Introduction
Data encryption is a technique to protect sensitive data from unauthorized access by converting it into an unreadable format. Encryption algorithms use complex mathematical formulas to scramble the original message or data, making it virtually impossible for hackers or cybercriminals to decipher the content. The encrypted data can only be accessed and understood by authorized individuals with decryption keys or passphrases.
The Data Encryption Standard (DES) was one of the first encryption standards developed in the 1970s by IBM. It was widely used for secure communication until its weaknesses were discovered, and it was eventually replaced by a more robust standard called Advanced Encryption Standard (AES). AES is currently considered the gold standard for encryption and is widely used by governments, financial institutions, and businesses.
The DES is based on a Feistel network structure, which involves dividing plaintext into fixed-size blocks, typically 64 bits. The algorithm performs sixteen rounds of encryption on each block using a different subkey for each round. These subkeys are derived from an initial key shared between the sender and receiver. The plaintext is mixed with these subkeys during encryption through mathematical operations such as substitution and permutation to produce ciphertext.
Understanding The Data Encryption Standard (DES)
Description Of DES And Its Characteristics
DES encrypts and decrypts data using a secret key, which must be kept confidential to ensure secure communication. One of the main characteristics of DES is its 64-bit block size, meaning that it can only encrypt or decrypt messages up to 64 bits at once. This limitation led to security concerns in the late 1990s, prompting NIST to develop the Advanced Encryption Standard (AES) with larger block sizes for more secure encryption. Another characteristic of DES is its use of Feistel network structure, which involves dividing each block into two halves and processing them through multiple rounds of substitution-permutation operations before recombining them into a final encrypted or decrypted message.
Comparison Between DES And Other Encryption Standards
The Advanced Encryption Standard (AES) has replaced DES as the standard encryption algorithm due to its higher level of security and faster processing speed.
One advantage of AES over DES is its key size. While DES uses a 56-bit key, AES can use a 128-, 192-, or 256-bit key, making it much more difficult to crack using brute-force attacks. Another advantage is that AES uses a different number of rounds depending on the length of the key, making it more adaptable to different levels of security requirements.
Other encryption standards, such as Blowfish and Twofish, have also emerged as alternatives to DES. These algorithms use larger block sizes than DES and offer similar levels of security as AES. However, they are not as widely adopted or standardized as AES, which remains the go-to encryption standard for most commercial applications today.
Block Cypher Operation And Its Role In DES
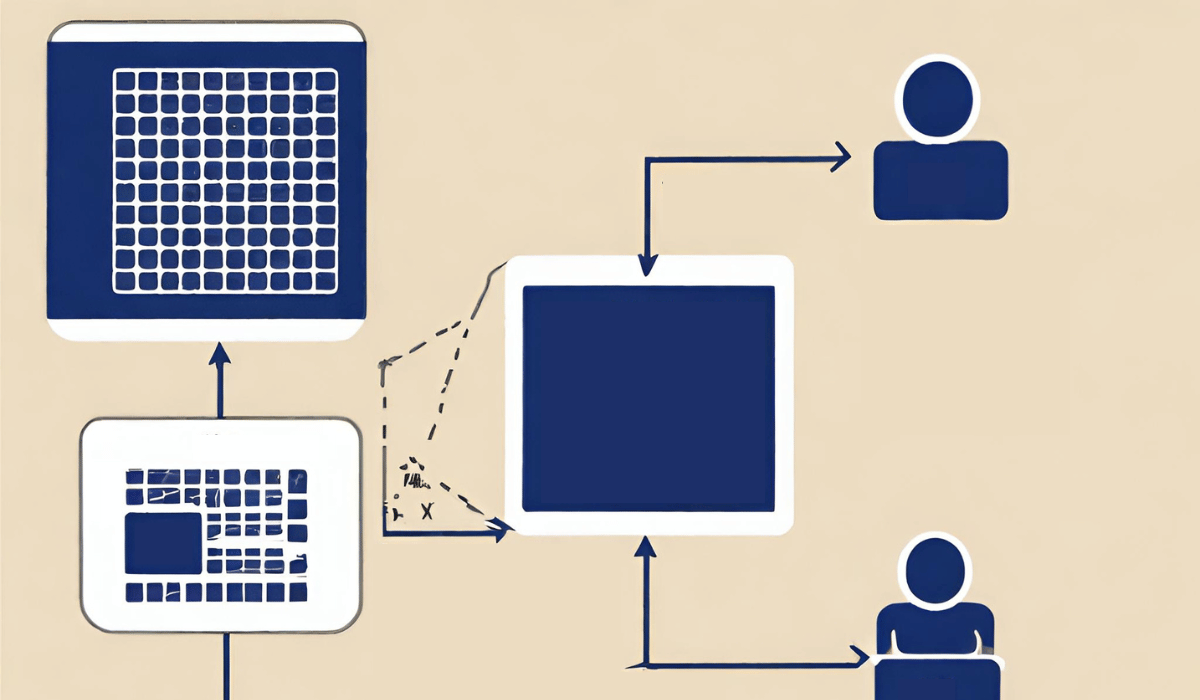
The block cypher algorithm divides the plaintext message into fixed-sized blocks and encrypts each block individually. The standard block size for DES is 64 bits, meaning any message longer than this length must be divided into multiple blocks.
