Introduction to Google Sheets
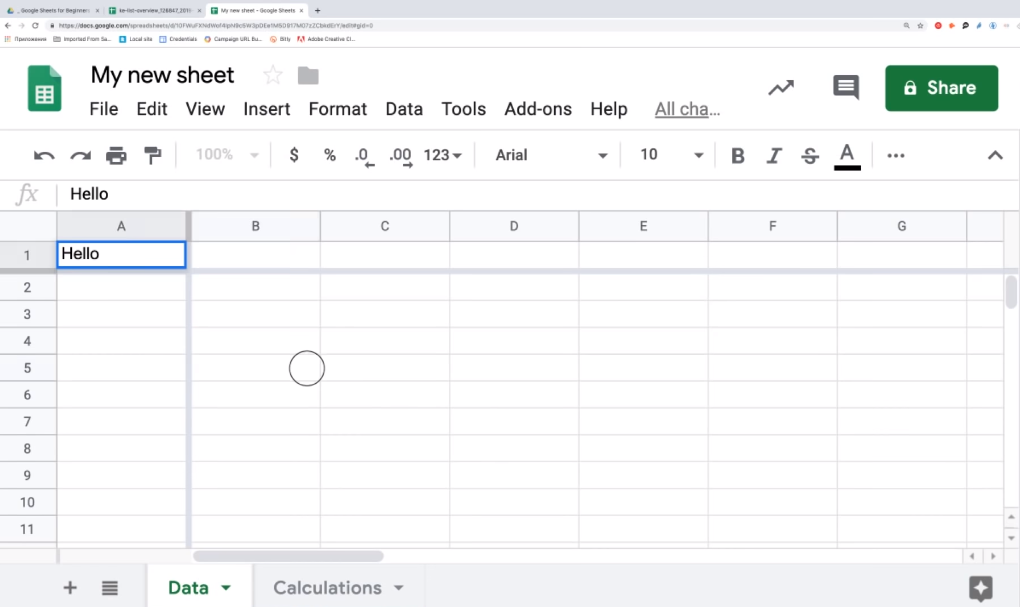
Google Sheets is a widely used cloud-based spreadsheet tool that allows users to create, edit and share spreadsheets online. It is part of the Google Drive suite of productivity tools and is accessible through any web browser on a desktop or mobile device. Google Sheets offers a range of features, including formulas, charts, data validation, and collaboration tools. It is a popular choice for individuals and businesses alike, with the ability to import and export data in a variety of formats.
Data Security Risks in Google Sheets
Google Sheets is a powerful tool for managing and analyzing data, but it’s important to be aware of the potential security risks involved. Here are some key considerations to keep in mind:
1. Access controls: Make sure to set appropriate access controls for your spreadsheets, limiting who can view, edit, or share them. This can help prevent unauthorized access or changes to your data.
2. Password protection: Consider using password protection for your spreadsheets, especially if they contain sensitive or confidential information.
Methods Used By Attackers To Compromise Data
1. phishing: Attackers often use phishing emails to trick users into revealing sensitive information, such as login credentials or financial data.
2. Malware: Malware can be used to gain unauthorized access to your computer or network, allowing attackers to steal data or install additional malicious software.
Strengthening Access Control
To strengthen access control and protect your sensitive data, you can consider implementing the following measures:
1. Use strong passwords: Ensure that all users have strong passwords that are difficult to guess. Passwords should be at least 8 characters long and include a combination of letters, numbers, and symbols.
2. Two-factor authentication: Consider implementing two-factor authentication, which requires users to provide a second form of identification, such as a code sent to their mobile device, in addition to their password.
Creating Strong User Accounts
To create strong user accounts, you can implement the following measures:
1. Use unique usernames: Encourage users to use unique usernames that are not easily guessable. Avoid using common usernames such as “admin” or “user”.
2. Enforce password policies: Set password policies that require users to create strong passwords. Passwords should be at least 8 characters long and include a combination of letters, numbers, and symbols.
3. Implement two-factor authentication.
Managing User Permissions
To manage user permissions, you can follow these steps:
1. Identify the different levels of access: Determine the different levels of access that users need based on their roles and responsibilities.
2. Create user groups: Group users based on their access requirements and assign permissions to each group.
3. Assign permissions: Assign permissions to each user group based on their level of access. For example, an administrator may have full access to all functions, while a regular user may only have access to certain features.
