Definition And Significance of Big Data
Big data refers to large and complex datasets that cannot be processed using traditional data processing tools. These datasets typically contain massive amounts of unstructured, semi-structured, and structured data that are generated from various sources such as social media, sensors, and transactional systems. The significance of big data lies in its ability to provide insights and actionable information that can be used to inform business decisions, improve customer experiences, and drive innovation.
Understanding Privacy in Big Data
Big data has raised concerns about privacy as it often involves the collection and analysis of personal information. Privacy in big data can be protected by implementing measures such as data anonymization, encryption, and access controls. However, it is important to note that complete anonymity is often not possible in big data as even seemingly anonymous data can be re-identified through various techniques. Therefore, it is crucial for organizations to be transparent about their data collection and usage practices and to obtain informed consent from individuals.
Legal Framework for Privacy Protection
The legal framework for privacy protection varies by country and region. In the United States, privacy protection is primarily governed by sector-specific laws such as HIPAA for healthcare data and GLBA for financial data. Additionally, there are federal laws such as the Children’s Online Privacy Protection Act (COPPA) and the Electronic Communications Privacy Act (ECPA) that provide privacy protection for specific types of data.
Privacy Protection Techniques
Data Minimization
Data minimization is a privacy protection technique that involves collecting and retaining only the minimum amount of data necessary for a specific purpose. This technique helps to reduce the risk of data breaches and unauthorized access to personal information.
Access Control Mechanisms
Access control mechanisms are privacy protection techniques that restrict access to personal information to only authorized individuals or entities. This can involve the use of passwords, biometric authentication, and other security measures to ensure that only those who need access to the information can access it.
Encryption and Data Security
Encryption and data security are crucial privacy protection techniques that involve encoding personal information to prevent unauthorized access. Encryption algorithms are used to scramble data so that it can only be accessed by those who have the encryption key. This helps to ensure that even if personal information is intercepted, it cannot be read or used by unauthorized parties.
De-identification Techniques
De-identification techniques are another privacy protection method that involves removing or altering personal information to make it anonymous or unidentifiable. This can include techniques such as data masking, where certain parts of personal information are replaced with dummy data, or anonymization, where personal information is removed entirely. This helps to protect individuals’ privacy by preventing their personal information from being linked to their identity. Overall, a combination of these privacy protection techniques can be used to help ensure that personal information is kept safe and secure.
Privacy-Preserving Data Analysis
Privacy-preserving data analysis is a technique used to analyze data while keeping personal information confidential. This is particularly important in cases where sensitive information is being analyzed, such as in medical or financial data. One way to achieve privacy-preserving data analysis is through the use of encryption techniques, such as homomorphic encryption, which allows computations to be performed on encrypted data without the need to decrypt it. Another method is to use differential privacy, which adds random noise to the data to prevent the identification of individuals.
Auditing and Monitoring
Auditing and monitoring are important aspects of ensuring the integrity and security of data. Auditing involves reviewing and analyzing data to ensure that it is accurate and consistent, while monitoring involves actively tracking data to detect any unusual activity or potential security breaches. To effectively audit and monitor data, it is important to have robust data management systems in place, including access controls, logging, and reporting mechanisms. These systems can help to identify and address any issues with data accuracy or security promptly.
Privacy Best Practices for Individuals
Controlling Personal Information
One of the best practices for individuals to protect their privacy is to control their personal information. This includes being cautious about what information is shared online, such as on social media platforms, and avoiding giving out sensitive information to unknown or untrusted sources. It is also important to regularly review privacy settings on social media and other online accounts to ensure that only necessary information is being shared.
Secure Online Communication
Secure online communication is crucial to protect sensitive information from being intercepted by unauthorized parties. Using strong passwords and two-factor authentication can help prevent unauthorized access to accounts. Additionally, using secure communication channels such as encrypted messaging apps or virtual private networks (VPNs) can help protect information during transmission. It is also important to be cautious when clicking on links or downloading attachments from unknown sources, as these can be used to infect devices with malware or steal personal information.
Regular Data Backup
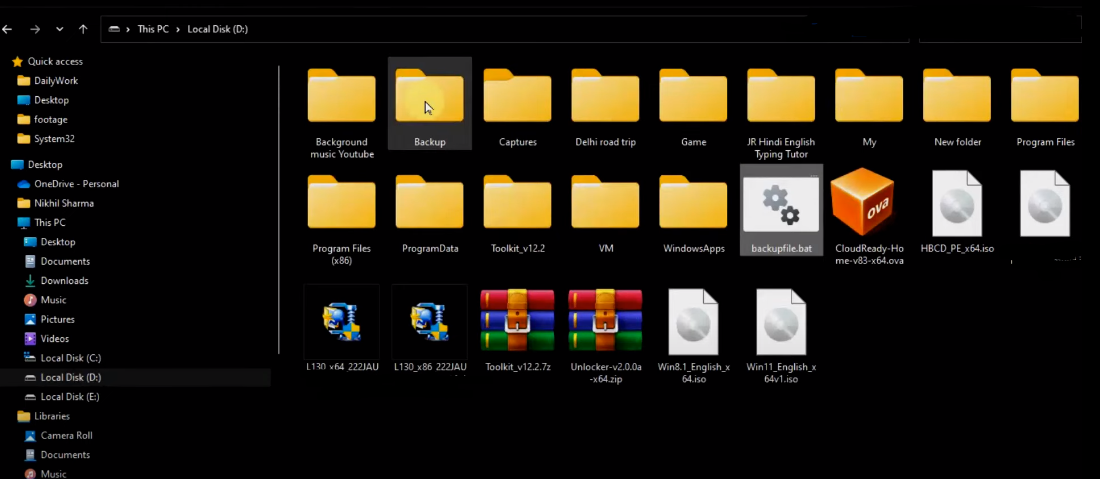
Regular data backup is crucial for protecting important information from loss or damage. It is recommended to back up data at least once a week or more frequently for critical data. Backups should be stored in a secure location, such as an external hard drive or cloud storage service, and should be encrypted to prevent unauthorized access. It is also important to test backups regularly to ensure that they can be restored in case of a data loss event.
