Importance of Encryption in Protecting Data
Encryption is a crucial tool for protecting data because it ensures that only authorized parties can access and understand the information. By encoding the data using complex algorithms, encryption makes it unreadable to anyone without the proper decryption key. This helps to prevent unauthorized access, theft, and tampering of sensitive information, such as personal data, financial records, and confidential business information. Encryption is especially important for online transactions, where data is transmitted over networks vulnerable to interception or hacking.
Understanding Encryption
Encryption is a process of converting plain text or data into a coded form that is unreadable to anyone without the proper decryption key. The purpose of encryption is to protect sensitive information from unauthorized access, theft, or tampering. Encryption uses complex algorithms to scramble the data, making it difficult for hackers or other unauthorized users to access or read the information. Encryption is essential for online transactions, where data is transmitted over networks vulnerable to interception or hacking.
Discuss How Encryption Works?
Encryption works by using complex mathematical algorithms to scramble data so that it becomes unreadable to anyone who doesn’t have the decryption key. The encryption process involves taking the original data and applying a mathematical formula to it, which transforms the data into an unintelligible form. The resulting encrypted data can only be read by someone who has the decryption key, which is a unique code that reverses the encryption process.
Encryption is used in a variety of applications, including online banking, e-commerce, email, and messaging apps. By encrypting sensitive data, businesses and individuals can protect their information from unauthorized access, theft, and tampering.
PIA as a VPN Service
Private Internet Access (PIA) is a virtual private network (VPN) service that provides a secure and private Internet connection. PIA encrypts all internet traffic, making it unreadable to anyone who may try to intercept it. This means that your online activity, including your browsing history and personal information, is kept private and secure. PIA also offers features such as ad-blocking and malware protection, which further enhance your online security.
Explain How PIA Encrypts Data?
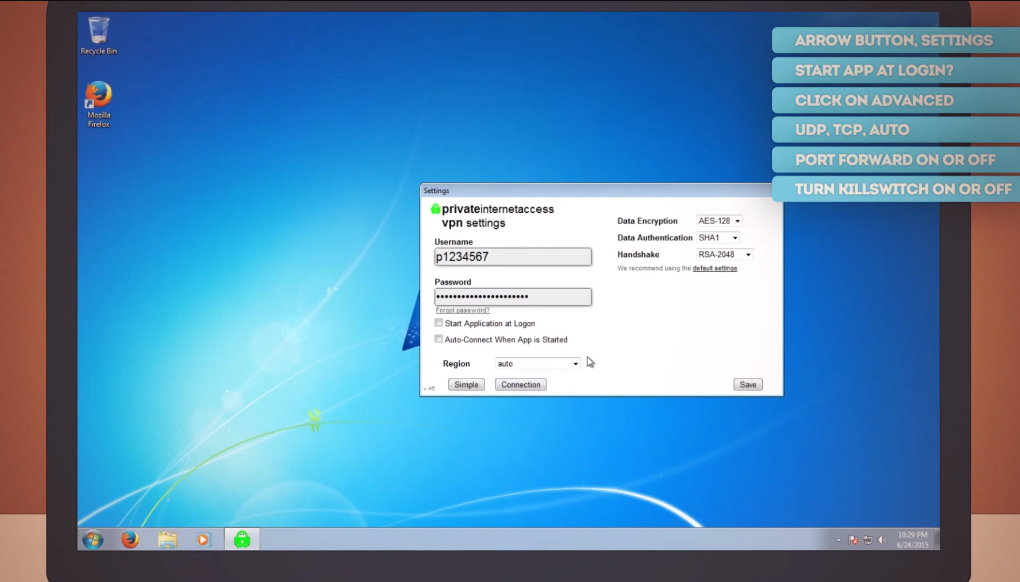
PIA uses advanced encryption protocols to secure your internet traffic. When you connect to the PIA VPN, your device establishes a secure connection with PIA’s servers. All data sent between your device and the server is encrypted using strong encryption algorithms. This means that any data intercepted by third parties will be unreadable and useless to them. PIA uses OpenVPN, IPSec/L2TP, and PPTP protocols to encrypt data, depending on the device and operating system being used.