Tracking and Monitoring User Activity
4. Implement tracking and monitoring: Implement a system to track and monitor user activity. This will help identify any unauthorized access attempts or suspicious activity.
5. Regularly review access: Regularly review user access and permissions to ensure that they are still appropriate for their role and responsibilities.
6. Enforce strong passwords: Enforce strong password policies to prevent unauthorized access.
7. Provide training: Provide training to users on the importance of protecting sensitive information and the proper use of access privileges.
Protecting Data at Rest
Protecting data at rest is equally important as protecting data in transit. Here are some best practices to follow:
1. Encryption: Use encryption to protect sensitive data at rest. This ensures that even if the data is stolen, it cannot be accessed without the encryption key.
2. Access controls: Implement access controls to restrict access to sensitive data only to authorized personnel.
3. Secure storage: Store sensitive data in secure storage systems that are designed to protect against physical and logical attacks.
Encryption of Data
Encryption of data is a crucial step in protecting sensitive information from unauthorized access. Encryption is the process of converting plain text data into a coded form that can only be read by authorized individuals with the decryption key. This ensures that even if the data is intercepted, it cannot be read or understood by anyone who does not have the key.
Securing File Storage
Securing file storage is also an important aspect of protecting sensitive information. This can be achieved through various methods such as access controls, firewalls, and intrusion detection systems. Access controls ensure that only authorized individuals have access to the files, while firewalls and intrusion detection systems protect against unauthorized access attempts.
Physical Security In addition to logical security measures, physical security is also important for protecting sensitive information. This can include measures such as secure storage facilities, video surveillance, and access controls to physical locations.
Securing Data in Transit
When sensitive information is being transmitted between locations, it is important to ensure that the data is secure. This can be achieved through the use of encryption and secure communication protocols. Encryption ensures that the data is scrambled and unreadable to anyone who intercepts it, while secure communication protocols ensure that the data is transmitted only between authorized parties.
Utilizing HTTPS for Secure Connections
HTTPS is a widely used secure communication protocol that is used to encrypt data in transit between a website and its users. It is commonly used for online transactions, such as banking and e-commerce, as well as for securing login pages and other sensitive areas of a website. HTTPS uses SSL/TLS encryption to protect data in transit and prevent unauthorized access or interception. Websites that use HTTPS display a padlock icon in the address bar of the browser, indicating that the connection is secure.
Protecting Against Man-in-the-Middle Attacks
HTTPS is an essential tool for protecting against man-in-the-middle attacks, where an attacker intercepts the communication between the website and the user. With HTTPS, all data is encrypted, making it much harder for an attacker to intercept and read the data. Additionally, HTTPS uses digital certificates to verify the identity of the website, ensuring that the user is communicating with the intended website and not a fake one set up by an attacker.
Preventing Data Loss
Preventing data loss is crucial for any organization that handles sensitive information. One way to prevent data loss is to regularly back up all important data to a secure location. This ensures that if there is a system failure or a cyber attack, the data can be easily restored. It’s also important to implement strong access controls to ensure that only authorized individuals have access to sensitive data. This can include using multi-factor authentication, role-based access controls, and regular monitoring of user activity.