Safe Internet Browsing
Safe internet browsing is essential for protecting your personal information and computer from viruses and malware. To ensure safe browsing, you should always use trusted antivirus software and keep it updated regularly. It is also recommended to use a virtual private network (VPN) to encrypt your online activity and prevent hackers from accessing your data. Additionally, avoid clicking on suspicious links or downloading attachments from unknown sources, as they may contain harmful software.
Managing Cookies and Tracking
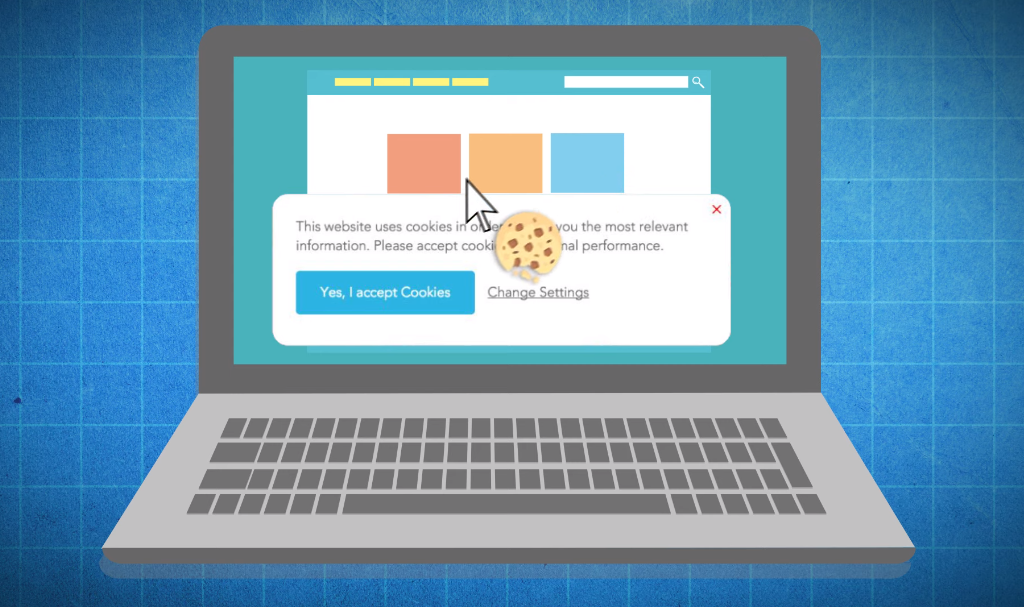
Cookies and tracking can be managed by adjusting your browser settings. Cookies are small files that websites store on your computer to remember your preferences and login information. You can choose to block all cookies or only accept them from trusted websites. Some browsers also offer a private browsing mode that doesn’t save your browsing history or cookies. Tracking refers to the collection of data about your online activity, which is often used for targeted advertising.
FAQs
What is the significance of privacy in big data?
Privacy is a significant concern in big data because the collection and analysis of large amounts of personal information can potentially lead to the violation of an individual’s privacy rights. As more and more data is collected, there is a risk that sensitive information such as personal details, financial information, and health records could be exposed or misused. Organizations need to implement strong privacy policies and security measures to protect individuals’ data and ensure that it is used only for legitimate purposes.
What are the legal requirements for protecting privacy in big data?
The legal requirements for protecting privacy in big data vary depending on the country and region. In the United States, the most comprehensive federal law governing data privacy is the General Data Protection Regulation (GDPR), which sets strict rules for how personal data must be collected, stored, and processed. Other countries have their privacy laws, such as the Personal Information Protection and Electronic Documents Act (PIPEDA) in Canada and the Privacy Act in Australia.
How can data minimization techniques help in privacy protection?
Data minimization techniques can help in privacy protection by reducing the amount of personal data that is collected, processed, and stored by organizations. This means that only the minimum amount of data necessary to achieve a specific purpose is collected, and any unnecessary or unrelated data is not collected or retained. By minimizing the amount of personal data that is stored, the risk of data breaches and unauthorized access to sensitive information is reduced.
What is the role of encryption in safeguarding privacy?
Encryption plays a crucial role in safeguarding privacy by converting sensitive information into an unreadable format that can only be deciphered by those with the necessary decryption key. This ensures that even if data is intercepted or stolen, it cannot be read or used by unauthorized individuals. Encryption is used to protect data both in transit and at rest, such as when it is stored on servers or in databases.
