Online anonymity is not absolute. While you can enhance your privacy using tools like VPNs and the Tor Browser, factors like data collection, social connections, and legal considerations can compromise your anonymity. Achieving complete online anonymity is a challenging goal, and using these tools responsibly to protect your digital footprint while staying within legal boundaries is important.
Understanding Online Anonymity

Online anonymity is concealing one’s identity while navigating the digital realm. It often involves using pseudonyms or masking personal information to protect privacy and avoid tracking. While the desire for anonymity is legitimate in many cases, it’s essential to recognize that online anonymity is a complex and elusive goal.
The Illusion of True Anonymity
Online platforms often allow users to remain anonymous by using pseudonyms or avatars, giving them a sense of security. However, it’s essential to recognize that this anonymity is often more illusory than real. When you create an account or engage in online activities, you leave digital footprints that can be traced back to you.
The Role of IP Addresses
One of the fundamental factors undermining online anonymity is the use of IP (Internet Protocol) addresses. Every device connected to the internet has a unique IP address, which can reveal your location and identity when accessed by the right authorities. VPNs (Virtual Private Networks) can mask your IP address to some extent, but they aren’t foolproof.
Why Choose Online Anonymity?
Protecting Personal Privacy
One of the primary reasons people choose online anonymity is to protect their personal information. When you browse the internet, various websites and online services collect data, ranging from your IP address to your browsing history.
Online tracking has become pervasive, with companies and advertisers monitoring your online activities to deliver targeted ads. Anonymous browsing makes tracking your behavior and preferences challenging for these entities, allowing you to maintain a semblance of privacy.
Expressing Opinions Freely
Online anonymity empowers individuals to express their opinions and ideas freely. Some fear reprisals or backlash for their views and beliefs, making anonymity a shield against potential consequences.
Sometimes, individuals may find it difficult to express themselves openly due to societal or cultural restrictions. Online anonymity provides a safe space to voice dissenting opinions or explore personal interests without fear of judgment or condemnation.
The Challenges of Staying Anonymous
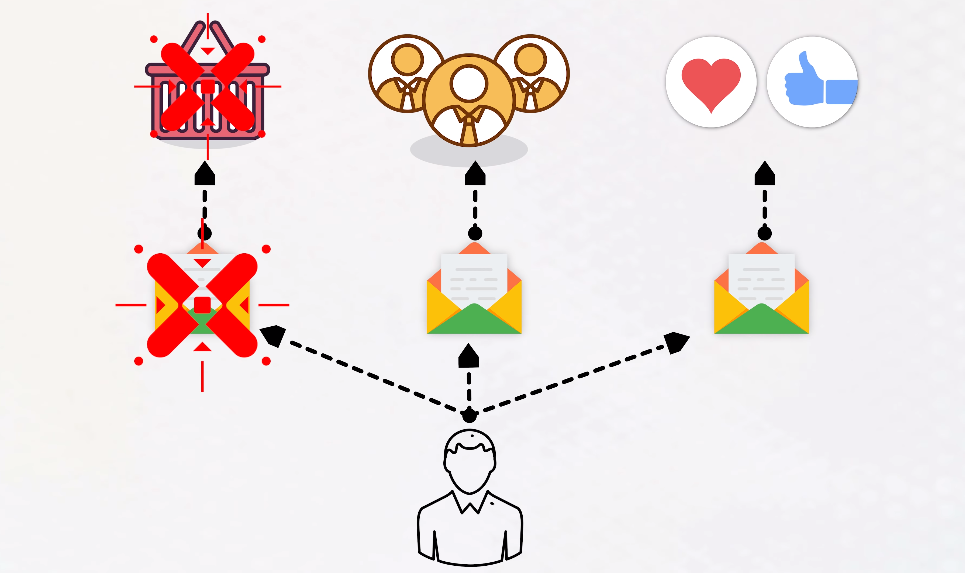
1. Data Collection by Websites and Services
Your activity leaves a digital footprint when you visit websites or use online services. Websites often collect data such as IP addresses, cookies, and browsing history, which can be used to identify you.
2. Social Media and Personal Connections
Social media platforms encourage users to create profiles and connect with friends and acquaintances. While you may use an alias, your connections and interactions can reveal your identity over time.
3. Legal and Ethical Considerations
The law may require websites and online services to disclose user information in certain situations, undermining the idea of complete anonymity. Ethical dilemmas may also arise when individuals engage in illegal activities online.
The Misconceptions about Anonymity
Anonymity vs. Privacy
While online anonymity aims to conceal your identity, privacy is about safeguarding your personal information. Even if you are anonymous, your data may still be vulnerable if you don’t take steps to protect it.