Regular Backups
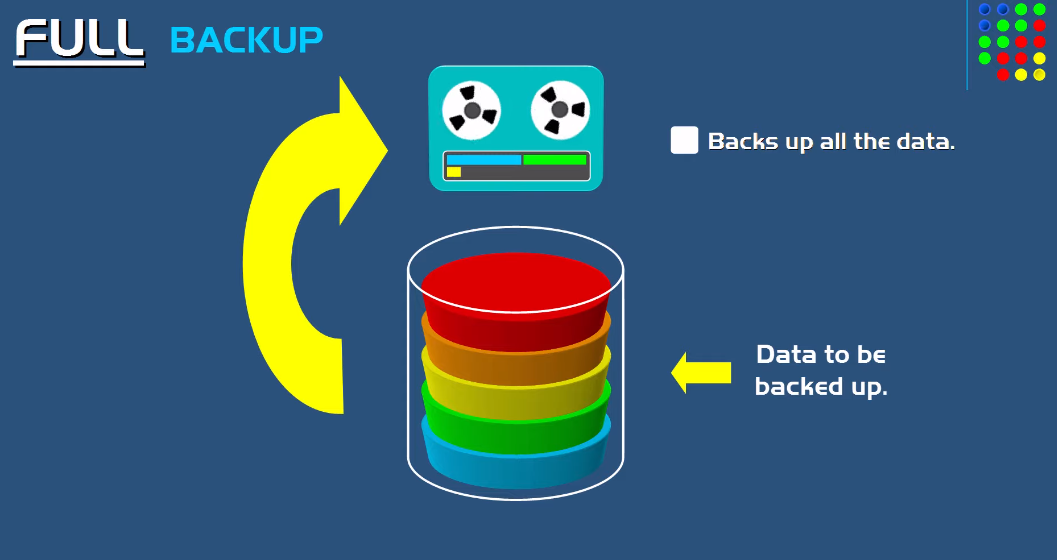
Regular backups of important data are crucial for preventing data loss in case of system failure or cyber-attack. It’s important to back up data to a secure location, such as an external hard drive or cloud storage service. This ensures that the data can be easily restored in the event of a disaster.
Version Control and Revision History
Version control and revision history are important tools for managing changes to documents and other files. They allow users to track changes, revert to previous versions, and collaborate on documents with multiple users. This can be especially useful in a business setting where multiple people may be working on the same document or project. By using version control and revision history, businesses can ensure that everyone is working from the same version of a document and that changes are properly tracked and documented.
Implementing Data Loss Prevention Measures
Data loss prevention measures are crucial for businesses to protect their sensitive and confidential information. These measures can include implementing firewalls, antivirus software, and encryption protocols to prevent unauthorized access to data. Additionally, businesses can train their employees on best practices for data security, such as using strong passwords, avoiding phishing scams, and being cautious when sharing information. Regular backups of important data can also help mitigate the risk of data loss.
Data Validation and Verification
Data validation and verification are crucial steps in ensuring the accuracy and reliability of data. Data validation involves checking whether the data entered is valid and conforms to specific rules and standards. This can include checking for correct data types, ranges, and formats. Verification, on the other hand, involves ensuring that the data entered is accurate and matches the source. This can be done through various methods such as double-entry verification, where two people independently enter the same data and compare the results.
Using Data Validation and Conditional Formatting
Data validation and conditional formatting are useful tools for ensuring data accuracy and consistency. Data validation can be used to set specific rules and constraints on the data that can be entered into a cell or range of cells. For example, you can set a rule that only allows numbers between 1 and 100 to be entered into a particular cell. Conditional formatting, on the other hand, allows you to format cells based on specific conditions or criteria.
Frequently Asked Questions (FAQs)
How often should I change my Google account password?
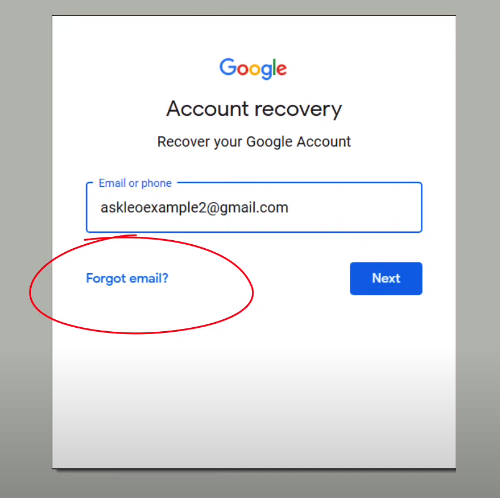
It is generally recommended to change your Google account password every six months to ensure the security of your account. It’s also a good idea to change your password immediately if you suspect that your account has been compromised.
Can I recover data that was accidentally deleted from Google Sheets?
Yes, you can recover data that was accidentally deleted from Google Sheets. Google Sheets has an “Undo” feature that allows you to undo your most recent action, including deleting cells or data. You can also check the “Version history” feature to see previous versions of your sheet and restore any deleted data from there.
Can I access Google Sheets offline to work on my data securely?
Yes, you can access Google Sheets offline by enabling offline access in your Google Drive settings. This allows you to work on your data securely without an internet connection. Any changes you make will be automatically synced to your account when you go back online. Keep in mind that some features may not be available offline, and you may need to manually save your changes before going offline.
