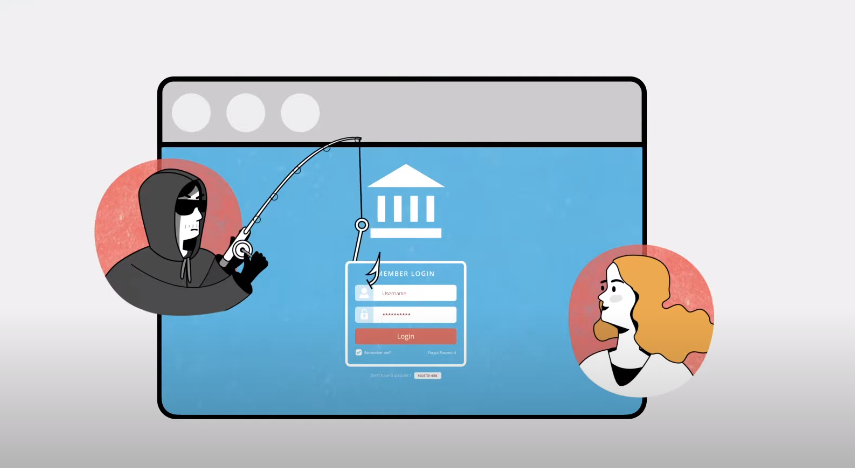
One of the most crucial aspects of encryption is its role in safeguarding your online activities. Whether you’re sending an email, making an online purchase, or simply chatting with friends on social media, encryption is at work in the background. It ensures that the information you share remains confidential and can’t be intercepted by hackers or cybercriminals.
Encryption is not limited to your online interactions; it also plays a pivotal role in protecting sensitive data stored on your devices. This includes your financial records, personal photos, and login credentials. Without encryption, all this information would be vulnerable to theft or unauthorized access.
Everyday Encryption:
You’re Probably Already Using Encryption
You likely use encryption daily without realizing it. For instance, popular messaging apps like WhatsApp boast their “end-to-end encryption” feature. This means that when you send a message, it’s wrapped in layers of security, making it indecipherable to everyone except the intended recipient.
End-to-end encryption is like a secret code between you and your friend. It ensures that only the sender and receiver can access the message, keeping it private and secure. This is just one example of how encryption seamlessly integrates into our daily routines.
Exploring Encryption Algorithms
In addition to end-to-end encryption, various encryption algorithms cater to different security needs. Common names in this realm include Triple DES, RSA, and Blowfish. These algorithms offer diverse levels of protection, allowing you to choose the one that best suits your requirements.
Data Protection Beyond Encryption:
Data Masking:
While encryption provides robust security, there’s another strategy in play – data masking. This technique involves creating a fake version of your data to mislead potential snoopers and hackers. It acts as a decoy, helping organizations identify the source of data breaches and fortify their defenses.
One-Way Security
Unlike encryption, data masking doesn’t allow the reverse transformation of data. Once data is masked, it can’t be reversed into its original form. This one-way protection ensures that even if hackers gain access to the masked data, they can’t decipher it, adding an extra layer of security.
Why Encryption Matters?

Encryption is not just about safeguarding your personal information; it’s also a cornerstone of privacy in the digital age. It ensures that your conversations, online activities, and sensitive data remain private free from surveillance or eavesdropping.
Foiling Cybercriminals
Cybercriminals are constantly on the prowl, looking for vulnerabilities to exploit. Encryption is a formidable barrier, making it exceedingly difficult for them to access your data. By using encryption, you become a less appealing target for cyberattacks.
Business Benefits
Encryption isn’t limited to individuals; it’s equally crucial for businesses. Companies use encryption to protect their trade secrets, customer data, and financial information. It’s a fundamental tool in maintaining the trust of clients and partners.
The Future of Encryption:
Quantum Cryptography:
The world of encryption is constantly evolving. One exciting development is quantum cryptography, which exploits the unique properties of quantum mechanics. This cutting-edge technology enables the achievement of cryptographic goals previously deemed impossible. For example, data stored in a quantum state can’t be stolen or copied without changing its state, making it exceptionally secure.
Homomorphic Encryption:
In the realm of cloud computing, homomorphic encryption plays a crucial role. It allows companies to perform operations on encrypted data without exposing the data to service providers. Companies can identify currency values, tax, and exchange rates without compromising data security. It’s not just limited to finance; homomorphic encryption has applications in protected voting systems, confidential data retrieval schemes, and collision-resistant hash functions.
Honey Encryption:
Another innovative approach is honey encryption. When incorrect credentials are entered, this technique generates useless data, fooling hackers into believing they’ve successfully infiltrated the system. Hackers receive data that appears genuine but is, in fact, a cleverly designed smokescreen. This discourages further hacking attempts, as hackers may think they’ve already achieved their goal.
Conclusion
Encryption is not an exclusive tool for tech geeks. It’s a vital component of digital life that everyone should embrace to protect their data in today’s interconnected world. While the current 256-bit encryption algorithms are robust, the future holds even more advanced techniques that will leave hackers and intruders with few opportunities to breach our data.
FAQs:
Is encryption difficult to set up?
Setting up encryption can vary in complexity depending on the application. Some messaging apps, like WhatsApp, have seamless end-to-end encryption, while encrypting an entire hard drive may require more technical knowledge. However, user-friendly tools and guides are available to make the process accessible to non-experts.
Can encrypted data ever be hacked?
While encryption is highly secure, no system is completely immune to hacking. Encryption’s strength lies in the encryption key’s complexity and algorithm. Regularly updating and strengthening your encryption methods can minimize the risk of breaches.
What’s the difference between encryption and data masking?
Encryption transforms data into a coded form that can be reversed with the correct key, while data masking replaces sensitive data with fake, irreversible information to mislead potential intruders.
Is quantum cryptography available to the public?
Quantum cryptography is still in the research and development stage. While it holds immense promise, it may be some time before it becomes widely accessible.
How can I learn more about encryption?
You can explore online tutorials, courses, and resources from cybersecurity organizations and reputable tech institutions to learn more about encryption. Additionally, consulting with cybersecurity experts can provide valuable insights into implementing encryption for your needs.
Can encryption slow down internet connections?
Encryption can introduce some overhead, which may slightly slow down internet connections. However, modern encryption methods are optimized for speed and security, and the impact on internet speed is usually minimal and not noticeable for regular browsing and communication.
Do I need to be tech-savvy to use encryption?
No, you don’t need to be a tech expert to use encryption daily. Many applications and services, such as messaging apps and online banking, automatically handle encryption for you. It’s as simple as using these services securely and being mindful of your digital security.