In DES, a block cypher operation involves two main steps: encryption and decryption. During encryption, the plaintext message undergoes several rounds of substitution-permutation operations using a secret key to produce a ciphertext output. Conversely, the same process is reversed during decryption to recover the original plaintext message.
The role of block cypher operation in DES is critical because it provides robust security against brute force attacks by making it computationally expensive for attackers to decipher the encrypted data without knowing the secret key used in encryption.
Modes Of Operation Used With DES
The modes of operation used with DES include Electronic Codebook (ECB), Cipher Block Chaining (CBC), Cipher Feedback (CFB), Output Feedback (OFB), and Counter Mode (CTR). The ECB mode involves dividing the plaintext into blocks and encrypting each block independently using a secret key. The disadvantage of this mode is that it does not conceal patterns in plaintext.
The Components Of DES
The DES comprises several components that work together to encrypt and decrypt data.
The first component of DES is the key, which is an arbitrary sequence of 64 bits used to encrypt and decrypt data.
The second component is the initial permutation (IP), which rearranges the input data into a specific order before it enters the core algorithm. The core algorithm consists of sixteen rounds, each performing different operations on the input data.
During each round, two primary functions are applied: expansion permutation and substitution boxes (S-boxes). Expansion permutation involves expanding 32-bit blocks into 48-bit blocks by duplicating some bits while discarding others. S-boxes perform nonlinear substitutions on these expanded blocks using pre-defined tables that replace each block with another according to its content.
After sixteen rounds, a final permutation known as inverse initial permutation (IP-1) takes place to output encrypted ciphertext. Understanding each component’s role in DES can help users better understand its workings and appreciate its robust security features.
Illustration Of The DES Algorithm Using Examples
Let’s consider an example where we want to encrypt the message “HELLO” using DES.
The message is converted into binary form and divided into 64-bit blocks. The initial permutation (IP) is applied to each 64-bit block of plaintext, followed by sixteen rounds of substitutions and permutations known as Feistel rounds. At each round, a unique subkey derived from the main key using a Key Schedule is XORed with half of the input bit string before passing through substitution boxes (S-boxes) and Permutation tables (P-boxes).
Inverse Initial Permutation (IIP) is applied at the final round to yield the ciphertext. Once encrypted, only someone possessing the secret key and decryption algorithm can decipher this message back into plain text. This example illustrates how DES encryption works by breaking down its complex mechanism into simpler, visually understandable steps.
Strengths And Weaknesses Of DES
Discussion Of The Strengths Of DES
One of the key strengths of DES is its widespread adoption in many industries, including finance, healthcare, and government agencies. This makes it a trusted standard for secure data transmission and storage. Additionally, DES has undergone rigorous testing to ensure its security against various attacks.
Another of the Data Encryption Standard (DES) is its simplicity. DES is a relatively straightforward encryption algorithm that can be easily implemented on various hardware and software platforms. This makes it an attractive option for organizations looking to secure their data without investing in complex and expensive encryption solutions.
DES has a long history of being widely used and trusted by government agencies, financial institutions, and other organizations worldwide. Its reliability and security have been tested over many years, making it one of the most enduring encryption standards still in use today.
Limitations And Vulnerabilities Of DES
Key Length
With a 56-bit key length, DES is vulnerable to brute-force attacks that can break the encryption using modern computing power in less than a day. This has led to the development of stronger encryption algorithms such as Advanced Encryption Standard (AES), which uses longer key lengths and more robust security features.
Susceptibility To Block Cypher Attacks:
Due to its fixed block size, attackers can use known plaintext or ciphertext pairs to gain insight into the encryption algorithm and potentially break it. Additionally, DES is vulnerable to differential cryptanalysis, a technique attackers use to analyze the difference between pairs of plaintexts and their corresponding ciphertexts.
The Need For An Improved Encryption Standard
DES has a key length of only 56 bits which can be easily cracked by modern computing power. Additionally, there have been concerns about the security of DES due to its age and vulnerabilities discovered over time.
