Introduction:
Now that you have finally decided to start using Cloud Secure and that you are aware of how it benefits you, it is time for you to learn how exactly it works. Know that it does not involve any hard and fast rule of algorithm utilization or similar conditions. All you need to remember is your master password, which would your first step of setting up your cloud secure account. Ahead of that, it is all quick and easy but always remember to never lose your password, as it is almost impossible to recover it.
How to use Cloud Secure – Beginners guide to cloud security
Here are the basic steps to protect Cloud Accounts with the help of this software:
- Install the software on your device and create a Master Password.
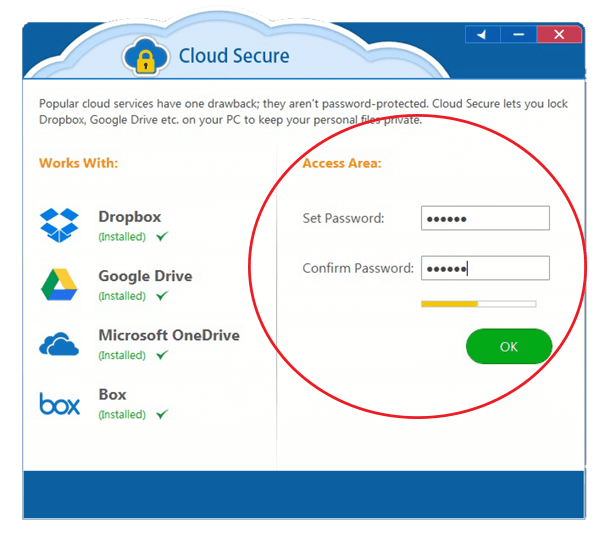
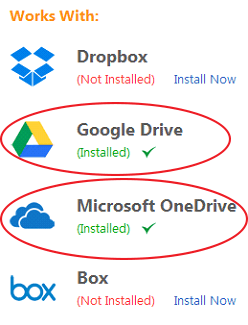
- You can protect multiple Cloud Accounts such as Dropbox, Microsoft OneDrive, Google Drive, & Box.
- Furthermore, login into your account to activate the protection for one or more Cloud Accounts.
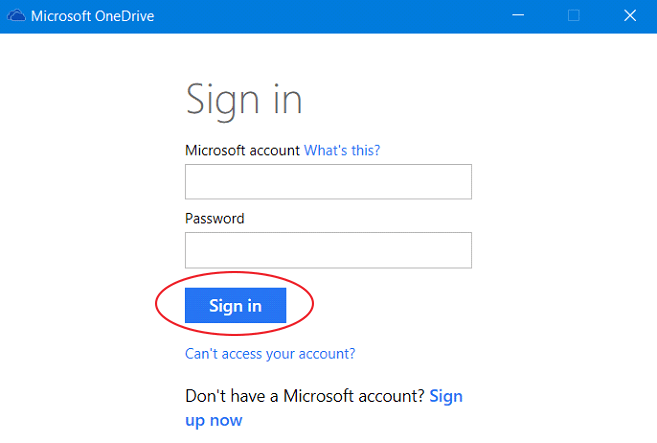
- The software will detect the installed Cloud Accounts on your device.
- You can turn the protection on for any Cloud Account by clicking on the “Lock” button.

- The remaining uninstalled Cloud Accounts can be downloaded by clicking on the “Install now” button.
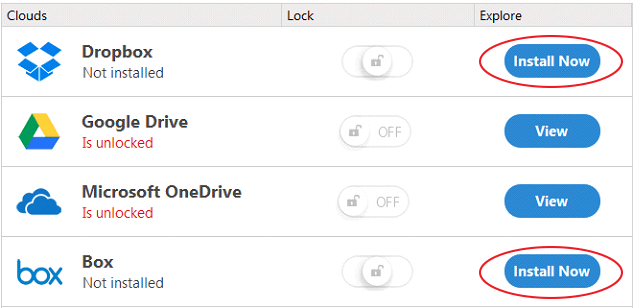
- Once the protection is on, it will get denoted by the color “green” while the insecure Cloud Accounts will be shown as “Google Drive is unlocked.”
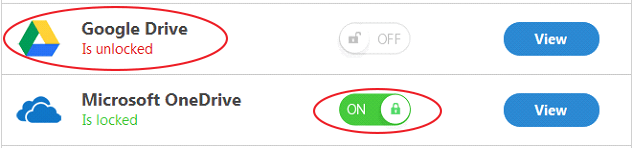
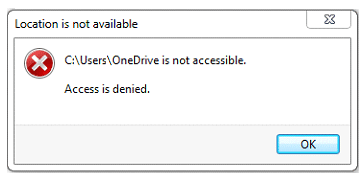
- Once the protection status for any Cloud Account is active, you cannot access that Account from its previous location (stored on your PC).
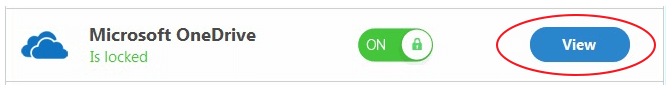
- To view the files in the Locked folder, Click on the “View” button that will open the respective Cloud Account in a protected view.
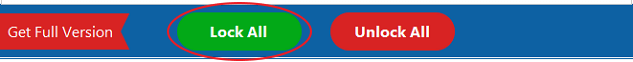
- To lock all the Cloud Accounts, you can click on the “Lock All” button.
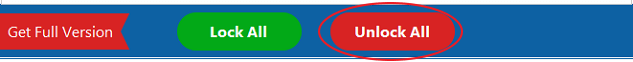
- In any case, you can unlock all the Cloud Accounts by clicking on the “Unlock All” button.
Verdict:
Beyond cloud secure’s security, there exists no hope of making the data in your cloud account safe. That does not mean the cloud storage accounts themselves are not having any security of their own, sure they have, but the standards they have set are quite breach-able today. Most of the profound hackers of the present can tear access or get through such security standards in a few days or even less. Hence, dependable security is highly important.