The Myth of Total Anonymity
Many individuals assume that they can be completely untraceable online. However, achieving absolute anonymity is challenging and often impossible, especially when facing determined adversaries with the right resources.
The Tools for Online Anonymity

1. Virtual Private Networks (VPNs)
What are VPNs? Virtual Private Networks, commonly known as VPNs, are powerful tools for enhancing online anonymity. They work by routing your internet traffic through encrypted servers in various regions. By doing so, they hide your real IP address and make it appear you are browsing from a different location.
How Do VPNs Enhance Anonymity?
- Masking Your IP Address: VPNs replace your IP address with that of the VPN server, making it difficult for websites and online services to trace your location or identity.
- Encryption: VPNs use encryption protocols to secure your internet traffic, preventing hackers or eavesdroppers from intercepting your data.
Considerations When Using VPNs
- Choose a Reputable Provider: Not all VPN providers offer the same level of security and privacy. Opt for a well-established, trustworthy VPN service.
- Server Locations: Select a VPN location that aligns with your privacy needs. Some countries have more stringent data retention laws than others.
2. Tor Browser
What is the Tor Browser? The Tor Browser is a specialized web browser that allows you to access the internet while preserving your anonymity. It works by routing your traffic through a network of volunteer-operated servers, making it challenging for anyone to trace your online activities.
How Does Tor Enhance Anonymity?
- Routing Through Multiple Servers: Tor routes your internet traffic through several servers, ensuring your online footprint is obfuscated.
- Access to the Dark Web: While not its primary purpose, the Tor Browser also provides access to the dark web, a realm known for its heightened anonymity.
Considerations When Using Tor
- Slower Speeds: Due to the multiple server hops, browsing with Tor can be slower than using a standard browser.
- Caution on the Dark Web: The dark web can be risky, so exercise extreme caution if you choose to explore it.
3. Encryption Services
What Are Encryption Services? Encryption services are essential tools for securing your communication and data. They ensure that your messages and files are scrambled and can only be deciphered by the intended recipient.
How Do Encryption Services Enhance Anonymity?
- Protecting Your Messages: Services like Signal and WhatsApp offer end-to-end encryption, meaning only you and the person you’re communicating with can read the messages.
- Securing Your Files: Encryption tools like VeraCrypt allow you to encrypt files and folders on your device, preventing unauthorized access.
Considerations When Using Encryption Services
- Use Strong Passwords: Your encryption is only as strong as your password. Create complex, unique passwords for added security.
- Verify Encryption: Ensure your services have strong encryption features and have been independently audited for security.
The Limits of Online Anonymity
1. Technical Vulnerabilities
Even with anonymity tools, vulnerabilities in software or user errors can expose your identity. It’s crucial to stay updated and follow best practices.
2. Metadata and Behavioral Patterns
Metadata, such as the timing and frequency of your online activities, can reveal patterns that may lead to the identification of an anonymous user.
The Verdict on Online Anonymity
Though valuable in certain situations, online anonymity is not an impenetrable shield. It can somewhat protect your identity, but it’s not a guarantee of absolute secrecy. Users should be aware of the risks and limitations associated with online anonymity and exercise caution while navigating the digital landscape.
Conclusion
In the internet age, being anonymous online is a complex and multifaceted concept. While it offers a degree of protection, it’s essential to remember that true anonymity is often elusive. The digital footprints we leave behind and advances in technology and data collection can compromise our online identity. Therefore, it’s crucial to approach online activities with vigilance, privacy tools, and awareness of the limitations of online anonymity.
FAQs
Can I truly hide my identity online?
Achieving complete anonymity online is exceedingly difficult. Even with tools like VPNs and Tor, determined entities may uncover your identity through various means.
Are there legal repercussions for illegal activities conducted anonymously online?
Yes, engaging in illegal activities online can have legal consequences. Law enforcement agencies can employ advanced techniques to track down individuals who commit crimes while attempting to remain anonymous.
What steps can I take to enhance my online privacy?
To enhance online privacy, use encrypted messaging apps, employ strong and unique passwords, enable two-factor authentication, and be cautious about sharing personal information online.
Are there any situations where online anonymity is genuinely effective?
Online anonymity can effectively protect your identity from casual observers and maintain privacy in everyday online activities. However, it may not withstand determined efforts to unveil your identity.
How can I balance the benefits of online anonymity with the risks?
To balance online anonymity and risk mitigation, use privacy tools like VPNs and encrypted messaging apps and exercise caution when sharing personal information and engaging in online activities. Stay informed about evolving online threats and technologies.