Furthermore, with advancements in technology and the increasing amount of sensitive data being stored online or transmitted electronically, an encryption standard needs to provide high-level security and be scalable and adaptable to changing threats. The need for improved encryption standards is especially critical in fields such as healthcare, finance, and government, where data privacy is paramount.
DES Variants And Implementations
Overview Of Triple DES (3DES)
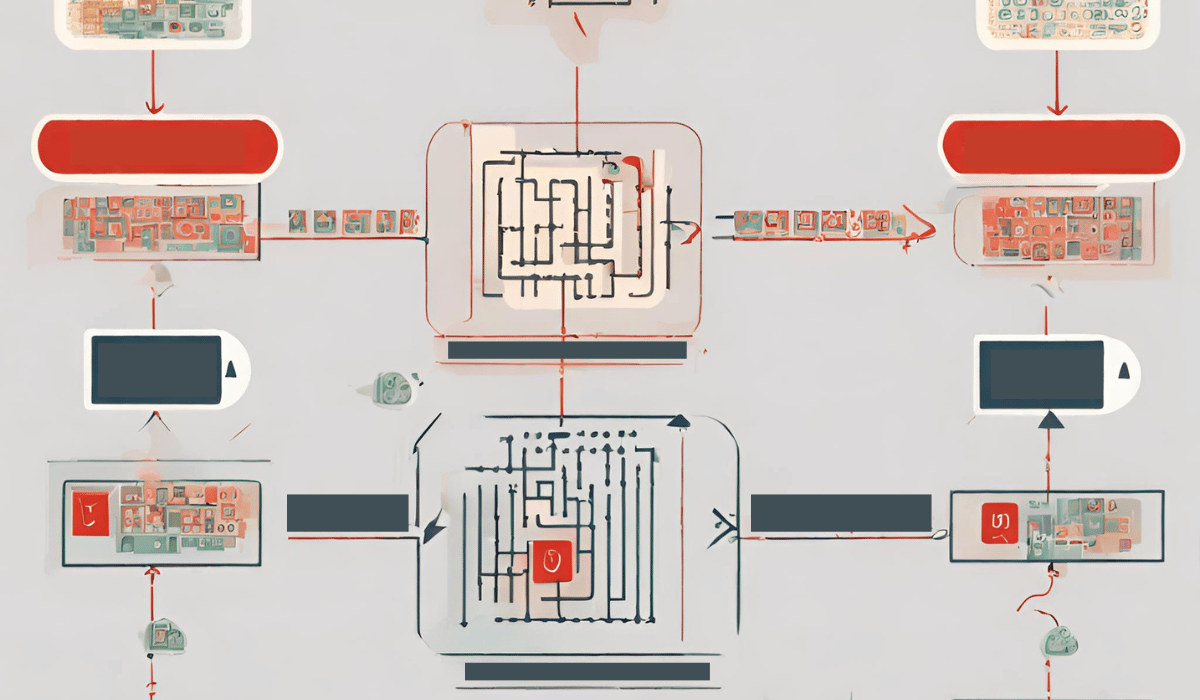
Triple DES (3DES) is a symmetric-key block cypher algorithm that uses three keys and three rounds of encryption to provide enhanced security compared to the original Data Encryption Standard (DES). The first step in 3DES is to encrypt the plaintext with one key using the original DES algorithm. The output of this operation is decrypted with a second key using the DES algorithm again. The output of this decryption is encrypted once more with the third and final key. This process results in a ciphertext that is more secure than standard DES due to its use of multiple keys and encryption rounds.
Description Of Advanced Encryption Standard (AES)
AES uses a block cipher technique where plaintext is divided into blocks of fixed size and then encrypted using a secret key. The most commonly used block size is 128 bits, but AES also supports block sizes of 192 and 256 bits. AES operates on rounds where each round consists of several steps that involve substitution, permutation, and mixing operations. The number of rounds depends on the key length: 10 rounds for a 128-bit key, 12 rounds for a 192-bit key, and 14 rounds for a 256-bit key.
Comparison Of 3DES And AES
3DES is a symmetric key algorithm that uses three rounds of DES (Data Encryption Standard) to encrypt data. It is slower than AES but has been around for longer and is still considered secure enough for certain applications. However, it is gradually being replaced by AES.
AES, on the other hand, is also a symmetric key algorithm that uses a block cipher. It was developed as a replacement for DES and offers stronger security with its variable key size options (128-bit, 192-bit or 256-bit). The use of block cipher makes it faster than 3DES while providing better protection against attacks.
While 3DES may still be useful in certain situations, such as legacy systems where upgrading to AES would be difficult or costly, AES should be the preferred choice for new systems due to its higher security and performance benefits.