Encryption Protocols Used by PIA
PIA uses several encryption protocols to secure data between the user’s device and the VPN server. The most commonly used protocols are OpenVPN, IPSec/L2TP, and PPTP.OpenVPN is an open-source protocol that uses SSL/TLS encryption to secure data. It is considered to be one of the most secure protocols available and is widely used by VPN providers. OpenVPN can be configured to use various encryption algorithms, including AES and Blowfish.
Effectiveness of PIA’s Encryption
Based on the information provided, PIA appears to be using strong encryption protocols to secure data between the user’s device and the VPN server. OpenVPN, which is one of the most commonly used protocols, is known for its strong SSL/TLS encryption and can be configured to use various encryption algorithms, including AES and Blowfish. The use of IPSec/L2TP and PPTP protocols also adds an extra layer of security to the data transmission process.
Benefits of Using PIA for Encryption
Using PIA for encryption provides several benefits, including:
1. Enhanced Security: PIA uses strong encryption protocols to secure data transmission, which ensures that the user’s data is protected from prying eyes.
2. Privacy Protection: PIA’s encryption protocols ensure that the user’s online activities are kept private and cannot be monitored by third parties.
3. Access to Restricted Content: PIA’s encryption protocols allow users to access restricted content by bypassing geo-restrictions and censorship.
Comparison with Other VPN Services
When compared to other VPN services, PIA stands out in terms of its strong encryption protocols, which provide enhanced security and privacy protection. Additionally, PIA’s ability to bypass geo-restrictions and censorship makes it a popular choice for users who want to access restricted content. However, some users may find that other VPN services offer a wider range of server locations or more advanced features. Ultimately, the best VPN service for an individual user will depend on their specific needs and preferences.
Factors that Affect Encryption
Several factors can affect the strength of encryption in a VPN service. These include the type of encryption protocol used, the key length, and the strength of the encryption algorithm. Additionally, the level of encryption can be affected by the processing power of the device being used, as well as the speed of the internet connection. Users need to choose a VPN service that uses strong encryption protocols and key lengths, as well as regularly updating their encryption algorithms to stay ahead of potential security threats.
How to Test PIA’s Encryption?
To test the encryption of Private Internet Access (PIA), you can use various online tools such as Wireshark or Packet Sniffer to monitor your Internet traffic. You can also use a VPN testing tool like ipleak.net or dnsleaktest.com to check if your IP address and DNS requests are being leaked. To ensure that PIA’s encryption is working properly, you can also check the settings of your VPN client to verify that it is using the recommended encryption protocol and key length.
Misconceptions About PIA and Encryption
One common misconception is that PIA’s encryption is not strong enough to protect your online activities. However, PIA uses industry-standard encryption protocols such as OpenVPN, L2TP/IPSec, and PPTP, which are considered to be highly secure. Another misconception is that PIA logs your online activities.
Pertinent FAQs
Is PIA Encryption Strong Enough to Protect My Data?
Yes, PIA offers strong encryption protocols to protect your online activities. It uses AES-256 encryption, which is considered to be one of the most secure encryption standards available. Additionally, PIA also offers other security features such as a kill switch and DNS leak protection to further enhance your online security.
How Does PIA Encrypt Data?
PIA uses AES-256 encryption to encrypt your data. This encryption standard is considered to be one of the most secure encryption protocols available. PIA also uses other security features such as a kill switch and DNS leak protection to further enhance your online security. These features ensure that your online activities remain private and secure.
What Encryption Protocols Does PIA Use?
PIA uses the AES-256 encryption protocol, which is considered to be one of the most secure encryption protocols available. Additionally, PIA also supports other encryption protocols such as OpenVPN, L2TP/IPSec, and PPTP. These protocols provide users with a range of options to choose from based on their specific security needs.
What Are The Limitations of PIA’s Encryption?
The AES-256 encryption protocol is considered to be extremely secure and is widely used by many organizations and government agencies. However, it is important to note that no encryption protocol is completely foolproof and can be vulnerable to attacks if not implemented properly or if there are weaknesses in the underlying system.
Conclusion
In conclusion, Private Internet Access (PIA) is a reliable VPN service that offers strong encryption protocols to protect your online activities. It is important to ensure that your VPN client is using the recommended encryption protocol and key length for maximum security. Despite common misconceptions, PIA does not log your online activities.