Key Management In DES
To ensure the security of encrypted data in DES, it’s important to carefully manage keys. This includes generating strong random keys using a trusted source of entropy and securely distributing them to authorized users or systems. It also involves rotating keys periodically to mitigate the risk of key compromise or theft.
In addition, proper key management in DES involves implementing robust access controls and auditing mechanisms to monitor who has access to keys and how they’re being used. This helps prevent unauthorized access or misuse of keys that could compromise the security of sensitive data. By following best practices for key management in DES, organizations can help protect their valuable information from cyber threats and maintain trust with customers and stakeholders.
Future Of Data Encryption Standard
The Evolution Of Encryption Standards Beyond DES
The Data Encryption Standard (DES) was a popular encryption algorithm during the 1970s and 1980s. However, with the advancement of technology, it became vulnerable to brute-force attacks. As a result, new encryption standards were developed to provide better security.
One such standard is Advanced Encryption Standard (AES), which uses block cyphers to encrypt data. AES is currently considered one of the most secure encryption algorithms in use today and has been adopted by governments worldwide.
Another important development in encryption standards is Elliptic Curve Cryptography (ECC). This method uses elliptic curves instead of prime numbers for key exchange, resulting in smaller key sizes and faster computations compared to traditional public-key cryptography.
Quantum Computing And Its Impact On Encryption
Quantum computing is a rapidly developing technology that has the potential to revolutionize the way we process information. One of its most significant impacts could be on data encryption, which is used to protect sensitive information in transit and at rest. Traditional encryption relies on mathematical algorithms that are extremely difficult (if not impossible) for classical computers to solve. However, quantum computers can use their unique properties to break these algorithms much more easily.
This presents a significant challenge for the future of data security, as many current encryption methods will become vulnerable once large-scale quantum computers become widely available. As such, researchers are actively exploring new approaches to encryption that can withstand attacks from quantum computers. One promising solution is post-quantum cryptography (PQC), which uses different types of mathematical problems than traditional encryption and would be resistant to attacks from even the most advanced quantum computers.
The Future Of Encryption In A Rapidly Evolving Digital Landscape
The future of encryption will likely involve more complex algorithms capable of resisting attacks from quantum computers while still maintaining high levels of performance. Additionally, there will be a need for multi-layered security protocols that incorporate both hardware and software-based solutions to provide robust data protection. With data privacy regulations becoming stricter across various industries globally, companies must adopt more sophisticated encryption methods to ensure compliance.
FAQs
What Is The Difference Between DES And 3DES?
The Data Encryption Standard (DES) is a symmetric encryption algorithm that uses a 56-bit key to encrypt and decrypt data. IBM developed it in the 1970s and adopted it as the United States government standard for secure communications. However, with advances in computing power, DES became vulnerable to brute-force attacks, where an attacker could try all possible keys until finding the correct one.
To address the security issues of DES, triple DES (3DES) was introduced as a more secure variant. 3DES applies the DES algorithm three times using two or three different keys to provide stronger encryption. With this method, even if an attacker manages to break one layer of encryption, they still need to break through two more layers before accessing any sensitive data.
What Is The Key Size For The Data Encryption Standard(DES) Algorithm?
The key size for DES is 56 bits, which means that there are 2^56 possible keys. This may seem like a large number, but it can be easily cracked with modern computing power.
Can Des Be Cracked With Modern Computing Technology?
Modern computers can perform billions of calculations per second, making it easier for hackers to crack the encryption.
Is DES Still Used In Modern Encryption?
Although DES is no longer considered secure for use in high-stakes situations, it is still used in some applications where security is not a primary concern. One of the reasons why DES is still being used in modern encryption systems is because of its simple and efficient design. This means that DES can be easily implemented on older devices with limited processing power or storage capacity.
How Can I Ensure Proper Key Management In DES?
Ensure proper key management in DES through the use of a key management system. Such a system can help automate many processes involved in managing keys, including generating new keys, rotating old ones, and revoking compromised ones. Additionally, it can provide an audit trail that allows administrators to monitor who has accessed which keys and when.
Conclusion
The Data Encryption Standard (DES) is a widely used cryptographic algorithm that has existed for several decades. Despite its age, it offers robust security protection for sensitive data transmissions. However, with the increasing sophistication of cyber attacks, DES has become vulnerable to brute force attacks and other hacking techniques.
As such, organizations are advised to implement more advanced encryption systems like Advanced Encryption Standard (AES) or Triple DES (3DES) to secure their data effectively. Even though AES may have some weaknesses in specific use cases, it still provides better security than DES.
